Technical Differences between AES vs RSA Encryption
Encryption safeguards data confidentiality and integrity. Advanced Encryption Standard (AES) and Rivest-Shamir-Adleman (RSA) are prominent encryption algorithms with distinct technical differences. AES is a symmetric-key algorithm, using the same key for encryption and decryption, operating on fixed data blocks through substitution and permutation.
Conversely, RSA is an asymmetric-key algorithm, utilizing separate public and private keys based on the difficulty of factoring large integers. AES excels in efficient data encryption, while RSA's strength lies in secure key exchange and digital signatures.
Understanding their underlying principles, mathematical operations, and practical applications is crucial for implementing appropriate encryption solutions that meet specific security requirements.
Key Takeaways
- AES and RSA are both widely used encryption algorithms but have different strengths. RSA is best for encrypting small amounts of data, while AES excels at bulk encryption.
- RSA relies on asymmetric (public/private) keys, while AES uses symmetric keys. This impacts their encryption/decryption speed and methodology.
- AES is faster at both encrypting and decrypting data compared to RSA. But RSA allows for digital signatures and private key distribution.
- AES is better suited for bulk data encryption, while RSA is better for encrypting passwords, keys, and other small pieces of data.
- Both AES and RSA have high security if large enough key sizes are used. AES-256 is considered practically unbreakable by brute force.
- Many systems use a hybrid approach with RSA for key distribution and AES for bulk data encryption. This provides both the security of RSA with the speed of AES.
Head-to-Head Comparison Between AES vs RSA Encryption
| Feature | AES | RSA |
| Type of cryptography | Symmetric (Private key) | Asymmetric (Public key) |
| Key length | 128, 192, or 256-bit | Minimum 2048-bit recommended |
| Encryption speed | Very fast | Slow |
| Decryption speed | Very fast | Slow |
| Scalability | Bulk data encryption | Only small amounts of data |
| Digital signatures | No | Yes |
| Key distribution | No | Yes |
| Forward secrecy | Yes, with ephemeral keys | No |
| Hardware acceleration | Widespread support | Less support |
| Key generation | Simple and fast | Complex and slow |
| Security level | Very high (AES-256) | High with large keys |
| Common applications | Disk encryption, network encryption | Encrypting passwords, keys, signatures |
How AES Encryption Works
Unlike RSA, AES relies on symmetric cryptography. This means it uses the same cryptographic key to both encrypt and decrypt data. AES also operates on fixed block sizes of 128 bits.
Here is a basic overview of how AES encryption works:
- The sender and recipient agree on an AES key to use for encryption/decryption. This is known as a shared secret.
- The plaintext data is divided into 128-bit blocks. If needed, the last block will be padded.
- Encryption applies a series of substitutions and transformations to each block using the AES algorithm and secret key. This produces the encrypted ciphertext.
- The ciphertext blocks are transmitted to the recipient.
- Using the same shared AES key, the recipient decrypts each ciphertext block to recover the original plaintext.
The security of AES relies on the secrecy of the key and the complexity of the AES block substitutions/transformations.
Also Read: What is AES 128-Bit Encryption?
AES Keys
AES supports key sizes of 128, 192, or 256 bits. 128-bit keys are the minimum, but 256-bit provides the strongest security. The larger key sizes add more permutations to the transformations.
Ideally, AES keys should be randomly generated for each encryption process. Keys should never be reused where possible.
AES Encryption Process
The AES encryption flow consists of four main functions applied to each 128-bit block:
- SubBytes- Non-linear byte substitutions using a substitution table. Makes encryption resistant to analysis.
- ShiftRows- Circular shifting of row bytes to scramble and diffuse bits.
- MixColumns- Mathematical column mixing operation to further diffuse bits.
- AddRoundKey- A simple XOR between the block and a round key derived from the original AES key.
Decryption uses the inverse functions in reverse order. The key schedule algorithm generates round keys from the main AES key.
How RSA Encryption Works
RSA gets its name from its creators - Rivest, Shamir, and Adleman who publicly described the algorithm in 1977. It relies on asymmetric cryptography and key pairs.
Here's a quick overview of how RSA encryption works:
- Each user generates a public/private key pair. The private key is kept secret, while the public key can be widely distributed.
- To encrypt a message, the sender retrieves the recipient's public key and uses it to encrypt the data.
- The encrypted data can only be decrypted using the recipient's unique private key.
This asymmetric approach allows for secure distribution of encrypted data without having to securely exchange a symmetric key beforehand. Anybody can encrypt data using the public key, but only the private key holder can decrypt it.
RSA Keys
RSA keys consist of a public exponent and modulus along with a private exponent. The security of RSA relies on the difficulty of factoring large prime numbers.
For adequate security, RSA keys should be at least 2048 bits long today. Some recommendations go up to 3072-bit keys for extremely sensitive data.
RSA Encryption Process
The RSA encryption process consists of three main steps:
- Key Generation- The public keys and private keys are generated using very large prime numbers and complex mathematical operations.
- Encryption- The plaintext data is encrypted using the recipient's public key, undergoing modular exponentiation with the public exponent. This produces the encrypted ciphertext.
- Decryption- The ciphertext is decrypted using the recipient's private key, reversing the modular exponentiation process. This recovers the original plaintext.
This approach allows anyone to encrypt data using the public key, but only the private key holder can decrypt it.
Comparing Strengths of RSA and AES
Now that we've looked at how AES and RSA work at a high level, let's compare some of their relative strengths and weaknesses.
Factorization vs Brute Force
The primary strength of RSA is reliance on factoring large primes. There are no known efficient algorithms to factor large prime numbers. This means brute force is the best-known attack.
AES strength relies on key size. A brute-force attack needs to try all possible key permutations. Larger key sizes exponentially increase the permutations.
Asymmetric vs Symmetric Keys
RSA uses asymmetric public/private keys while AES relies on symmetric key encryption.
Asymmetric keys allow RSA to provide functionality that AES cannot match like digital signatures and private key distribution.
But symmetric cryptography is faster than asymmetric cryptography. AES encryption/decryption is much quicker than RSA.
Bulk Encryption
Given its faster performance, AES excels at bulk encrypting large amounts of data. Streaming ciphers allow for AES encryption of near limitless data.
RSA encryption becomes unworkable for large data sets due to its computational intensity. It's better suited for small pieces of data.
Security
Both RSA using large enough key pairs and AES with 256-bit keys are considered highly secure and resistant to brute force attacks with modern computing.
AES-256 is specified to provide up to 256 bits of security strength. Breaking it by brute force requires astronomical amounts of computing power.
Encryption Speed
As previously mentioned, AES is much faster at encrypting and decrypting data compared to RSA.
For example, AES-256 operates at least 100x faster than 2048-bit RSA on similar hardware. Some benchmarks show AES-256 outperforming RSA by up to 5000x for encrypting larger amounts of data.
Also Read: Code Signing vs. SSL Certificate
Ideal Use Cases for RSA and AES
Given their different strengths, here are the ideal use cases where AES and RSA excel:
RSA Use Cases
- Encrypting asymmetric cryptography keys for transmission
- Encrypting passwords, certificates, and other small pieces of data
- Providing digital signatures to verify authenticity and integrity
- Generating session keys for symmetric encryption
- Securely distributing private keys and sharing secrets
AES Use Cases
- Bulk encryption of sensitive data at rest and in transit
- Disk and full disk encryption
- Database field encryption
- Encrypting website traffic and sensitive communications
- Providing symmetric encryption for apps and services
- Streaming cipher for real-time communications encryption
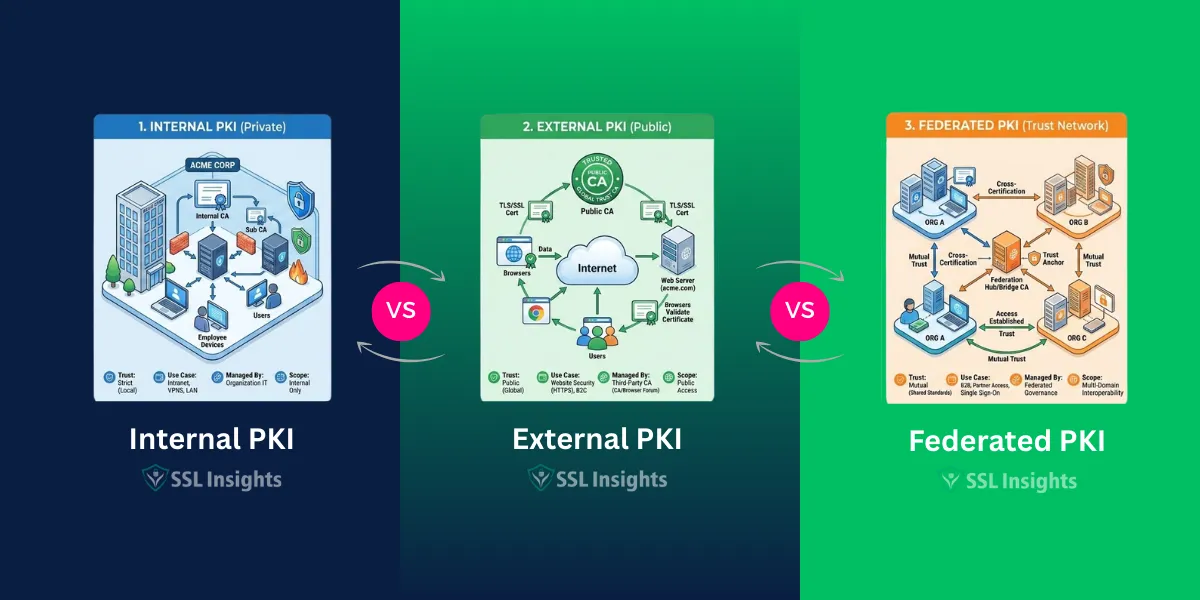
PKI enables secure e-commerce, protected communications, and robust system accessibility controls.
Hybrid Cryptography Systems
Today, many robust cryptography systems take a hybrid approach to leverage both AES and RSA.
This typically involves using RSA for the asymmetric components like digital signatures, key distribution, and exchanging secret keys. AES is then used for fast bulk data encryption and stream ciphers.
For example:
- RSA can generate and exchange a symmetric AES key for encrypting chat/messaging sessions
- Email encryption uses RSA for signatures and secret key exchange, AES for encrypting the email contents
- Websites use RSA certificates and keys for the SSL/TLS handshakes, then AES encryption takes over for the session data streams.
By combining AES and RSA, developers get the best of both worlds - RSA's secure key distribution and authentication with AES speed and data encryption power.
Summary: AES Encryption vs RSA Encryption
In summary, AES and RSA encryption algorithms differ significantly in their underlying principles and implementations. AES is a symmetric-key algorithm, faster for bulk data encryption, while RSA is an asymmetric-key algorithm, better suited for secure key exchange and digital signatures.
AES offers multiple key lengths, while RSA's security relies on the difficulty of factoring large prime numbers. Understanding these technical differences is crucial for selecting the appropriate encryption method based on performance, security requirements, and use case scenarios.
FAQs About AES Encryption vs RSA Encryption
Is RSA or AES more secure?
Both implementers properly implement AES and RSA with adequate key sizes, making them highly secure. Current computing considers AES-256 practically unbreakable by brute force. Factorization also finds 2048+ bit RSA keys extremely difficult to crack.
Is AES faster than RSA?
Yes, AES is significantly faster than RSA for both encryption and decryption. Benchmarks show AES-256 operating over 100x faster than a 2048-bit RSA key for small data. For bulk data, AES can outperform RSA by 5000x or more.
Does RSA use asymmetric keys?
Yes, RSA relies on asymmetric (public/private) key pairs. Anyone can encrypt data using the public key, but only the private key holder can decrypt it. This allows RSA to enable digital signatures and private key distribution.
Does AES use symmetric keys?
AES uses symmetric cryptography - this means the same key is used for both encryption and decryption. Symmetric ciphers allow for much faster performance than asymmetric cryptography.
Can RSA encrypt large amounts of data?
No, RSA encryption becomes unworkable for encrypting large data sets due to its computational complexity. RSA is better suited to encrypting small pieces of data like keys, passwords, and digital signatures.
Is AES better for bulk encryption?
Yes, AES excels at bulk encrypting large amounts of sensitive data thanks to its symmetric key approach. Streaming modes like GCM allow AES to encrypt essentially unlimited amounts of data.
What key sizes are recommended for RSA and AES?
For RSA, cryptographers recommend a minimum 2048-bit key, but 3072 bits or larger keys protect sensitive data better. For AES, experts consider a 256-bit key size unbreakable for the foreseeable future.
Can RSA and AES be used together?
Yes, many cryptosystems take a hybrid approach using RSA for digitally signing and exchanging keys paired with AES for fast bulk data encryption. This harnesses the security of RSA with the speed of AES.