What’s the Difference between AES and DES Ciphers
Encryption algorithms like AES Cipher and DES Cipher are not just theoretical concepts but essential tools for protecting sensitive data in today's digital world. When comparing AES Cipher vs DES Cipher, it's not just about which is newer or stronger, but about the practical implications for your data security.
This article will provide an in-depth comparison of AES and DES ciphers, analyzing their key lengths, block sizes, security levels, and more. AES represents a major improvement over DES and is now the encryption algorithm of choice for many organizations.
Understanding the core AES and DES Ciphers distinctions will shed light on why the newer AES standard provides enhanced security and resilience against attacks. With data breaches on the rise, utilizing robust encryption like AES is not just a good idea but a necessity for anyone transmitting confidential information digitally.
Key Takeaways
- AES and DES are symmetric key encryption algorithms that use the same secret key for encrypting and decrypting data.
- AES is newer, supports larger key sizes, and is more secure than DES. DES is now considered insecure for many applications.
- AES operates on fixed block sizes of 128 bits and supports key sizes of 128, 192, and 256 bits. DES operates on 64-bit blocks and uses 56-bit keys.
- AES performs multiple encryption rounds and permutations, making it very difficult to crack through brute force. DES has simpler rounds and is vulnerable to brute-force attacks.
- AES is the current encryption standard recommended by the US government and widely used globally. DES has been phased out due to its vulnerabilities.
- AES is significantly faster and more efficient in software than DES, making it better suited for a wide range of applications.
AES Cipher vs DES Cipher: A Quick Comparison
|
Feature |
AES |
DES |
|
Standardized |
2001 |
1977 |
|
Block size |
128-bit |
64-bit |
|
Key sizes |
128, 192, 256-bit |
56-bit |
|
Rounds |
10, 12, 14 |
16 |
|
Structure |
Substitution-permutation network |
Feistel network |
|
Implementation |
Efficient in software and hardware |
Optimized for hardware |
|
Security |
Very high - no known breaks |
Vulnerable to attacks |
|
Brute force resistance |
Excellent - keys too large |
Poor - 56-bit key is weak |
|
Cryptanalysis resistance |
Excellent - strong against known attacks |
Poor - susceptible to differential and linear cryptanalysis |
|
Speed |
Very fast in software |
Slower in software |
|
Memory usage |
Low |
High |
|
Parallelizability |
High |
Low |
|
Design complexity |
Simple |
Complex |
|
Adoption |
Widely deployed and standardized |
Deprecated, restricted usage |
|
Recommendation |
Strongly recommended and preferred |
Deprecated and not recommended |
What is Encryption and How Do Ciphers Work?
Encryption is the process of encoding data in such a way that only authorized parties can read it. This is accomplished using encryption algorithms or ciphers.
The original data is called plaintext, and the encrypted data is called ciphertext. Encryption converts plaintext to ciphertext using a key. Decryption reverses this process, converting ciphertext back into plaintext using the same key.
Symmetric key encryption uses the same secret key for both encryption and decryption. The sender encrypts the plaintext with the key to generate ciphertext. The receiver uses the same key to decrypt the ciphertext and restore the original plaintext. This requires securely sharing the secret key.
AES and DES are symmetric key block ciphers. They break data into fixed-size blocks and encrypt one block at a time. Each block is encrypted using the secret key in a series of steps called rounds. Modern block ciphers like AES and DES rely on multiple rounds for security.
What is the Advanced Encryption Standard (AES)?
The Advanced Encryption Standard (AES) is a symmetric encryption cipher standardized by the US National Institute of Standards and Technology (NIST) in 2001.
AES emerged after a 5-year standardization process to select a successor for DES, which was showing vulnerabilities. An algorithm called Rijndael, submitted by Belgian cryptographers, was chosen as the AES algorithm.
AES specifies a fixed block size of 128 bits and supports key sizes of 128, 192, and 256 bits. It operates on a 4×4 column-major order matrix of bytes called the state. The AES cipher uses several substitution and permutation rounds on the state to encrypt the data blocks.
Decryption uses the inverse functions to revert the rounds. AES typically applies 10 to 14 rounds depending on the key size for high security:
- 128-bit keys - 10 rounds
- 192-bit keys - 12 rounds
- 256-bit keys - 14 rounds
AES provides very strong security and is approved by US federal organizations to protect classified information. It is used globally for encrypting data in transit and at rest. The larger key sizes future-proof AES against brute force attacks.
What is the Data Encryption Standard (DES)?
The Data Encryption Standard (DES) is a symmetric key block cipher published as a federal standard in 1977. IBM developed it based on an earlier cipher called Lucifer. DES was the predominant encryption algorithm in the commercial world for decades.
DES operates on fixed 64-bit blocks of plaintext and ciphertext. It uses 56-bit keys during the encryption process. DES applies 16 identical rounds of permutations and substitutions determined by the key. This provides strong cryptographic strength.
The US government endorsed DES for protecting sensitive but unclassified data. Throughout the late 20th century, it saw widespread global adoption in the finance, manufacturing, and government sectors. Many standard protocols, such as SSH, SSL, and IPsec, supported DES-based encryption.
However, as computing power increased, the 56-bit key size was found vulnerable to brute force attacks. 3DES, a variant using up to three keys, aimed to increase the key size. By the late 1990s, DES was officially deprecated in favor of the stronger AES algorithm.
What are the Key Differences between AES and DES?
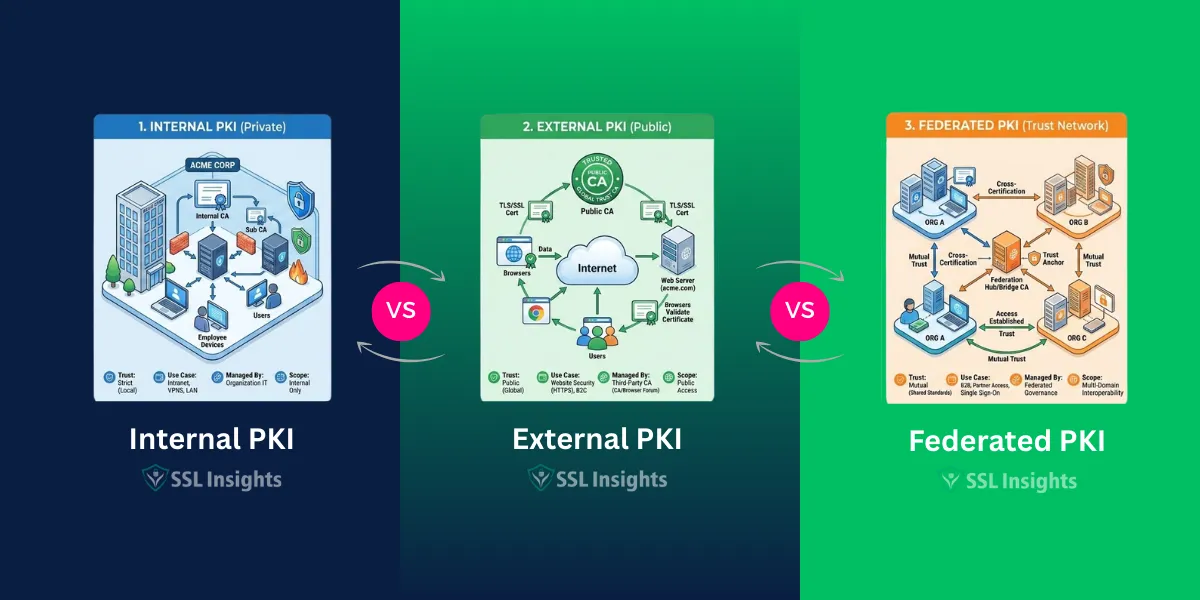
While AES and DES are both symmetric key algorithms, there are important technical differences between the two ciphers:
Block Size
- AES operates on a fixed block size of 128 bits during encryption and decryption.
- DES works with much smaller 64-bit blocks.
Key Length
- AES supports key sizes of 128, 192, and 256 bits. The larger keys provide greater security against brute-force attacks.
- DES uses only 56-bit keys. This makes it susceptible to cracking.
Number of Rounds
- AES applies 10 to 14 rounds, depending on the key size. The multiple rounds provide high diffusion and confusion.
- DES has simpler 16 identical rounds. This makes cryptanalysis easier.
Implementation
- AES can be efficiently implemented on 8-bit processors and in hardware. It requires little memory and is fast in software.
- DES has a complex implementation and operates slower in software. It is better suited for hardware implementation.
Security
- AES has no known practical vulnerabilities so far. The US government uses AES to encrypt top-secret classified information.
- DES has several vulnerabilities and can be cracked in under a day. It is no longer considered secure by standards.
Adoption
- AES is the de facto standard for encryption, mandated by many government and enterprise policies. It is widely deployed and supported.
- DES usage is deprecated worldwide due to its vulnerabilities. Support has declined, and most protocols recommend using AES instead.
How does AES Work?
The AES cipher uses a round-based substitution-permutation network to encrypt data blocks. Each round applies mathematical operations to thoroughly scramble and diffuse the input bits using the secret key. Let's look at how the AES encryption algorithm works:
Key Expansion
The first step is to generate round keys from the input secret key using Rijndael's key schedule. The key bits are expanded into separate round keys for each of the Nr rounds. For the 128-bit key size, there will be 11 round keys, including the initial key.
Initial Round
The plaintext block is XORed with the initial round key derived from the input secret key. This produces an initial intermediate ciphertext block.
Rounds
The intermediate ciphertext now goes through Nr-1 rounds of four stages:
- SubBytes: A nonlinear substitution cipher using a lookup table called the S-box. This confuses.
- ShiftRows: A permutation that shifts the rows cyclically by different offsets. This provides diffusion.
- MixColumns: A column-wise mixing operation using matrix multiplication in the finite field GF(28). It adds more diffusion.
- AddRoundKey: Each round key is XORed with the current block state. This adds the key material to the ciphertext.
The repeated rounds produce sufficient diffusion and confusion of the input bits. The decryption process applies the inverse functions of all these round stages.
Final Round
The final Nr round lacks the MixColumns stage. The final ciphertext is produced after the SubBytes, ShiftRows, and AddRoundKey stages in the last round.
This ciphertext can only be decrypted by applying the Nr rounds with the original key that was used to generate the round keys.
How does DES Work?
DES operates on 64-bit blocks of plaintext and applies 16 rounds of permutations, swaps, and substitutions guided by the 56-bit key. Here is an overview of how DES encryption works:
Initial Permutation
The input 64-bit plaintext block is first subjected to an initial permutation (IP). This rearranges the bits according to a predefined pattern.
Round Function
The permuted block now goes through 16 identical rounds of operations. Each round applies the following functions:
- Expansion Permutation (E): Expands the block from 32 bits to 48 bits using an expansion table.
- XOR with Round Key (⊕): The 48-bit output is XORed with a 48-bit round key derived from the main key.
- S-Box Substitution: The 48 bits are divided into 8 groups of 6 bits each. Each group is substituted through an S-Box lookup table to get a 4-bit output. This provides nonlinearity.
- P-Box Permutation: The 32 output bits are permuted again according to a fixed permutation table.
Final Permutation
After the 16 DES rounds, the output block undergoes a final permutation (IP-1), and the 64-bit ciphertext is produced.
Decryption applies the same series of steps in reverse order using the same key. The initial permutation IP-1 is applied first, then the 16 rounds are applied using the round keys, and finally, the inverse initial permutation IP produces the original plaintext.
Overall, the 16 rounds of substitution, permutation, and key mixing provided sufficient security when DES was designed. However, its short key length makes it vulnerable to brute-force attacks with modern computing power.
Key Points on DES
- Operates on 64-bit blocks using 56-bit key
- Applies an initial and final permutation
- 16 identical rounds of substitution, permutation, and XORing with round keys
- The 56-bit key is split into two 28-bit halves for each round
- Weaknesses due to short key size and simpler round function
- Provides inadequate security for today's applications
- It has been replaced by the stronger and more efficient AES algorithm
What are the Main Security Differences between AES and DES?
AES and DES have significant security differences due to their design:
Brute Force Attacks
- AES: All AES key sizes (128, 192, 256 bit) are secure against brute-force attacks with current computing capabilities.
- DES: The 56-bit key is vulnerable to brute force attacks. DES keys can be cracked in less than a day using brute force.
Cryptanalysis Resistance
- AES: No practical cryptanalytic attacks have been found on AES so far. Its design resists known attacks like differential and linear cryptanalysis.
- DES: Analytical techniques like differential cryptanalysis can crack DES with less than 247 chosen plaintexts. DES has several theoretical weaknesses.
Round Function Strength
- AES: Multiple nonlinear substitution-permutation rounds provide high diffusion and confusion.
- DES: The round function with just swaps and substitutions is mathematically weaker.
Key Scheduling
- AES: Each round uses a different 128-bit round key derived from the cipher key. This prevents related key attacks.
- DES: All rounds use portions of the same 56-bit key, making it more susceptible to related-key attacks.
Block Size
- AES: The 128-bit block size protects against birthday attacks.
- DES: Smaller 64-bit blocks make it more vulnerable to collision and birthday attacks.
What are the Main Performance Differences?
In addition to much stronger security, AES offers significantly better performance compared to DES when implemented in software:
- Speed: Thanks to its compact design structure, AES performs faster and more efficiently in software. DES's complex Feistel structure impacts software performance.
- Memory: AES requires far less memory than DES during execution. This allows it to fit better in constrained embedded devices.
- Simplicity: AES has a simpler algebraic structure than DES, making it easier to implement securely.
- Hardware Suitability: DES was designed for efficient hardware implementation. AES operates efficiently in both software and hardware across 8/32/64-bit platforms.
- Power Consumption: Software-based AES encryption uses less power than DES, making it suitable for low-power IoT devices.
- Parallelizability: The AES round structure allows more inherent parallelism than DES, enabling performance gains on multi-core CPUs.
The combination of high throughput and low resource usage makes AES the superior choice for general-purpose encryption in modern computer systems and networks.
What are Some Key Application Differences?
AES and DES have found wide adoption in many areas, though AES usage has mostly displaced DES over time:
- Web Security: HTTPS and SSL/TLS protocols use AES encryption to secure web and internet communications. DES was used earlier but is now deprecated.
- Wireless Networks: The WPA2 standard uses AES in Counter mode to encrypt wireless network traffic, while DES and 3DES were used in the insecure WEP standard.
- Data Storage: AES in XTS mode is widely used to encrypt data at rest in full disk encryption products and secure file containers. DES is obsolete for storage.
- Smartcards: The finance industry employs AES encryption in EMV smartcards for credit/debit transactions and mobile payments. DES has been phased out.
- Messaging: AES is used to encrypt emails, chat messages, and voice/video calls in various internet communication applications and protocols, such as Signal and WhatsApp.
- Blockchains: Most cryptocurrencies, like Bitcoin, employ AES-based algorithms for encrypting digital wallets and blockchain data.
Final Thoughts
In summarize, AES and DES are two of the most widely used symmetric encryption algorithms. The AES cipher is the successor to the DES cipher, as it provides stronger security with a longer key length of 128, 192, or 256 bits compared to 56 bits for DES. AES operates on a 4x4 column-major order matrix of bytes, executing several substitution and permutation rounds, while DES operates on a Feistel structure on 64-bit blocks with 16 rounds.
The AES cipher is more secure and computationally efficient than the DES cipher due to its longer key length, making it the preferred choice for modern cryptographic applications when comparing the AES cipher vs DES cipher. With continuing advances in computing power, stronger ciphers like AES will likely be needed going forward to keep data secure.
Frequently Asked Questions
Is AES more secure than DES?
Yes, AES is much more secure than DES due to its stronger design, large key sizes, and resistance against various cryptanalytic attacks. DES is considered insecure for most purposes.
Is AES a replacement for DES?
Yes, AES was designed by NIST to replace DES as the standard symmetric encryption cipher. AES is now used widely instead of DES across industries and applications.
What key sizes does AES support?
AES supports key sizes of 128, 192, and 256 bits. Each size has a different number of rounds: 10, 12, and 14, respectively.
What is the difference between AES-128, AES-192 and AES-256?
These refer to the three different key sizes in AES. The larger the key, the higher the security but reduced performance. 128-bit keys are sufficient for most purposes.
Is DES still used today?
DES usage has declined significantly. Although it may still be present in legacy systems, all modern applications use AES instead of DES. Using DES is not recommended due to its vulnerabilities.
How fast can DES be cracked?
DES has a 56-bit key that can be cracked in under a day through brute force attacks using modern computers. Specialized rigs can crack DES in minutes or hours.
Which is faster, AES or DES?
When implemented in software, AES is significantly faster than DES. It also consumes less memory and power, making it better for performance-constrained devices.
Is 3DES more secure than AES?
Actually, 3DES, which uses up to 3 keys, is less secure than AES. AES, with its larger keys, offers better future-proof security compared to 3DES.
Does AES use a Feistel structure like DES?
No, AES uses a substitution-permutation structure, while DES uses a Feistel structure. This makes AES more efficient in software.

Priya Mervana
 Verified Web Security Experts
Verified Web Security Experts
Priya Mervana is working at SSLInsights.com as a web security expert with over 10 years of experience writing about encryption, SSL certificates, and online privacy. She aims to make complex security topics easily understandable for everyday internet users.