OpenSSL provides the x509 command to check certificate details directly from your terminal. Run openssl x509 -in certificate.crt -text -noout to view complete certificate information including issuer, validity dates, and subject details.
How Do You Check a Certificate Using OpenSSL?
The primary command displays full certificate details in readable format. Execute openssl x509 -in your_certificate.crt -text -noout where -text outputs human-readable data and -noout suppresses the encoded version.
For PEM format certificates, this command works immediately. DER format requires adding -inform DER flag.
openssl x509 -in certificate.crt -text -noout
This outputs issuer name, subject name, validity period, serial number, signature algorithm, and public key information.
What Information Does the x509 Command Display?
The output includes several critical certificate components. You’ll see the certificate version (typically v3), serial number assigned by the certificate authority, and signature algorithm used.
Issuer details show who created the certificate. Subject information identifies the certificate owner. Validity dates indicate when the certificate becomes active and expires.
Public key details appear with algorithm type and key size. Extensions display additional attributes like subject alternative names and key usage permissions.
| Certificate Field | Description | Example Value |
| Issuer | Certificate authority | CN=Let’s Encrypt Authority |
| Subject | Certificate owner | CN=example.com |
| Valid From | Start date | Jan 15 2025 |
| Valid Until | Expiration date | Apr 15 2025 |
| Serial Number | Unique identifier | 4A:3B:2C:1D |
How Can You Check Certificate Expiration Dates?
Use openssl x509 -in certificate.crt -noout -dates to display only validity dates. This simplified command shows start and end dates without additional details.
openssl x509 -in certificate.crt -noout -dates
- notBefore: Certificate activation date
- notAfter: Certificate expiration date
What Commands Verify Certificate and Key Matching?
Matching certificates with private keys prevents deployment errors. Generate MD5 hashes from both files and compare the output.
openssl x509 -noout -modulus -in certificate.crt | openssl md5 openssl rsa -noout -modulus -in private.key | openssl md5
Identical hash values confirm the certificate and key pair correctly. Different hashes indicate mismatched files that won’t work together.
This verification step catches configuration mistakes before deploying to production servers.
How Do You Check Certificates on Remote Servers?
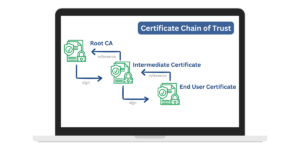
The s_client command connects to remote servers and retrieves their certificates. Run openssl s_client -connect example.com:443 -showcerts to view the complete certificate chain.
openssl s_client -connect example.com:443 -showcerts
According to Netcraft’s January 2026 Web Server Survey, over 1.2 billion websites currently use SSL/TLS certificates for encrypted connections.
Press Ctrl+C to exit after viewing certificate details. The command displays the entire chain from server certificate through intermediate certificates to root certificate.
What Are the Common Certificate Verification Commands?
Beyond basic viewing, OpenSSL offers specialized verification commands. Each serves specific troubleshooting or validation needs.
Check certificate purpose:
openssl x509 -in certificate.crt -noout -purpose
Verify certificate against CA bundle:
openssl verify -CAfile ca-bundle.crt certificate.crt
Display certificate fingerprint:
openssl x509 -in certificate.crt -noout -fingerprint
Show subject alternative names:
openssl x509 -in certificate.crt -noout -ext subjectAltName
The -purpose flag reveals whether the certificate works for SSL server authentication, SSL client authentication, or code signing. Verification against a CA bundle confirms the certificate chain’s validity.
Fingerprints provide unique identifiers for certificate comparison. Subject alternative names list all domains the certificate protects.
How Can You Convert Certificate Formats?
Different systems require different certificate formats. OpenSSL converts between PEM, DER, PKCS#7, and PKCS#12 formats.
PEM to DER:
openssl x509 -in certificate.pem -outform DER -out certificate.der
DER to PEM:
openssl x509 -in certificate.der -inform DER -out certificate.pem
PEM to PKCS#12:
openssl pkcs12 -export -in certificate.pem -inkey private.key -out certificate.p12
| Format | Extension | Use Case |
| PEM | .pem, .crt | Linux servers, Apache |
| DER | .der, .cer | Windows systems, Java |
| PKCS#12 | .p12, .pfx | Windows IIS, email certificates |
| PKCS#7 | .p7b, .p7c | Certificate chains |
PEM files contain Base64 encoded data between BEGIN and END markers. DER files use binary encoding. PKCS#12 bundles certificates and private keys into password-protected archives.
What Troubleshooting Commands Help With Certificate Issues?
When certificates fail, specific commands identify problems quickly. These diagnostic tools pinpoint configuration errors and validation failures.
Test cipher compatibility:
openssl s_client -connect example.com:443 -cipher 'AES256-SHA'
Check certificate chain order:
openssl crl2pkcs7 -nocrl -certfile certificate-chain.pem | openssl pkcs7 -print_certs -noout
Validate certificate dates:
openssl x509 -in certificate.crt -noout -checkend 86400
The -checkend flag accepts seconds and returns exit code 0 if the certificate remains valid for that duration. Use 86400 for one day, 604800 for one week.
Chain verification catches certificates loaded in wrong order. Cipher testing confirms server supports required encryption algorithms.
Missing intermediate certificates cause validation failures in browsers. Testing connections with -showcerts reveals incomplete chains requiring additional intermediate certificate installation.
Checking certificates through command-line tools gives administrators direct control over SSL/TLS validation. Master these OpenSSL commands to diagnose issues faster, verify configurations accurately, and maintain secure connections across your infrastructure.

Priya Mervana
 Verified Web Security Experts
Verified Web Security Experts
Priya Mervana is working at SSLInsights.com as a web security expert with over 10 years of experience writing about encryption, SSL certificates, and online privacy. She aims to make complex security topics easily understandable for everyday internet users.