Understanding Symmetric Encryption
Encryption is a method of scrambling data so that only authorized parties can access it. It has become an essential tool for protecting sensitive information in today's digital world. Symmetric encryption is one of the most basic forms of encryption and a good starting point for anyone new to encryption.
In symmetric encryption, the same cryptographic key is used to encrypt and decrypt the data. This differs from asymmetric encryption, where two different keys are used. The symmetric key must be known to both the sender and the receiver to securely share the encrypted data.
By the end of this guide, you will have a solid understanding of this fundamental encryption method and its role in securing data.
How Symmetric Encryption Works
Symmetric encryption uses a secret key to transform plaintext into ciphertext. It provides confidentiality but not authenticity. The general steps are:
- Sender and receiver agree on a secret key. This key should be generated randomly and kept private.
- Sender encrypts the plaintext using the secret key. This produces the ciphertext.
- Sender transmits the ciphertext to the receiver via an insecure channel.
- Receiver decrypts the ciphertext back into plaintext using the same secret key.
The secret key plays a crucial role. It enables encryption and decryption. A strong key means the ciphertext is computationally infeasible to break. Weak keys jeopardize security.
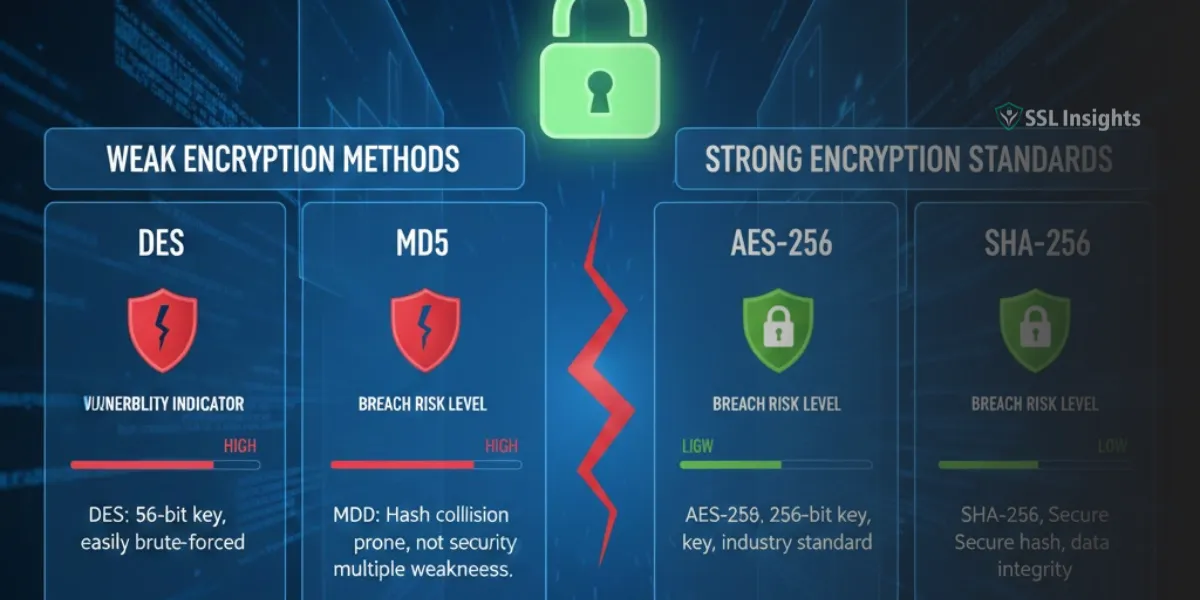
The encryption and decryption steps use an encryption algorithm. This is a cryptographic function using the key. It should be irreversible to prevent decryption without the key. Common symmetric algorithms include AES, Blowfish, RC4, DES and 3DES.
Symmetric encryption provides confidentiality but not authenticity or integrity. Additional mechanisms like message authentication codes (MACs) should be used to verify authenticity and integrity.
Types of Symmetric Encryption Algorithms
There are two main classes of symmetric encryption algorithms:
Block Ciphers
A block cipher encrypts fixed size blocks of plaintext at a time. For example, AES encrypts 128-bit blocks. Popular block cipher algorithms include:
- AES (Advanced Encryption Standard): The most widely used algorithm today. AES is fast, secure and comes in key sizes of 128, 192 or 256 bits.
- Blowfish: A strong 64-bit block cipher. It is faster than 3DES. Blowfish is public domain.
- 3DES (Triple Data Encryption Algorithm): A 64-bit block cipher that uses the DES algorithm three times. It offers stronger security than standard DES.
- DES (Data Encryption Standard): The original block cipher standardized in the 1970s. It encrypts 64-bit blocks with a 56-bit key. DES is now considered insecure.
Stream Ciphers
A stream cipher encrypts individual bits or bytes of plaintext at a time. Some examples include:
- RC4: A widely used stream cipher that is simple and fast in software. RC4 was initially a trade secret but was leaked in 1994.
- ChaCha20: A modern stream cipher designed for high performance. It is built on a pseudorandom function based on the ChaCha block cipher.
- Salsa20: A precursor to ChaCha20 with similar design principles.
Stream ciphers are generally faster than block ciphers in software. Block ciphers may be preferred for hardware implementations.
Uses of Symmetric Encryption
Symmetric encryption has many applications including:
- Encrypting Data at Rest: Data stored on devices is protected using a locally managed symmetric key. For example, BitLocker on Windows uses AES encryption.
- Secure Communication: Symmetric keys are used to encrypt communications like TLS sessions, VPN tunnels, wireless connections, etc. A key exchange protocol sets up the shared key.
- Database Encryption: Fields containing sensitive data can be encrypted in the database using a symmetric algorithm and key.
- Full Disk Encryption: The entire contents of a disk or storage device can be encrypted with a locally managed key.
- Provide Data Confidentiality: The primary goal of symmetric encryption is keeping data private from unauthorized access.
- Protect Master Keys: An asymmetric key pair used in public key encryption is often encrypted with a symmetric key for added security.
- Secure Backups: Backup files are ideal candidates for encryption using a symmetric key.
- Generate Cryptographic Hashes: The key is used to initialize variables within cryptographic hashing algorithms like SHA-2 or Blake2.
Pros and Cons of Symmetric Encryption
Advantages of Symmetric Encryption
- Faster than Asymmetric Encryption: Symmetric algorithms are optimized for speed in both software and hardware. They require less computational resources.
- Scales Efficiently: A single key can encrypt large amounts of data. The key size stays constant regardless of the data size.
- Provides Confidentiality: Strong symmetric ciphers make it computationally infeasible to recover the plaintext without the key.
Drawbacks of Symmetric Encryption:
- Key Distribution is a challenge: Sender and receiver must securely share the symmetric key to communicate. This usually requires asymmetric encryption.
- Risk of Compromised Keys: If the key is compromised, all data encrypted with it is compromised. Key management is crucial.
- No Authenticity: Symmetric encryption alone does not verify the authenticity or integrity of data. Additional mechanisms like MACs are needed.
- Vulnerable to Brute Force Attacks: Keys must be long enough to make exhaustive key searches infeasible for attackers.
Best Practices for Using Symmetric Encryption
Follow these best practices when using symmetric encryption:
- Use strong, standard algorithms like AES or ChaCha20. Avoid outdated algorithms like DES.
- Generate keys randomly using a cryptographically secure pseudo-random number generator.
- Choose sufficiently long key sizes (e.g. 256-bit keys for AES) for your security needs.
- HMAC is recommended over cipher block chaining as the MAC algorithm.
- Use different, unrelated keys for different purposes. Never reuse the same key.
- Store keys securely using a key management system or hardware security module (HSM).
- Automatically rotate keys regularly to limit exposure over time.
- Have strict key access policies limiting access to authorized persons only. Enforce access controls.
- Combine symmetric encryption with asymmetric encryption for key exchange and signatures.
- Properly implement authenticated encryption modes like GCM or EAX for message integrity.
- Follow key security hygiene by avoiding transmission in the clear, weak storage protections, etc.
Conclusion
Symmetric encryption provides foundational data protection capabilities through the use of shared secret keys. It enables confidentiality through standard algorithms like AES, Blowfish, RC4, etc. Symmetric ciphers are much faster than asymmetric ciphers and scale to large data sizes with a fixed key length.
However, symmetric encryption has drawbacks like challenging key distribution and lack of authenticity. It should be combined with additional mechanisms to construct a robust cryptosystem. Proper implementation and key management practices are critical for security.
For many real-world applications, hybrid cryptosystems using symmetric and asymmetric encryption provide the right blend of usability, speed and security. By following best practices and keeping keys secure, symmetric encryption can safely protect sensitive data at rest and in transit.
Frequently Asked Questions
What are the main differences between symmetric and asymmetric encryption?
Symmetric encryption uses the same key to encrypt and decrypt. Asymmetric encryption uses different public and private keys. Symmetric is much faster while asymmetric enables broader key distribution.
Is symmetric encryption secure?
Yes, modern algorithms like AES and systems like GCM authenticated encryption are considered highly secure when implemented correctly using sufficiently long key sizes. The main security risk is compromised keys.
What key sizes should be used today for symmetric encryption?
AES-128 is secure against brute force attacks. AES-256 provides an extra margin of safety against future cryptanalysis. For general purposes, AES-256 is recommended.
Does symmetric encryption provide authenticity?
Symmetric encryption alone only provides confidentiality. Authenticity is achieved in practice by adding message authentication codes (MACs) along with the ciphertext.
How are symmetric keys distributed securely?
Key exchange protocols that use asymmetric encryption like RSA or Diffie-Hellman can be used to securely establish a shared symmetric key between parties.