Basics of Encryption Algorithms
Encryption is the process of encoding information in such a way that only authorized parties can access it. It is used to protect sensitive information like passwords, credit card numbers, personal messages, and confidential business data. With encryption, the data is scrambled into an unreadable format called ciphertext. Only users with the correct decryption key can decipher the ciphertext back into usable plaintext.
Encryption has become one of the most important tools for information security in the digital age. It provides a barrier against cybercriminals, hackers, and other malicious actors who try to steal sensitive data. Without strong encryption, many of the conveniences of online banking, ecommerce, email, and other digital services would simply not be possible.
How Does Encryption Work?
Encryption relies on complex mathematical algorithms to securely scramble plaintext into ciphertext. It uses cryptographic keys to control access and make sure only authorized users can decrypt the data. There are several basic steps to the encryption process:
- Plaintext - The original readable message or data to be protected. This could be a password, text document, photo, email, or any digital asset.
- Encryption Algorithm - A mathematical function that takes the plaintext and a secret key as input and generates the encrypted ciphertext as output. Common algorithms include AES, Blowfish, RC4, and RSA.
- Encryption Key - A value fed into the algorithm along with the plaintext to encrypt or decrypt the data. The key controls access.
- Ciphertext - The scrambled output of the encryption function. The ciphertext looks like incomprehensible gibberish to anyone who doesn't have the decryption key.
- Decryption - Reversing the encryption process using the secret key and algorithm to convert the ciphertext back to readable plaintext.
The encryption and decryption processes rely on the algorithm and key working together in a complex mathematical relationship. Anyone who only has the ciphertext but doesn't have the key should not be able to break the encryption, even if they know the algorithm.
Symmetric vs. Asymmetric Encryption
There are two fundamental types of encryptions: symmetric encryption and asymmetric encryption. Both rely on algorithms and keys, but they go about it in different ways.
Symmetric Encryption
With symmetric encryption, the same key is used to encrypt and decrypt the data. This single secret key must be shared and kept secure by both communicating parties. Examples of symmetric algorithms include AES, Blowfish, RC4, and DES.
Symmetric encryption uses the same key to encrypt and decrypt data.
Benefits of Symmetric Encryption
- Speed - Symmetric algorithms are generally much faster at encrypting and decrypting compared to asymmetric encryption. This makes them suitable for encrypting large volumes of data.
- Simplicity - The math involved is less complex than asymmetric cryptography, making symmetric algorithms quick and easy to implement.
Downsides of Symmetric Encryption
- Key distribution - Some secure channel must be established to share the secret key between parties, which can be tricky.
- No digital signatures - The symmetric key alone cannot provide authentication or non-repudiation like asymmetric keys can.
- Number of keys - For 'n' users to communicate securely, n(n-1)/2 unique symmetric keys are needed (one for each user pair). The number of keys scales up quickly.
Asymmetric Encryption
Asymmetric cryptography uses two separate keys - a public key and a private key. As the names suggest, the private key is kept secret while the public key can be widely shared. The two keys are mathematically linked together through the algorithm.
Asymmetric encryption uses a public-private key pair for encryption and decryption.
How Asymmetric Encryption Works
- The public key is used to encrypt plaintext or verify a digital signature.
- The private key is used for decryption or signing.
- The public key cannot be used to decrypt data encrypted with itself, nor can it decrypt anything encrypted with the private key.
- The private key cannot decrypt data encrypted with the public key.
This one-way relationship allows the public key to be freely shared without compromising the private key's security. Anyone can encrypt with the public key, but only the holder of the private key can decrypt those messages.
Advantages of Asymmetric Cryptography
- Increased security - No need to securely share private keys since these remain protected by the owner. The public keys can be freely shared.
- Digital signatures - The private key can digitally sign messages, which can be verified with the public key. This provides authentication and non-repudiation.
- Key scalability - Only 'n' key pairs are needed for 'n' users to communicate securely with each other. The number of required keys grows linearly rather than exponentially.
Limitations of Asymmetric Cryptography
- Slower performance - The mathematical computations involved are far more complex compared to symmetric encryption. Not ideal for large volumes of data.
- Not always entirely public - The public key must still be authenticated as belonging to the right person to avoid man-in-the-middle attacks.
Common Encryption Algorithms
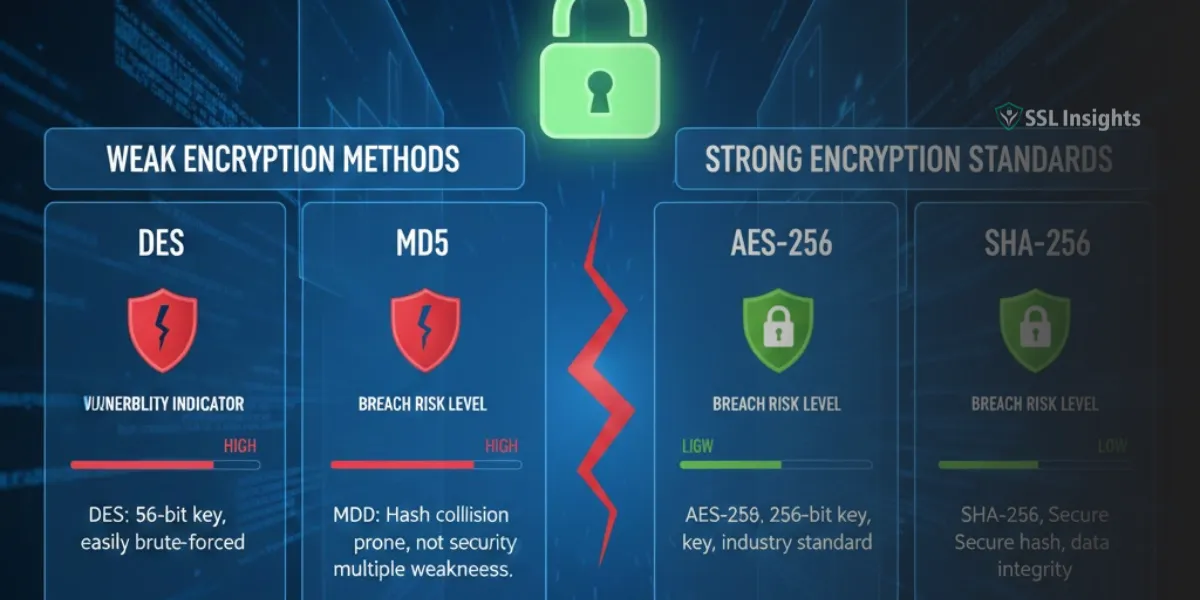
Many different encryption algorithms have been developed over the years, each with their own mathematical underpinnings, key strengths, and overall security. Some have stood the test of time while others have been cracked as computing power has advanced. Let's overview some of the most important and widely used algorithms available today:
1. AES (Advanced Encryption Standard)
Type: Symmetric
Key sizes: 128, 192, 256 bit
Developed: late 90s (standardized in 2001)
Status: Very secure, most widely adopted symmetric algorithm
AES is currently the gold standard for symmetric encryption and the default choice for encrypting electronic data worldwide. It is fast, secure, and flexible enough to work well on a variety of applications and devices. The US Government uses AES with 256-bit keys to protect classified information at the TOP SECRET level.
AES encrypts data in blocks of 128-bit at a time, using cryptographic keys of 128, 192, or 256 bits. The longer key lengths provide greater security as they increase the complexity that attackers face when trying to break the encryption.
Although no successful attacks against AES have been published, there are some concerns about its long-term viability due to the continual advancement in quantum computing which could someday allow brute-force key attacks. But for now, AES provides strong protection and will likely remain secure for the foreseeable future barring any major cryptanalysis breakthroughs.
2. RSA
Type: Asymmetric
Key sizes: 2048+ bits
Developed: 1977
Status: Secure if large enough key sizes are used
RSA is by far the most widely used public-key algorithm. It is named after its inventors - Ron Rivest, Adi Shamir, and Leonard Adleman. The math behind RSA relies on the difficulty of factoring extremely large prime numbers rather than advanced elliptic curves like many newer asymmetric algorithms.
In RSA, the public and private keys are generated together and consist of a modulus (n) that is the product of two large primes, along with integers (e and d) that are related to each other by the modulus. The calculations involved modular exponentiation and Euler's totient function.
RSA key pairs are often created at sizes of 2048 bits or larger. Key lengths of 1024-bits or below are considered vulnerable to attack. As computing power grows, key sizes will need to continue increasing to stay secure. RSA's slow speed makes it impractical for direct encryption of large data. But it is highly useful for generating digital signatures and exchanging keys.
RSA provides strong encryption when sufficiently long key sizes are used. But if large-scale quantum computers become reality, they could potentially crack RSA encryption by quickly factoring the public keys. So, its long-term future is questionable.
3. Elliptic Curve Cryptography (ECC)
Type: Asymmetric
Key sizes: 256-521 bits
Developed: 1985
Status: Growing popularity due to better efficiency than RSA
Elliptic Curve Cryptography is a modern public-key algorithm based on elliptic curve mathematics that can achieve equivalent security to RSA but with much shorter key lengths. For example, a 256-bit ECC key provides comparable cryptographic strength to a 3072-bit RSA key. The reduced key sizes result in faster performance, lower power consumption, bandwidth savings, and storage efficiencies.
The math behind ECC uses properties of elliptic curves over finite fields to create the public and private keys. Some benefits include:
- Very difficult for attackers to solve the discrete logarithm problem that underpins ECC encryption.
- Smaller keys and signatures for equivalent security to other asymmetric algorithms.
- Excellent performance across a wide range of platforms from mobiles to PCs.
ECC adoption has steadily grown thanks to being added to standards like TLS, PGP, SSH, and Bitcoin. It is suitable for constrained devices like smartphones and embedded systems. The algorithms are more convoluted than RSA which can make implementation tricky. But ECC provides strong security and efficiency especially for internet-layer encryption, digital signatures, and key exchange.
4. Blowfish
Type: Symmetric
Key sizes: 32-448 bits
Developed: 1993
Status: Secure algorithm but waning popularity, replaced by AES
Blowfish is a fast, compact symmetric cipher developed in the 1990s as an alternative to AES. It uses a 64-bit block size and key lengths ranging from 32 bits up to 448 bits. Weaknesses have been found when using fewer than 128 key bits, so larger keys are recommended. Blowfish has no known successful cryptographic attacks against it, but AES has become the dominant symmetric cipher for new applications.
5. RC4
Type: Symmetric
Key sizes: 40-2048 bits
Developed: 1987
Status: Vulnerable to attacks, no longer considered secure
RC4 (Rivest Cipher 4) is an older stream cipher developed in 1987 for RSA Security. It uses variable key sizes from 40 bits up to 2048 bits. RC4 was initially a trade secret but leaked out in 1994. Attacks against RC4 have gotten progressively better over the years, allowing potentially feasible attacks against SSL/TLS when using RC4 encryption. It is now considered insecure and should not be used for new systems.
How is Encryption Used?
Now that we've looked at some common algorithms, how and where is encryption actually applied today? What technologies and products rely on it?
Data-in-Transit Encryption
Data transmitted over networks can easily be intercepted without encryption. Encrypting data in transit ensures it stays private and tamper-proof as it moves between locations or across public networks like the internet. Common examples include:
- TLS (Transport Layer Security) - Encrypts web traffic and internet communications. Provides the 'HTTPS' secure connection protocol and successor to SSL. TLS uses asymmetric (public-key) encryption for authentication and handshake and symmetric encryption (e.g. AES) for data transfer.
- IPsec - Suite of protocols for encrypting traffic on IP networks, including VPNs and WiFi hotspots. Uses the IKE protocol to set up a secure channel then symmetric encryption for data transfer.
- SSH (Secure Shell) - Encrypted network protocol for securely logging into command line interfaces of remote machines and servers. Uses asymmetric encryption to authenticate and negotiate encryption keys for the session.
- PGP/GPG Encryption - Encrypts data including emails, messages, files, directories. Based on asymmetric cryptography to securely share public keys and sign data.
- E2E Chat Encryption - Apps like WhatsApp and Signal use end-to-end encryption to protect chat sessions and calls. Only the sender and recipient can decrypt messages.
- MACsec - Security standard that encrypts traffic on Ethernet LANs, preventing man-in-the-middle attacks on the underlying infrastructure.
Data-at-Rest Encryption
Data-at-rest refers to data that is persisted and stored physically in files, databases, flash drives, external disks, cloud storage, backups, archives, etc. Since this data lives outside a transient session, it needs protective encryption against attackers who gain physical access to the storage media. Examples include:
- Full disk encryption - Encrypts the entire boot disk/storage device at the volume level. Protects against access if a laptop is lost or stolen.
- File/folder encryption - Selectively encrypting important files and folders for an added layer of protection.
- Encrypted databases - Databases often house sensitive information like financial transactions, healthcare records, credentials, PII, and other private data. Encrypting this data adds a major defense against breaches. Popular DBs like SQL Server and Oracle provide built-in encryption capabilities.
- Cloud storage encryption - Services like iCloud, Dropbox, and Google Drive encrypt data before uploading it to the cloud and while at rest in cloud storage.
- Encrypted archives - Password protected Zip files that encrypt the compressed archive contents. Widely used for securely storing and sending groups of files.
- Encrypted backups - Backups create copies of sensitive data that could be exposed if not properly secured. Encryption provides an essential security control for backup media.
- Cryptocurrency wallets - Wallets hold the public and private keys associated with blockchain assets. Encrypting the wallet adds critical protection against theft of cryptocurrencies.
Public Key Infrastructure (PKI)
Public Key Infrastructure (PKI) provides the basis for establishing trust and authentication of public keys used in asymmetric encryption. With symmetric encryption, both parties share the same secret key directly. But with public-key encryption, how is a user able to validate that a public key really belongs to the right entity?
PKI establishes this trust through:
- Digital Certificates - Certificates issued and digitally signed by a Certificate Authority bind together the entity's identity with their public key. The CA's signature and trust anchor proves the key is genuine.
- Certificate Authorities - CAs verify an entity's identity then issue and sign a certificate containing their public key. The CA publishes certificate revocation lists as needed.
- Registration Authorities - RAs verify user identities before certificate issuance and handle the application process on behalf of a CA.
- Repositories/Directories - Certificates and public keys are stored in repositories like LDAP servers for distribution and revocation checking.
PKI provides the essential management and distribution framework to prevent impersonation. However, the system is only as secure as its root CAs. If a CA's private root key were to get compromised, attackers could use it to issue fraudulent certificates and spoof identities.
Common Use Cases for Encryption
Encryption plays an indispensable role in security today across many different industries, products, and use cases:
Banking & Finance
Protecting highly sensitive personal and financial data. Encryption is crucial for:
- Online banking sessions, fund transfers, and transactions
- Credit card numbers and mobile payment platforms
- Stock trading apps, investment accounts, and financial records
- Cryptocurrency wallets and blockchain transactions
- ATM connections and communications
- HR payroll systems and accounting systems
Email & Messaging
Securing communications and guarding privacy:
- Email encryption with S/MIME and PGP to encrypt messages and attachments.
- E2E encrypted chat apps like WhatsApp, Signal, and Telegram for private conversations.
- VOIP call encryption preventing eavesdropping and wiretapping.
Cloud Services
Safeguarding data stored and accessed remotely in the cloud:
- Encrypted databases, object storage, archives, and backups
- Disk and volume encryption options for IaaS virtual instances
- Encrypting data in transit to and from cloud providers
- Key management systems and HSMs to secure keys
Wireless Networks
Locking down WiFi hotspots and cellular connections against eavesdropping:
- WPA2 WiFi encryption secures wireless networks and prevents packet sniffing attacks.
- LTE encryption applied to CDMA cellular networks protects call data and traffic.
- Bluetooth encryption on BR/EDR & Bluetooth Low Energy connections.
Healthcare Industry
Ensuring patient privacy protections:
- Encrypted medical records, prescriptions, lab reports, imagery, genetics, and research data.
- HIPAA compliance for healthcare data 'at rest' and 'in motion'.
- Biometric data, wearables, remote health monitoring devices.
Government Agencies
Safeguarding classified and sensitive documents:
- Top Secret and classified data marked up to 'TS/SCI'.
- Encrypted communications, devices, and storage for classified systems.
- Defense agencies, law enforcement, and the intelligence community rely heavily on encryption.
- Secure government websites, portals, applications, and databases.
Retail & Ecommerce
Minimizing risk of payment data theft and financial fraud:
- Encrypted customer credit card numbers, order details, and payment systems.
- Securing point-of-sale (POS) terminals against card skimmers and hacking.
- Ecommerce checkout pages and merchant payment gateways using TLS.
Education Sector
Shielding student and institutional data:
- Student record systems, grading systems, e-learning portals
- Campus payment systems, procurement systems, HR databases
- Digital repository servers holding volumes of research data
- Secure student/faculty WiFi and administrative networks
Encryption Key Management
The cryptographic keys are the crown jewels that ultimately protect encrypted data. Keys must be properly generated, stored, and managed across their entire lifecycle. Compromised keys defeat the purpose of encryption.
Best practices for encryption key management include:
- Secure key generation- Keys should be randomly generated by cryptographically secure pseudo-random number generators (CSPRNGs), not simple PRNGs. Generating keys in insecure environments increases risks.
- Key escrow and recovery- Striking a balance between making keys inaccessible if lost while also preventing unwanted access by third parties. Use multi-party key recovery schemes.
- Key storage and transmission- Keys at rest should reside in secure storage like HSMs. Keys in transit should always be encrypted.
- Key rotation- Periodically generating new keys and retiring old one’s limits exposure over time and reduces the impact of a compromised key.
- Access controls- Restrict key usage through logical access controls and separation of duties. Use least privileged permissions.
- Key destruction- Keys should be securely wiped when no longer needed following proper cryptographic erase techniques.
- Logging, auditing- Monitor key access events, usage patterns and exposure. Log events like key creation/deletion.
- Key backup- Back up keys securely to allow recovery but prevent duplication in multiple places. Store backups separately from operational keys.
- Protocol support- Ensure proper protocols and key exchange algorithms are in place particularly for asymmetric encryption.
- Key management system- Centralize key management under a single lifecycle management system rather than relying on ad hoc methods.
Proper encryption key management controls are just as critical as the algorithms themselves. Poor key management can lead to data exposures even if strong encryption is used.
Advantages & Disadvantages of Encryption
Encryption certainly makes data more secure, but it isn't a magic solution without any drawbacks. Here are some key pros and cons to consider:
Advantages of Encryption
- Protects confidentiality of sensitive data in transit and at rest.
- Allows secure communication channels over untrusted networks.
- Shields against cyber threats like data exfiltration, theft, wiretapping.
- Enables safer data storage on public clouds that cannot be trusted.
- Facilitates online commerce, banking, and activities needing identity assurances.
- Provides verification of data integrity and authenticity.
Disadvantages of Encryption
- Encrypted data is unreadable and unusable without decryption keys.
- Cryptographic operations can negatively impact performance and latency.
- Key management complexity especially with asymmetric ciphers.
- Encrypted data cannot be easily searched or analyzed.
- Recovery from lost keys is difficult or impossible.
- Government restrictions on permitted encryption strength.
- Incorrectly implemented encryption can have security holes.
- Potential for insider threats from authorized users.
Determining the right balance requires assessing the assets needing protection against the constraint’s encryption may impose for a particular use case. But generally, encryption improves security posture despite some drawbacks.
Encryption Algorithms in Action
Let's look at some examples of encryption algorithms applied in real-world protocols and applications:
- AES in VPNs- Many popular virtual private network solutions like OpenVPN and WireGuard use AES symmetric encryption to secure data in the encrypted tunnel. AES provides performance and security with minimal overhead.
- RSA in HTTPS- Secure HTTPS websites have their domain validated SSL/TLS certificates signed by a trusted certificate authority using RSA encryption. Web browsers verify the RSA signature on the cert matches the public key.
- ECC in Blockchain- ECC is widely used to secure blockchain transactions. Bitcoin uses the secp256k1 elliptic curve for ECC key pairs to sign transactions. The digital signatures validate ownership of the cryptocurrency.
- PGP Encryption- OpenPGP and PGP use a combination of asymmetric encryption and symmetric encryption. RSA or ECC manage the public-private key pairs while AES is used to symmetrically encrypt messages, files, and folders.
- Signal Protocol- The Signal messaging app pioneered an e2e encrypted messaging protocol using a combination of asymmetric ECC key pairs, symmetric AES-GCM encryption, and the X3DH key agreement protocol. Voice/video calls also leverage SRTP and ZRTP.
The Future of Encryption
Cryptography has played a pivotal role in the growth of the internet and digital age. As computing power and quantum computing advance, we will continue seeing older cryptographic primitives and weaker key sizes phased out in favor of stronger quantum-resistant algorithms.
Post-quantum cryptography is an active research area with algorithms like lattice-based cryptography and multivariate-quadratic equations emerging as potential quantum-safe replacements to RSA and ECC. But the math and implementations are not yet mature.
Future encryption methods will likely be hybrid schemes that combine symmetric algorithms like AES with post-quantum public key algorithms instead of traditional RSA or ECC when those are rendered obsolete. Cryptographic agility and algorithm flexibility will be critical in the fast-moving encryption arms race against adversaries.
Conclusion
Encryption provides the backbone of data security and trust in the digital world. By transforming plaintext into ciphertext using secure algorithms and keys, encryption allows sensitive information to be stored and transmitted safely over insecure channels. It enables online commerce, private communications, secure cloud computing and so much more.
A basic overview of how symmetric and asymmetric encryption work provides helpful context on the fundamentals. Looking under the hood at common algorithms like AES, RSA, and ECC shows how encryption is applied in real-world technologies. And understanding encryption's advantages and limitations sheds light on why it is so important despite some downsides.
With encryption built into everything from databases and cloud services to web connections and messaging apps, individuals and organizations must learn how to effectively leverage it to protect their data. Cryptography is an arms race where attackers and defenders continue escalating their tools and tactics. But cryptography, when properly implemented, can provide a shield against the compromise of sensitive information.
FAQs About Encryption
What are the different types of encryption?
The main types of encryption are symmetric encryption (uses the same key) and asymmetric encryption (uses public-private key pairs). Symmetric encryption is faster for large data but asymmetric encryption enables better key distribution and security.
What is encryption and how does it work?
Encryption converts plaintext data into ciphertext that looks scrambled and unintelligible. It uses algorithms and cryptographic keys to scramble the data in a reversible way so only authorized users with the key can decrypt it back to plaintext.
Why is encryption important for security?
Encryption secures sensitive data in transit and at rest that would otherwise be vulnerable. It provides the underlying security for online banking, private messaging, ecommerce transactions, and other activities that need to hide confidential data.
What are the most secure encryption algorithms?
The AES and RSA algorithms are widely used and considered very secure when large enough key sizes are used properly. ECC offers efficient security. Older algorithms like RC4 and DES are now considered weak and deprecated.
What is the difference between hashing and encryption?
Hashing is a one-way cryptographic function that produces a unique fixed-length digest from input data. Encryption is two-way and reversible with the proper key. Hashing is used for integrity checks while encryption focuses on confidentiality.
How does public key encryption work?
Public key encryption uses mathematically related public-private key pairs. The public key encrypts data while only the private key holder can decrypt. The public key can be widely shared to allow encryption by anyone. Private keys provide the trapdoor.
What is quantum encryption?
Quantum encryption leverages principles of quantum mechanics for security. Quantum key distribution (QKD) enables two parties to produce a shared random key over a quantum channel. QKD aims to provide provably secure key exchange resistant to quantum computers.