Verified by Priya Mervana, SSL Security Researcher at SSLInsights - Last reviewed: May 2026 | Based on hands-on analysis of PKI deployments across web security and enterprise SSL environments.
QUICK DEFINITION
Asymmetric cryptography uses two mathematically linked keys - a public key and a private key - to secure digital communications. The public key encrypts data or verifies signatures; the private key decrypts data or creates signatures. Neither key can perform the other's function, and the private key cannot be derived from the public key. This pairing is what makes modern SSL/TLS, email encryption, and cryptocurrency wallets possible.
Source: Priya Mervna, SSLInsights - web security expert, 10+ years
What is the difference between public key and private key?
The core distinction is access: a public key is distributed freely to anyone who needs to communicate securely with you, while a private key is held only by its owner and never shared. One encrypts; the other decrypts. Together they form the foundation of every HTTPS connection you make today.
The table below captures the functional differences before the full explanation:
| Attribute | Public Key | Private Key |
| Distribution | Shared freely | Never shared |
| Primary use | Encrypt messages / verify signatures | Decrypt messages / create signatures |
| Security guarantee | Confidentiality | Authenticity & non-repudiation |
| If compromised | Low impact - replace certificate | High impact - all secured data is at risk |
| Storage | Embedded in digital certificates | Encrypted on server, HSM, or smart card |
| Key size (RSA, secure 2026) | 2048-bit minimum; 3072-bit recommended | Same algorithm, same size as paired public key |
What Is a Public Key in Cryptography?
A public key is the shareable half of an asymmetric key pair - a long string of numbers generated by an algorithm like RSA or ECC that anyone can use to encrypt a message or verify a digital signature. Because the corresponding private key is the only key that can reverse those operations, sharing your public key widely carries no security risk.
How does public key encryption work?
When a browser connects to an HTTPS site, it retrieves the server's public key from its SSL certificate. The browser uses that public key to initiate an encrypted session. Only the server - holding its private key - can complete that handshake and read what the browser sends. This is the mechanism behind every secure login form, payment page, and API call on the web.
Public keys are distributed through four main channels: digital certificates issued by certificate authorities (CAs), public key servers such as keys.openpgp.org, direct manual exchange via email or USB, and automatic key exchange built into apps and protocols like HTTPS. The critical point is that how are public keys distributed safely depends on certificate authorities vouching for the key's ownership - without that chain of trust, any public key could be faked.
At SSLInsights, analysis of common SSL misconfigurations across hundreds of deployments shows that most "man-in-the-middle" vulnerabilities stem not from weak public keys themselves but from absent or improperly validated certificates - meaning the key is fine but the trust layer around it is broken.
What Is a Private Key and What Is It Used For?
A private key is the secret counterpart to a public key - generated at the same moment, mathematically linked, but designed to stay exclusively with its owner. It performs two functions no other key can: decrypting messages encrypted with its paired public key, and creating digital signatures that the public key can verify.
Where is the private key stored on a server?
In most web server environments, the private key lives as an encrypted file in the server's file system (e.g., /etc/ssl/private/ on Linux-based systems), protected by file permissions and, ideally, a passphrase. High-security environments store private keys in Hardware Security Modules (HSMs) - dedicated tamper-proof devices that perform cryptographic operations without ever exposing the key in plaintext. Cloud environments often use services like AWS Certificate Manager or Azure Key Vault, which handle private key storage and rotation automatically.
What is a digital signature and how does it work?
A digital signature is created by running a message through a hash function, then encrypting that hash with the sender's private key. The recipient decrypts the hash using the sender's public key. If the decrypted hash matches a fresh hash of the message, the signature is valid - proving both that the sender is who they claim to be and that the message wasn't altered in transit.

Priya Mervana
SSL Security Researcher, SSLInsights
"The most common private key mistake I see in production environments isn't weak key size - it's inadequate storage. Keys sitting in world-readable directories or bundled inside Docker images give attackers immediate full access to all encrypted communications. Treat your private key with the same security posture you'd apply to a root password."
How Are Public and Private Keys Generated?
Both keys are produced simultaneously by a cryptographic algorithm, with the private key chosen first as a random number, and the public key derived from it through a one-way mathematical operation. This means the public key can be calculated from the private key, but the reverse - can a private key be derived from a public key? - is computationally infeasible with current hardware given sufficient key sizes.
The two dominant algorithms in use today are:
- RSA (Rivest–Shamir–Adleman) selects two very large prime numbers, multiplies them together, and bases security on the difficulty of factoring that product. A 2048-bit RSA key is the current minimum for production use; NIST's 2024 post-quantum guidance recommends transitioning to 3072-bit or higher for long-lived certificates. RSA is widely supported but produces larger key sizes than ECC for equivalent security levels.
- ECC (Elliptic Curve Cryptography) uses the algebraic properties of elliptic curves over finite fields. A 256-bit ECC key provides roughly equivalent security to a 3072-bit RSA key - making ECC significantly faster for TLS handshakes and better suited to mobile and IoT environments. Most modern TLS 1.3 deployments default to ECC via the P-256 or X25519 curves.
- RSA vs ECC key generation differences come down to this tradeoff: RSA has broader legacy compatibility; ECC offers smaller keys, faster operations, and lower compute overhead. For new deployments in 2026, ECC is the preferred choice unless legacy system compatibility is required.
Symmetric vs Asymmetric Encryption: Where Public/Private Keys Fit
What is the difference between symmetric vs asymmetric encryption?
Symmetric encryption uses one shared key for both encryption and decryption - fast and efficient, but it requires both parties to already share that secret key securely. Asymmetric encryption (the public/private key system) solves that key-exchange problem: the public key can travel openly over any network, eliminating the need to pre-share a secret.
In practice, TLS combines both: asymmetric cryptography handles the initial handshake and key exchange, then both parties switch to a symmetric session key (like AES-256) for the bulk of the data transfer. How does SSL use public and private keys? SSL/TLS uses the server's public key during the handshake to establish a shared session key; from that point forward, all communication uses that faster symmetric key. The private key's job ends once the handshake is complete.
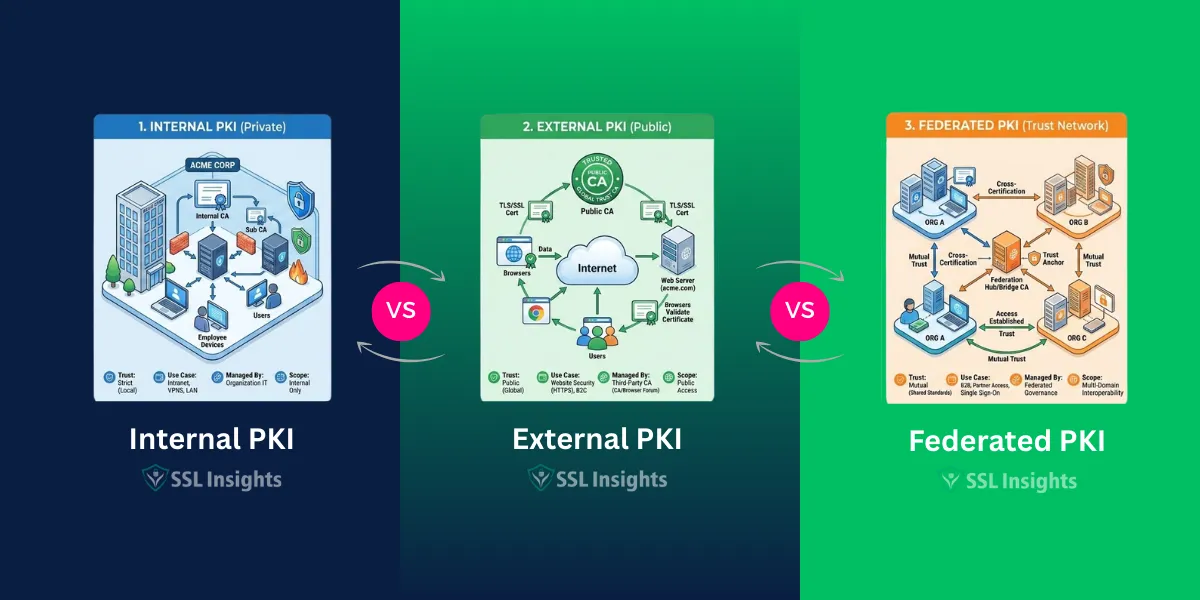
What is public key infrastructure (PKI) explained simply?
PKI is the system of certificate authorities, digital certificates, and revocation mechanisms that lets the internet trust public keys at scale. Without PKI, any attacker could publish a fake public key claiming to belong to your bank. PKI solves that by having a trusted CA cryptographically sign each certificate, binding a public key to a verified identity.
Real-World Examples: How Public and Private Keys Are Used
How SSL/TLS Certificates Use Key Pairs
Every HTTPS website holds a private key on its web server and publishes a corresponding public key inside its SSL certificate. During the TLS handshake, the browser uses the public key to verify the server's identity and establish a session key. The server uses its private key to complete that verification. According to the SSL/TLS statistics tracked by SSLInsights, over 97% of the top 1 million websites now use HTTPS - meaning this key-pair mechanism is operating billions of times per day.
PGP/GPG Email Encryption
PGP (Pretty Good Privacy) and GPG (GNU Privacy Guard) apply asymmetric cryptography to email. Each participant generates a key pair and publishes their public key to a key server. Senders encrypt messages with the recipient's public key; only the recipient's private key can decrypt them. The same mechanism supports signing: a sender signs with their private key, and recipients verify with the matching public key - confirming authenticity without sharing any secrets.
Cryptocurrency Wallets
Public key infrastructure PKI explained in the context of Bitcoin: each wallet address is derived from a public key. Spending funds requires a transaction signed by the corresponding private key. The network verifies the signature using the public key, confirming the spender owns the wallet - all without the private key ever leaving the owner's device. Losing the private key means permanent loss of access to those funds, with no recovery mechanism.

Priya Mervana is an SSL security researcher at SSLInsights with deep experience in PKI deployments, certificate management, and TLS configuration analysis. Her work covers SSL/TLS best practices for web servers, enterprise networks, and cloud environments, with a focus on making cryptographic concepts accessible to practitioners who need to act on them - not just understand them theoretically.
PRACTITIONER’S NOTE
In reviewing SSL configurations across a range of web environments, the single most consistent issue isn't weak keys - it's neglected key management. Private keys get copied into version control, stored without encryption, or never rotated after a server migration. A 4096-bit RSA key stored carelessly is far more vulnerable than a properly managed 2048-bit key. Before you focus on key size, audit where your private keys actually live and who can access them. That audit will reveal more risk than any algorithm comparison.
– Priya Mervana | SSL Security Researcher, SSLInsights
Final Words
The public key and private key work as a pair - each one meaningless without the other. The public key travels freely and handles encryption and signature verification; the private key stays locked away and handles decryption and signature creation. Every SSL certificate, encrypted email, and cryptocurrency transaction relies on this relationship. Understanding it is the first step to making sound decisions about certificate selection, key storage, and your overall security posture.
Frequently Asked Questions on Public Key vs Private Key
What is the main difference between a public key and a private key?
A public key is distributed openly and used to encrypt data or verify digital signatures. A private key is kept secret by its owner and used to decrypt data or create signatures. The two are mathematically linked: one reverses what the other performs, but neither can be calculated from the other with current computing power at recommended key sizes.
Which key do you share publicly?
The public key. Sharing it widely is by design - anyone who wants to send you an encrypted message or verify your identity needs your public key. Sharing it does not expose your private key or compromise your security in any way.
Can a private key be derived from a public key?
No, not with any practical computing method available today. The mathematical operations used (prime factorization for RSA, discrete logarithm on elliptic curves for ECC) are designed to be one-way. Deriving a 2048-bit RSA private key from its public key would require more compute time than the current age of the universe.
What key size is considered secure in 2026?
For RSA: 2048-bit is the minimum; 3072-bit is recommended for certificates with multi-year validity. For ECC: 256-bit (P-256 or X25519) is considered secure and is the default in TLS 1.3. NIST's 2024 post-quantum migration guidance recommends beginning evaluation of ML-KEM (Kyber) for post-quantum readiness, though widespread adoption is still several years away.
What happens if your private key is compromised?
Any attacker with access to your private key can decrypt all past and future communications protected by that key (unless forward secrecy was used), forge digital signatures in your name, and impersonate your server to connecting clients. Immediate steps: revoke the certificate with your CA, generate a new key pair, reissue the certificate, and rotate any secrets that may have been exposed. Time matters - most CAs can revoke within hours.
Can you recover a lost private key?
No. A private key cannot be reconstructed from the public key or from any encrypted data. If the key is lost without a backup, the only resolution is to generate a new key pair and reissue the certificate. This is why encrypted, redundant backups of private keys are a non-negotiable part of any PKI management policy.