Weak encryption exposes your data to interception, theft, and manipulation by attackers who can break outdated security protocols. Organizations using algorithms like DES or MD5 face regulatory penalties, reputational damage, and financial losses from breaches that stronger encryption methods would prevent.
Why Does Weak Encryption Put Your Data at Risk?
Weak encryption uses outdated algorithms that attackers can crack with modern computing power. When cybercriminals intercept encrypted data, they run brute-force attacks or exploit known vulnerabilities to decrypt sensitive information. According to GRSee's security assessment report (November 2025), cryptographic failures with weak encryption algorithms consistently rank among the top vulnerabilities discovered during security assessments.
The mathematics behind weak encryption creates predictable patterns. Algorithms with short key lengths generate fewer possible combinations, allowing attackers to test every option systematically. A 56-bit key offers roughly 72 quadrillion combinations—sounds secure until you realize modern processors test billions per second.
Business operations grind to a halt when encryption fails. Customer data becomes accessible to competitors and criminals. Payment processing stops. Communication channels compromise confidential negotiations. The damage extends far beyond immediate data loss.
What Happens When Attackers Break Weak Encryption?
Data theft occurs first. Attackers access customer records, financial information, health data, and intellectual property. Your encrypted files become readable plaintext, exposing everything you tried to protect.
Man-in-the-middle attacks become possible. Cybercriminals position themselves between communicating parties, intercepting and potentially altering messages without detection. They read your encrypted emails, capture login credentials, and monitor sensitive transactions.
Regulatory violations follow breaches. GDPR, HIPAA, and PCI DSS mandate strong encryption for specific data types. Companies using weak encryption face fines reaching millions of dollars plus mandatory breach notifications that damage customer trust.
Common consequences include:
- Customer database exposure with names, addresses, and payment details
- Stolen intellectual property and trade secrets
- Compromised authentication systems allowing unauthorized access
- Legal liability from inadequate data protection measures
- Revenue loss during system recovery and reputation repair
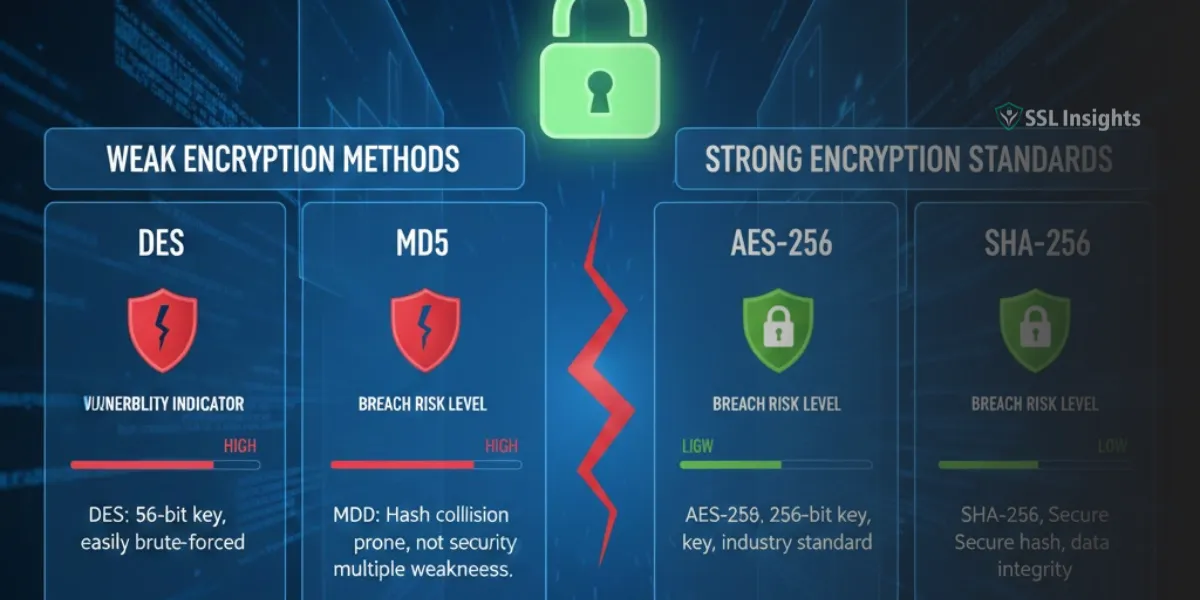
How Do Common Weak Encryption Methods Fail?
DES (Data Encryption Standard) uses 56-bit keys that computers crack in hours. Released in 1977, this algorithm served its purpose for decades but can't withstand current processing capabilities.
MD5 hashing generates collisions where different inputs produce identical outputs. Attackers exploit these collisions to forge digital signatures and bypass authentication systems.
RC4 stream cipher contains biases in its output that reveal patterns in encrypted data. Major browsers disabled RC4 support years ago after researchers demonstrated practical attacks.
WEP (Wired Equivalent Privacy) for WiFi networks breaks within minutes using freely available tools. The protocol's flawed implementation of RC4 combined with weak initialization vectors creates multiple attack vectors.
|
Weak Method |
Key Length |
Time to Crack |
Replacement Standard |
|
DES |
56-bit |
Hours |
AES-256 |
|
3DES |
112-bit effective |
Days |
AES-128/256 |
|
MD5 |
128-bit hash |
Instant (collisions) |
SHA-256 |
|
RC4 |
Variable |
Minutes to hours |
AES-GCM |
|
WEP |
40/104-bit |
Minutes |
WPA3 |
What Security Vulnerabilities Does Weak Encryption Create?
Password databases become targets. Weak hashing allows attackers to reverse-engineer passwords from stolen hash values. They build rainbow tables - precomputed lists matching hashes to plaintext passwords - that crack millions of accounts rapidly.
Certificate forgery undermines trust. When signing certificates use weak algorithms, attackers create fraudulent certificates that browsers accept as legitimate. Users unknowingly connect to malicious sites believing they're secure.
Replay attacks succeed when encryption lacks proper authentication. Attackers capture encrypted messages and retransmit them later to gain unauthorized access or duplicate transactions.
Session hijacking exploits weak key exchange protocols. Attackers predict or calculate session keys, then impersonate legitimate users without needing their passwords.
API endpoints become vulnerable when they transmit data without proper encryption. Attackers monitor network traffic to extract authentication tokens, session identifiers, and sensitive payload data.
How Does Weak Encryption Affect Different Industries?
Healthcare organizations store protected health information requiring HIPAA compliance. Weak encryption of patient records, insurance claims, and medical histories creates liability exposure. Breaches in this sector cost significantly more than other industries due to the sensitive nature of health data.
Financial institutions transmit payment card data under PCI DSS requirements. Using deprecated SSL/TLS versions or weak cipher suites during transactions triggers compliance failures and increases fraud risk. Banks and payment processors face both regulatory penalties and direct financial losses from fraudulent transactions.
E-commerce platforms protect customer payment information and personal details. Weak encryption during checkout processes allows credential stuffing attacks where stolen passwords grant access to accounts across multiple sites. Shopping cart data, order histories, and stored payment methods become accessible.
Government agencies handle classified information with strict security mandates. Weak encryption of sensitive communications or databases violates federal standards and potentially compromises national security. Public sector breaches affect citizen data including tax records, benefits information, and identity documents.
Manufacturing companies protect intellectual property, product designs, and proprietary processes. Industrial espionage through weak encryption allows competitors to steal years of research and development work. Supply chain communications also require strong encryption to prevent tampering.
What Are the Warning Signs of Weak Encryption?
Check your SSL/TLS configuration. Certificates using SHA-1 signatures or supporting SSL 3.0 indicate outdated security. Run scans on SSLInsights.com to identify weak cipher suites and protocol versions.
Review encryption algorithms in your applications. Legacy code often defaults to MD5 or DES for backward compatibility. Audit cryptographic libraries to ensure they disable weak options by default.
Monitor certificate expiration dates and key lengths. Certificates with RSA keys below 2048 bits or validity periods exceeding 13 months fail current standards.
Red flags include:
- SSL 2.0 or 3.0 protocol support
- Cipher suites with "EXPORT" in their names
- Hash algorithms MD2, MD4, MD5, or SHA-1
- Symmetric encryption using DES or 3DES
- RSA keys shorter than 2048 bits
- Self-signed certificates in production environments
- Missing HTTPS enforcement on login pages
- Unencrypted database backups
- Plaintext password storage in configuration files
Penetration testing reveals encryption weaknesses. Security professionals attempt to break your encryption using known attack methods. Failed tests identify which algorithms need immediate replacement.
How Can You Prevent Weak Encryption Vulnerabilities?
Implement AES-256 for symmetric encryption. This algorithm provides strong security with acceptable performance across most applications. Use GCM or CBC mode with proper initialization vectors to prevent pattern analysis attacks.
Deploy RSA-2048 or higher for asymmetric encryption. Better yet, transition to elliptic curve cryptography (ECC) which offers equivalent security with smaller key sizes and faster operations. ECC-384 provides security comparable to RSA-7680 while requiring significantly less computational overhead.
Enable TLS 1.3 for network communications. This protocol removes weak cipher suites, improves handshake security, and encrypts more connection metadata than previous versions. TLS 1.3 reduces latency while strengthening protection against downgrade attacks.
Use SHA-256 or SHA-3 for hashing operations. These algorithms resist collision attacks and provide sufficient output length for security applications. For password storage, implement bcrypt, scrypt, or Argon2 with appropriate work factors.
Rotate encryption keys regularly. Even strong algorithms become vulnerable when keys remain static for years. Implement automated key management systems that handle rotation, storage, and access controls without manual intervention.
What Steps Should You Take to Upgrade From Weak Encryption?
- Inventory your systems: Identify every location where encryption occurs—databases, file storage, network traffic, APIs, mobile apps, and backup systems. Document current algorithms and key strengths. Create a spreadsheet tracking each system's encryption method, last update date, and compliance status.
- Prioritize upgrades: Start with internet-facing systems and customer data. These present the highest risk and often face regulatory requirements. Move to internal systems afterward. Focus first on payment processing, authentication systems, and personally identifiable information storage.
- Test compatibility: Verify that upgraded encryption works with existing systems. Some legacy applications or IoT devices may require workarounds or replacement before you can implement strong encryption. Run parallel systems during transition periods to catch integration issues.
- Update configurations: Disable weak protocols and cipher suites in web servers, load balancers, and applications. Modern TLS libraries often support weak options for backward compatibility—you must explicitly disable them. Edit server configuration files to remove all references to outdated methods.
- Validate changes: Use scanning tools to confirm your improvements. Services like analyzing SSL certificate configurations provide detailed reports on protocol support, cipher strength, and certificate quality. Schedule regular automated scans to catch configuration drift.
- Document standards: Create policies specifying approved encryption algorithms, minimum key lengths, and prohibited weak methods. Include these requirements in development guidelines and vendor contracts. New projects should never implement deprecated encryption methods.
|
Upgrade Phase |
Timeline |
Key Actions |
Success Metrics |
|
Discovery |
Week 1-2 |
Inventory all encryption usage |
Complete system map |
|
Planning |
Week 3-4 |
Prioritize systems, assess compatibility |
Detailed upgrade roadmap |
|
Implementation |
Month 2-4 |
Deploy strong encryption, disable weak protocols |
All critical systems upgraded |
|
Validation |
Month 5 |
Test security, scan for vulnerabilities |
Zero weak encryption findings |
How Often Should You Review Encryption Strength?
Quarterly reviews catch new vulnerabilities. Cryptographic weaknesses emerge as researchers develop better attack methods. What's considered strong today may require upgrading within years. Schedule security team meetings to review current threat intelligence.
Update after major security announcements. When organizations like NIST publish new recommendations or researchers disclose vulnerabilities, assess your systems against updated requirements. Subscribe to security bulletins from CERT, CISA, and relevant industry groups.
Monitor industry standards evolution. Payment card industry standards, healthcare regulations, and government mandates regularly increase minimum encryption requirements. Plan upgrades before deadlines to avoid rushed implementations that introduce errors.
Annual penetration testing validates encryption effectiveness. External security firms attempt to break your encryption using current attack techniques. Their reports identify weaknesses you might miss during internal reviews.
Strong encryption forms your first defense against data breaches. Upgrading from weak algorithms to modern standards protects sensitive information, maintains regulatory compliance, and preserves customer trust. Start by assessing your current encryption methods through tools and security audits, then systematically replace weak implementations with proven strong alternatives like AES-256 and TLS 1.3. Organizations that prioritize encryption upgrades reduce breach costs and demonstrate commitment to data protection.

Priya Mervana
 Verified Web Security Experts
Verified Web Security Experts
Priya Mervana is working at SSLInsights.com as a web security expert with over 10 years of experience writing about encryption, SSL certificates, and online privacy. She aims to make complex security topics easily understandable for everyday internet users.