Understanding the Advanced Encryption Standard (AES)
Encryption is the process of encoding data or information to prevent unauthorized access. AES (Advanced Encryption Standard) 128 bit is a symmetric key encryption algorithm widely used to protect sensitive data.
Key Takeaways
- AES 128-bit encryption is a standard encryption algorithm adopted by the US government and organizations worldwide to protect confidential data.
- It uses a 128-bit fixed length key and a block size of 128 bits during encryption and decryption.
- AES 128 bit provides very strong security with its longer key size making it resistant to brute force attacks.
- The encryption algorithm goes through 10 rounds of substitution, transposition, and mixing operations on the input data block.
- Though theoretically hackable, there are no known successful attacks against AES 128 bit, so it is considered highly secure.
- AES 128 bit is used to encrypt data in transit and data at rest across many applications like documents, backups, databases, payment systems etc.
What is AES 128 Bit Encryption?
AES (Advanced Encryption Standard) is a symmetric key encryption algorithm standardized by NIST (National Institute of Standards and Technology) for encrypting electronic data to ensure its confidentiality.
AES 128 bit is one of the AES algorithms that uses a 128-bit fixed length key to encrypt and decrypt data in blocks of 128 bits.
Some key properties of the AES 128-bit cipher:
- Symmetric algorithm: Uses the same secret key for encryption and decryption.
- Block cipher: Encrypts and decrypts data in fixed size blocks of 128 bits.
- 128 bits key: Uses 128-bit secret key for encryption and decryption.
- 10 rounds: Data goes through 10 rounds of mathematical operations during encryption.
- Very high security: Provides strong confidentiality due to its security design.
How AES 128 Bit Encryption Works?
The AES 128-bit encryption algorithm works by repeating multiple rounds of substitution, transposition, and mixing operations on the plaintext input data block to produce the final encrypted ciphertext output.
The key steps are:
- KeyExpansion: The 128-bit input key is expanded to generate round keys for each round.
- Initial Round: An initial AddRoundKey operation is done by XORing the plaintext block with the first-round key.
- Main Rounds: The data then goes through 10 rounds of four operations: SubBytes, ShiftRows, MixColumns, and AddRoundKey.
- Final Round: A final round with three operations: SubBytes, ShiftRows, and AddRoundKey.
- Ciphertext: The output of the final round is the encrypted ciphertext.
This sequence of mathematical operations introduces diffusion and confusion at each round to thoroughly scramble the plaintext into random looking ciphertext.
Also Read: AES Encryption vs RSA Encryption
What Happens during AES 128-bit Encryption: A Detailed Process
Let's look at what happens during AES 128-bit encryption in more detail:
1. Key Expansion: The first step is to take the 128-bit secret key and expand it into 11 128-bit round keys using Rijndael's key schedule.
2. Initial Round:
- The plaintext data block is XORed with the first-round key to produce an intermediate ciphertext block.
- This initial AddRoundKey step provides diffusion by spreading the influence of each plaintext bit over many ciphertext bits.
3. Main Rounds (10 rounds)
Each round performs four operations on the intermediate ciphertext block:
- SubBytes: A non-linear substitution operation that substitutes each byte using a lookup table called an S-box. This provides confusion.
- ShiftRows: A transposition operation that shifts the rows of the state matrix by different offsets.
- MixColumns: A linear mixing operation that mixes the four bytes of each column using matrix multiplication over a Galois field.
- AddRoundKey: Each round key is XORed with the intermediate state. This provides diffusion across the block.
4. Final Round
The final round repeats three operations:
- SubBytes
- ShiftRows
- AddRoundKey
5. Ciphertext: Output of the final round is the 128-bit ciphertext.
This sequence of substitution, permutation, and key mixing introduces sufficient complexity to make AES highly resistant to cryptanalysis.
Why Use AES 128 Bit Encryption?
Here are some key reasons why AES 128-bit encryption is widely used to secure sensitive data:
- Strong security: Provides very robust protection due to its security design with 10 rounds, 128-bit keys, and complex mathematical operations.
- Resists brute force attacks: A 128-bit key has 3.4 x 10^38 possible keys making it impossible to crack by brute force.
- Wide adoption: AES is standardized by NIST and used worldwide by corporations and governments to protect classified information.
- Speed: Software and hardware implementations are fast making AES suitable for encrypting large amounts of data.
- Open algorithm: AES is open and available worldwide unlike proprietary algorithms that can be suspect.
- NIST validation: Stringent validation and testing by NIST confirming AES security against attacks.
- Flexibility: AES allows key sizes of 128, 192 and 256-bit to balance security and speed.
- Used extensively: Implemented many applications like documents, backups, databases, payment systems.
Is AES 128-Bit Encryption Hackable?
Though extremely robust, AES 128-bit encryption is theoretically vulnerable to brute force attacks since it relies on a fixed 128 bit key. However, successfully hacking AES 128 requires overcoming some immense challenges:
- Key size: 128-bit key has 3.4 x 10^38 potential keys making it impossible to try all combinations.
- Computational power: Billions of years required to brute force a 128-bit AES key with current computing capability.
- Strong algorithm: Underlying algorithm uses strong substitution, permutation, key mixing to thwart cryptanalysis.
- No known breaks: Despite major cryptanalysis attempts, no successful breaks of AES algorithm reported.
- Real world use: Additional security measures used alongside AES make hacks infeasible.
Is AES-128 Bit Secure?
Yes, AES 128-bit encryption is highly secure and recommended by NIST for protecting classified information up to the SECRET level. Here are some reasons it is considered secure:
- Brute force resistance: 128-bit key makes brute force attacks infeasible with current computing power.
- Strong algorithm: Combination of substitution, permutation, key mixing has thwarted all cryptanalytic attacks.
- NIST validation: Rigorously analyzed and tested by cryptographers to certify its security.
- Real world track record: No known successful breaks of AES since 2001 despite extensive cryptanalysis attempts.
- Conservative design: Extra security margin with 10 rounds instead of the minimum 6 rounds needed in principle.
- Used by governments: Trusted worldwide for securing top secret classified data and communications.
- Guideline compliance: Meets encryption guidelines of NSA, CESG, ISO, IETF.
How to Use AES 128 Bit Encryption
Here are some tips on using AES 128-bit encryption effectively:
- Use a cryptographically secure random number generator to create a sufficiently unpredictable 128-bit encryption key.
- Handle the encryption key securely since its compromise breaks the encryption. Store it securely or protect it with a passphrase.
- Use a cryptographic nonce or initialization vector (IV) to ensure distinct ciphertexts even when encrypting identical plaintext with the same key.
- Use AES 128-bit encryption alongside other security mechanisms like HTTPS, SSL, PKI, passwords, multi-factor authentication for layered security.
- Encrypt data in transit and data at rest to protect confidentiality. Use authenticated encryption to also ensure integrity and authenticity.
- Keep software up to date to take advantage of the latest crypto patches and fixes. Use well-tested implementations like OpenSSL.
- Follow crypto best practices around key management, storage, access control, rotation, destruction to prevent cryptosystem compromise.
Using AES 128-bit encryption correctly is crucial to harness its full security in practical applications.
AES-128 Bit Encryption Key Facts
To summarize, here are the key facts about AES 128-bit encryption:
- Standardized in 2001: AES 128 bit is specified in FIPS PUB 197 as a US government standard.
- 128-bit blocks: Encrypts and decrypts data in fixed blocks of 128 bits using algebraic operations.
- 128 bits key: Uses 128-bit secret key for encryption and decryption.
- 10 rounds: Data goes through 10 rounds of substitution, permutation and mixing.
- Symmetric encryption: Same key used for encrypting and decrypting data.
- Very high security: Provides strong confidentiality through its design and key size.
- Wide adoption: Used globally to protect government and commercial data.
- Fast performance: Efficient implementations in software and hardware.
- No known breaks: Despite major efforts, AES-128 bit has no known successful attacks.
Conclusion
AES 128-bit encryption is a highly secure and versatile algorithm suitable for protecting sensitive data across many applications. Its 128-bit key coupled with a robust encryption cipher provides strong defense against real world attacks with current computing capabilities. Properly implementing AES 128 along with other security controls allows organizations to safely secure their sensitive data. Going forward, AES 256 bit strengthens brute force protection for highly classified data.
Frequently Asked Questions
Is AES 128-bit encryption uncrackable?
Though practically unbreakable currently, AES 128-bit encryption is theoretically vulnerable to brute force attacks. But its 128-bit key size makes it computationally infeasible to crack with current technology.
How long would it take to crack AES 128?
With the most powerful supercomputer, it would take billions of years to crack a 128-bit AES key by brute force based on current computing capabilities.
Is AES 128-bit quantum resistant?
No, AES 128 bit is vulnerable to brute force attacks using quantum computers. But this is still a theoretical threat since practical quantum computing is limited currently. AES 256 provides better protection in the quantum era.
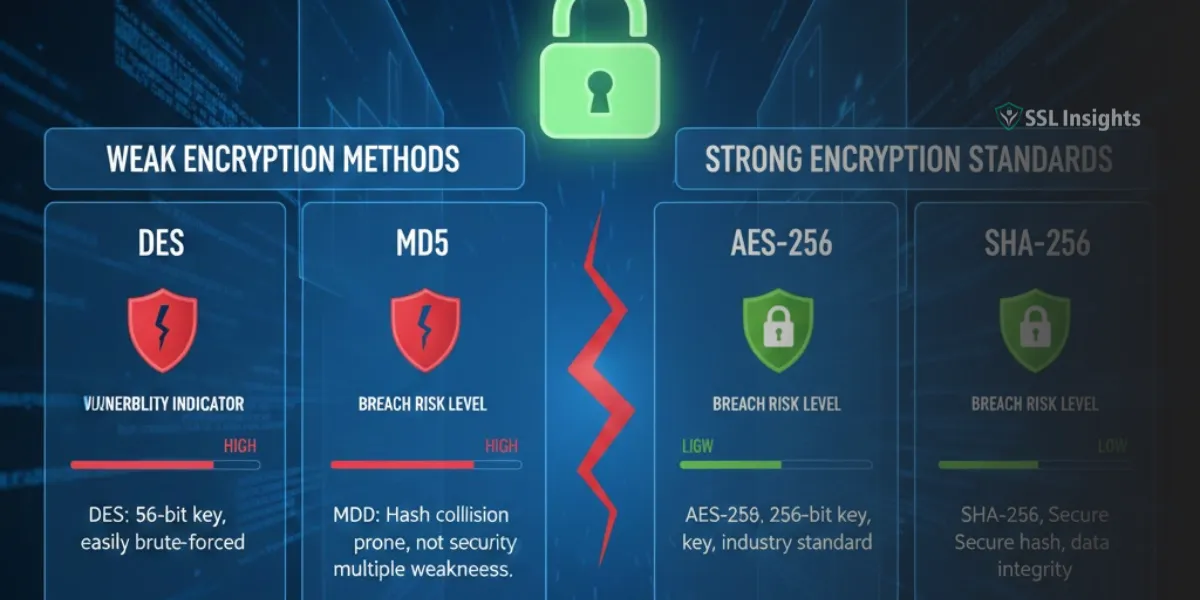
What is the difference between AES 128, 192 and 256?
AES comes in three key sizes: 128 bits, 192 bits and 256 bits. AES 128 is the most common since it offers the best balance between security and performance compared to AES 192 and AES 256.
Is AES 128 secure enough for banking?
Yes, AES 128 provides very robust encryption suitable for securing highly sensitive information like credit card data. Many payment systems and banks use AES 128 bit or stronger encryption.
Is AES 128-bit encryption adequate?
AES 128 bit supplies adequate encryption strength for most common applications like documents, databases, servers, backups, communications. It may not be suitable for highly classified data requiring encryption strength beyond computational brute force.
Should I use AES 256 instead of 128?
AES 256 provides enhanced brute force resistance over AES 128 but is slower. AES 128 delivers adequate security for typical applications today. But AES 256 offers better future-proof quantum security.
Can AES 128 be cracked?
There are no known instances of AES 128 bit being cracked through cryptanalysis despite major efforts. In theory, it is vulnerable to brute force attacks but that is not feasible currently.
Is AES 128 bit safe for password storage?
AES 128 bit is considered secure for encrypting password databases and hashes. But additional measures like salting, hashing, key management are required to implement it properly for password storage.