What are Encryption Algorithms: Definition, Types & More
Encryption algorithms are essential tools used to protect sensitive data as it is stored and transmitted. Encryption converts plaintext data into unreadable ciphertext without decrypting it first. Modern encryption standards ensure data stays confidential and tamper-proof.
There are many different types of encryption algorithms, and each has its advantages. The best encryption depends on the use case, priorities, and environment. Factors like speed, strength, key size, block size, standards compliance, and implementation complexity determine which cipher is optimal.
This guide provides an in-depth overview of the most widely used encryption algorithms and their unique characteristics. It explains symmetric algorithms like AES, DES, 3DES, RC4, and Blowfish, as well as asymmetric algorithms including RSA, Diffie-Hellman, elliptic curve cryptography, and digital signatures. Hashing and key derivation functions like bcrypt, scrypt, and Argon2 are also covered.
Key Takeaways
- Encryption algorithms are mathematical functions used to convert plain text into ciphertext to keep data secure.
- Common encryption algorithms include AES, DES, 3DES, RSA, Diffie-Hellman, elliptic curve cryptography, bcrypt, scrypt, and more.
- Symmetric algorithms like AES and DES use the same key for encryption and decryption, while asymmetric algorithms like RSA use a public/private key pair.
- Encryption key length, block size, rounds of transformation, and encryption mode all impact the strength and performance of encryption.
- Encryption should be used alongside other security measures, such as access controls, network security, backups, auditing, and key management.
Symmetric Key Encryption Algorithms
AES (Advanced Encryption Standard)
AES is widely regarded as the gold standard of encryption algorithms. It is a symmetric block cipher standardized by NIST in 2001 to replace DES. AES provides very high security and performance through a combination of protection, implementation cost, and flexibility.
AES encrypts data in 128-bit blocks using three different key lengths: 128, 192, or 256 bits. The algorithm consists of 10 rounds of substitution and permutation for 128-bit keys, 12 rounds for 192-bit keys, and 14 rounds for 256-bit keys. The high number of transformation rounds provides excellent diffusion and confusion.
AES is swift in software and hardware implementations across many platforms. It is commonly used to encrypt data for storage and transmission. The NSA approves AES for protecting classified data up to TOP SECRET. It can be used with a wide range of encryption modes, such as GCM, CCM, CTR, CBC, and XTS.
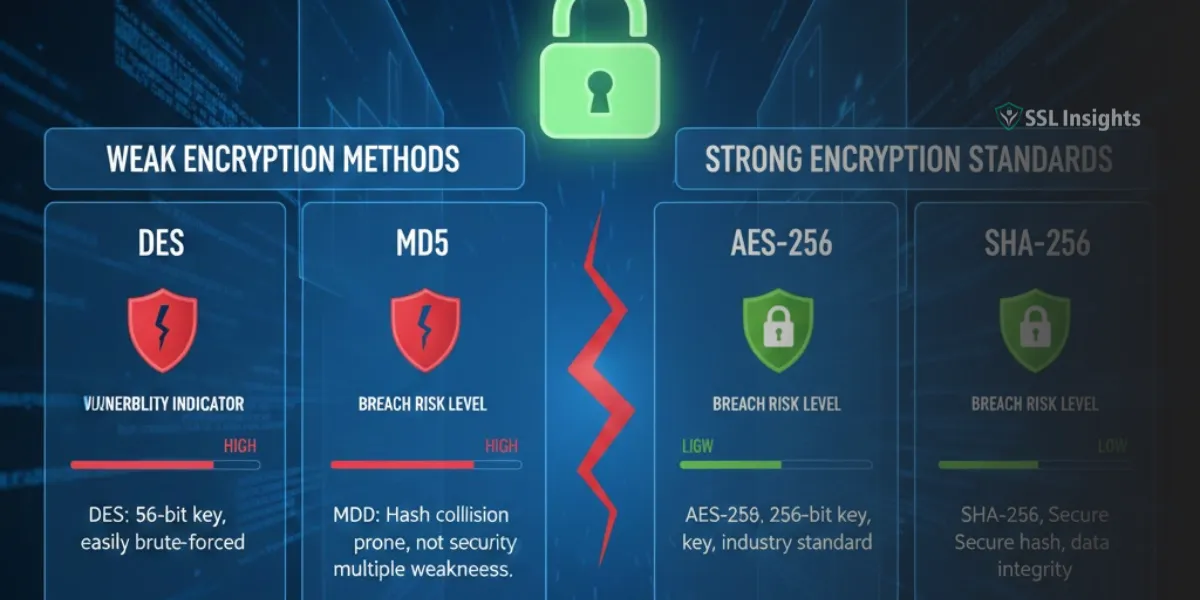
DES (Data Encryption Standard)
DES is a symmetric block cipher standardized in 1977 by NIST. It encrypts data in 64-bit blocks using a 56-bit key. DES was widely adopted but is now considered insecure due to its small key size, which makes it vulnerable to brute-force attacks.
DES transforms the plaintext using 16 rounds of Feistel ciphers, consisting of substitution, permutation, and key mixing. Due to cryptanalysis and its limited key size, DES was replaced by 3DES and then AES.
3DES (Triple DES)
3DES improves upon DES by encrypting each block three times with up to three different keys. There are three keying options:
- Three independent keys (168 bits total)
- Two keys where K1=K3 (112 bits)
- Single key where K1=K2=K3 (56 bits)
The three encryption rounds make 3DES more resistant to attacks than standard DES. However, it is much slower than AES. 3DES is still used in some legacy and payment systems, but AES is recommended for new applications.
RC4 (Rivest Cipher 4)
RC4 is a symmetric stream cipher designed in 1987 by Ron Rivest. It uses variable-length keys from 40 to 2048 bits. RC4 generates a pseudo-random keystream that is XORed with the plaintext to produce ciphertext.
RC4 was widely used in protocols like WEP and WPA to encrypt network traffic. It is very simple and fast in software, but its weaknesses make it vulnerable to attacks. RC4 is now deprecated and not recommended for new systems.
Blowfish
Blowfish is a fast, accessible symmetric block cipher designed in 1993 by Bruce Schneier. It encrypts data in 64-bit blocks with keys up to 448 bits long. Blowfish has a 64-bit block size and uses a Feistel network with 16 rounds.
Blowfish provides strong encryption and was intended to be a drop-in replacement for DES or 3DES. It is used in some legacy and specialized systems but has been superseded by AES in most mainstream applications.
Asymmetric Encryption Algorithms
Asymmetric algorithms use separate public and private keys for encryption and decryption. This allows public keys to be openly shared for encrypting data while private keys are kept secret to decrypt it. Asymmetric encryption is commonly used for key exchange, digital certificates, digital signatures, and message authentication.
RSA (Rivest, Shamir, Adleman)
RSA is the most widely used asymmetric algorithm created in 1977 by Ron Rivest, Adi Shamir, and Leonard Adleman. It enables public-key encryption and is widely used for secure data transmission.
RSA relies on the difficulty of factorizing large prime numbers. Keys are generated using two large prime numbers of hundreds of digits long. The public key can be openly shared, while the private key must be kept secret.
RSA encryption works as follows:
- Generate two large prime numbers, p and q. Compute n = p * q.
- Choose a public exponent e that is coprime to (p-1)*(q-1). The common value is 65,537.
- Compute the private exponent d such that (ed – 1) is divisible by (p-1)(q-1).
- The public key is (n, e). The private key is (n, d).
- To encrypt: Ciphertext = Plaintext^e mod n
- To decrypt: Plaintext = Ciphertext^d mod n
Security depends on the critical length. 1024-bit keys are commonly used and considered secure against attacks. Longer key lengths, like 2048 or 4096 bits, further improve security.
Diffie-Hellman Key Exchange
Diffie-Hellman allows two parties to establish a shared secret key over an insecure channel jointly. It enables key exchange without transmitting the actual keys.
The protocol works as follows:
- Alice and Bob agree on a prime number p and base g. These are public parameters.
- Alice chooses a secret integer a and sends Bob A = g^a mod p
- Bob chooses a secret integer b and sends Alice B = g^b mod p
- Alice computes shared key K = B^a mod p
- Bob computes shared key K = A^b mod p
Now both Alice and Bob have the shared secret K which can be used for symmetric encryption. The math provides key security even if the channel is intercepted.
Elliptic Curve Cryptography (ECC)
Elliptic Curve Cryptography (ECC) is an approach to asymmetric cryptography based on elliptic curves over finite fields. It uses smaller key sizes than RSA to provide equivalent security.
An elliptic curve equation is selected along with base point G. Private keys are random integers. The public key is computed by multiplying the private key with G.
ECC can create faster and more efficient cryptosystems using more minor keys. It is standard in securing internet communications and is implemented in TLS, PGP, and Bitcoin. NIST has standardized elliptic curves for government and commercial applications.
Hashing and Key Derivation Functions
Hashing and essential derivation functions are important components of many encryption systems.
1. Hashing for Message Authentication
Cryptographic hash functions like SHA-2, SHA-3, and BLAKE are used to generate a hash value or message digest from input data. This produces a fixed-length output that is deterministic (same input = same hash) but not reversible.
Hashing is used to verify data integrity and detect tampering. Common uses include digital signatures, message authentication codes (MAC), and blockchain.
2. Bcrypt
Bcrypt is an essential derivation function designed for password hashing. It uses the Blowfish cipher to create password hashes using a salt and variable number of rounds.
Bcrypt introduces a work factor to slow down brute force attacks. The cost parameter allows the compute time to be tuned. Bcrypt remains resistant to attacks even with GPU and custom hardware acceleration.
3. Scrypt
Like bcrypt, scrypt is a password-based essential derivation function. It also uses a salt and adjustable cost parameter.
Scrypt aims to reduce vulnerabilities to hardware brute-force attacks by using a memory-hard construct rather than computing power. This makes it difficult to parallelize and limits the advantages of GPU/FPGA/ASIC hardware.
4. Argon2
Argon2 is a newer key derivation algorithm that was selected as the winner of the Password Hashing Competition in 2015. It uses data-dependent memory access to thwart ASIC/GPU attacks and optimize resistance to side-channel attacks.
Argon2 comes in three versions:
- Argon2d maximizes resistance to GPU attacks.
- Argon2i is optimized against side-channel attacks.
- Argon2id is a hybrid version offering both defenses.
The Argon2 paper guides optimal parameter selection. The parameters allow tuning time and memory complexity to improve security against attacks. Like other password hash functions, Argon2 is designed for slow hashing to hinder brute-force attempts. It prevents parallelization and optimization of hash cracking. Argon2 is the winner of the Password Hashing Competition and is broadly considered one of the most robust password-hashing algorithms available today.
Encryption Modes of Operation
Encryption algorithms are used in different modes to handle encryption of more than one block of data:
- Electronic Codebook (ECB) Mode: Each block is encrypted independently and is not recommended as it does not hide data patterns.
- Cipher Block Chaining (CBC) Mode: Before encryption, each block is XORed with the previous ciphertext block. This method is more secure than the ECB.
- Output Feedback (OFB) Mode: The previous ciphertext is encrypted again and XORed with plaintext. This is stream cipher mode.
- Cipher Feedback (CFB) Mode: This mode shifts the previous ciphertext left, encrypts it, and XORs with plaintext. It is also a stream cipher mode.
- Counter (CTR) Mode: Uses sequential counter block encrypted with a nonce and XORed with plaintext. Parallelizable.
- Galois/Counter Mode (GCM): This method combines counter mode encryption and authentication using a synthetic IV. It is very efficient.
- XTS: Tweakable mode designed for disk encryption. XORs ciphertext with keystream.
Proper mode selection ensures optimal security when encrypting multiple blocks. Authenticated modes like GCM provide data integrity and authenticity.
Implementing Encryption Systems
To implement encryption effectively, algorithms and modes should be combined with other security controls:
- Access controls restrict encryption/decryption to authorized users. Multi-factor authentication improves security.
- Network security protections include firewalls, intrusion prevention systems, and VPNs.
- Auditing and logging of critical management operations.
- Physical security controls for cryptographic hardware and key storage.
- Secure key generation, distribution, rotation, and destruction practices.
- Defense in depth with layered defenses.
- Crypto agility to enable algorithm upgrades.
- Proper design and settings for IVs/nonces, padding, and chaining modes.
- Validation of inputs/outputs and encryption formats.
- Integrity checks and message authentication where needed.
- Secure code free of bugs and vulnerabilities.
- Regular testing and validation of all controls.
Comparing Encryption Algorithms
There is no one “best” encryption algorithm. The optimal choice depends on requirements like:
- Speed: Computational efficiency and hardware requirements.
- Security: Key lengths, vulnerability to attacks, compliance needs.
- Interoperability: Compatibility with protocols, systems, and standards.
- Cost: Licensing, royalties, development/maintenance.
- Algorithm type: Symmetric, asymmetric, hash, MAC, KDF, digital signature.
- Mode of operation: ECB, CBC, OFB, CFB, CTR, GCM, etc.
- Key management: Generation, exchange, storage, expiration, rotation.
- Resource usage: CPU, memory, storage, battery life.
- Implementation: Languages, libraries, and tooling available.
- Crypto agility: Ability to upgrade algorithms when needed.
- Compliance: Adherence to standards like FIPS 140-2, PCI DSS.
Recommendations for Best Practices
Based on the characteristics, strengths, and weaknesses of various algorithms, these are best practices:
- Use AES 128-bit or higher for symmetric encryption. AES-256 is preferred for susceptible data.
- RSA with 2048+ bit keys is standard for asymmetric encryption, digital signatures, and key exchange.
- Use ECDH or ECC for public key encryption if more minor keys are needed.
- SHA-256 hashing provides strong integrity verification and digital signatures.
- PBKDF2, bcrypt, scrypt or Argon2 for password hashing. Tuned to be slow.
- GCM or CCM mode is preferred over ECB/CBC. Use authenticated modes where possible.
- OWASP cryptography guidelines should be followed.
- NIST standards provide trusted, peer-reviewed algorithms.
- Open-source libraries like OpenSSL should be used over custom crypto.
- Keys should be robustly generated and protected throughout their lifecycle.
- Conduct internal and third-party audits to validate proper implementation.
Final Words
Encryption provides fundamental data security services and a last line of defense. Understanding algorithm strengths and weaknesses allows informed decisions when selecting the optimal ciphers for each use case. Proper implementation requires technical knowledge and engineering to ensure encryption is applied effectively without introducing new risks. Cryptographic controls must be combined with robust key management, access control, auditing, and other processes to protect sensitive data thoroughly throughout its lifetime.
Frequently Asked Questions (FAQ) Related to Encryption Algorithms
What is the most secure encryption algorithm?
The Advanced Encryption Standard (AES) is considered the gold standard today. AES-256 provides the highest security through its 256-bit keys. AES has withstood extensive cryptanalysis for over 20 years and is approved to secure classified US government data.
What is better, symmetric, or asymmetric encryption?
Symmetric algorithms like AES provide better performance and are used to encrypt data. Asymmetric encryption is used for key exchange, digital signatures, and public key encryption but needs to be faster for extensive data. Symmetric and asymmetric encryption are often combined in applications.
How does encryption work to secure data?
Encryption uses mathematical algorithms to convert plaintext into ciphertext that looks random and can only be read if decrypted. It protects confidentiality and integrity against unauthorized access. Modern encryption, like AES, relies on techniques like substitution, diffusion, and confusion to make attacks infeasible.
When should you use encryption?
Any sensitive data at rest or in transit should be encrypted. This includes customer data, credentials, trade secrets, and personal information. Regulations like HIPAA and PCI DSS also mandate encryption for protected data. Encryption should be applied commensurate with data sensitivity and risk.
What is the difference between hashing and encryption?
Hashing creates a fingerprint or digest of the input data using a cryptographic one-way function. Encryption scrambles data using a reversible algorithm and key. Hashing is used for integrity verification, while encryption provides confidentiality.
How can I test encryption algorithms?
Encryption libraries like OpenSSL allow testing different algorithms and key lengths to compare security strength and performance. Online encryption tools can also benchmark different ciphers. NIST hosts test vectors for validating FIPS 140-2 cryptographic implementations.

Priya Mervana
 Verified Web Security Experts
Verified Web Security Experts
Priya Mervana is working at SSLInsights.com as a web security expert with over 10 years of experience writing about encryption, SSL certificates, and online privacy. She aims to make complex security topics easily understandable for everyday internet users.