What Is PKI, and Why Does the Architecture Decision Matter?
PKI (Public Key Infrastructure) is a system of policies, processes, and components used to issue, manage, and revoke digital certificates based on X.509 standards. A PKI binds a public key to an identity – a device, a user, or a service – by having a Certificate Authority (CA) sign that binding with its own private key. The architecture determines who operates that CA, who trusts it by default, and what policies govern it.
The decision matters because trust is not universal. A certificate trusted by your organization’s laptops may be rejected by a partner’s firewall. A certificate trusted by every web browser may expose your internal infrastructure to CA/Browser Forum policy changes that have nothing to do with your security requirements. Getting the architecture right from the start avoids costly migrations later.
What Is Internal PKI?
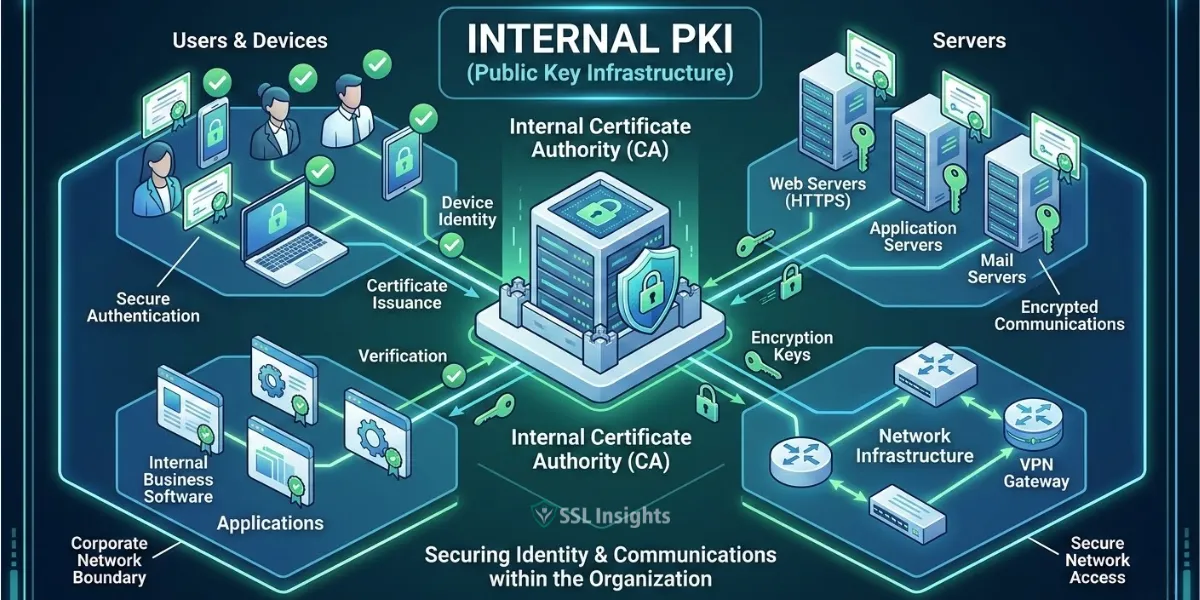
The most common deployment pattern follows a two-tier hierarchy. An offline root CA sits at the top and issues certificates only to intermediate CAs. Those intermediate CAs then issue certificates to end entities – servers, laptops, IoT devices, or application services. The offline root is never connected to the network, which means a compromise of an intermediate CA does not automatically compromise the root. Microsoft’s own internal PKI follows this two-tier design according to Microsoft’s CA hierarchy planning documentation.
Internal PKI is the right choice when:
- Your use cases are fully contained within the organization (device authentication, internal TLS, Zero Trust network access)
- You need to issue certificates in high volumes without per-certificate costs
- Your compliance requirements demand direct control over certificate policies
- You are managing IoT devices, containers, or microservices where short-lived certificates are preferred
The main drawback is operational burden. Your team owns everything – the HSM for root key storage, the CRL/OCSP infrastructure, the certificate lifecycle tooling, and the incident response procedures if the CA is compromised. For organizations without dedicated PKI expertise, that overhead is significant.
What Is External PKI?
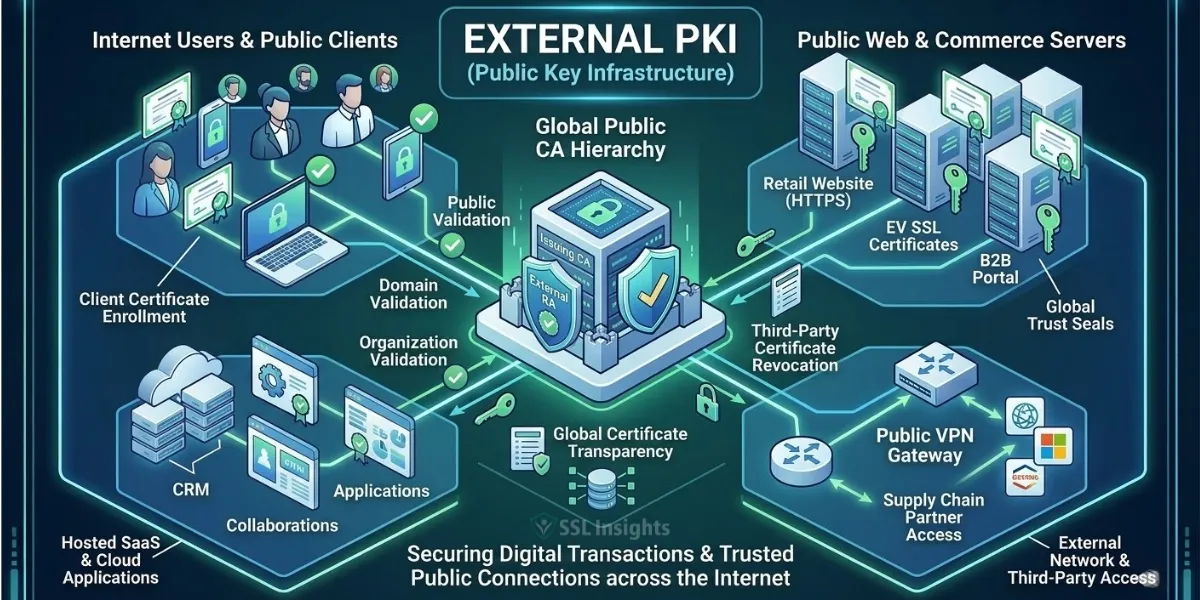
The CA/Browser Forum sets the rules that govern these CAs, covering everything from domain validation procedures to maximum certificate validity periods. These rules exist to protect the internet – but they also mean external CAs operate on timelines and policies that your organization does not control.
External PKI is the right choice when:
- You need certificates trusted by anyone on the internet without custom configuration
- Your primary use case is securing public-facing web servers, APIs, or customer-facing portals
- You have a small number of certificates and prefer managed issuance over building infrastructure
- Your team has limited PKI expertise and the simplicity of pay-per-certificate is preferable
Because external CA certificates are trusted by default in browsers, they are also subject to forced revocations or policy changes that may affect your systems unexpectedly. Understanding the difference between a self-signed certificate and a trusted CA certificate helps clarify why that trust chain matters.
What Is Federated PKI?
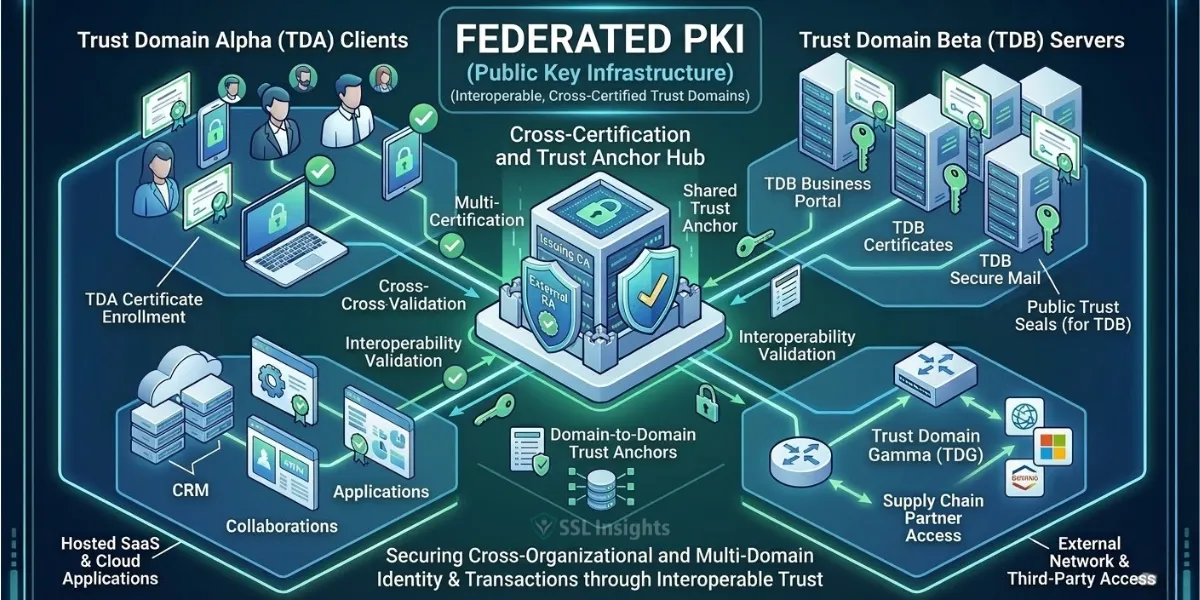
This architecture is most often used in three scenarios:
- Multi-cloud deployments: A company running workloads across AWS and GCP can operate separate CAs in each cloud. By federating the two CAs, services in AWS can authenticate directly to services in GCP using mutual TLS (mTLS), without routing traffic through a VPN.
- Industry consortiums: Regulated industries like healthcare, finance, or defense often operate federated PKIs where member organizations share a common root of trust managed by a central governance body.
- Mergers and acquisitions: When two companies join, federating their existing PKI environments is faster and lower risk than migrating all certificates to a single CA hierarchy.
Federated PKI does not grant automatic trust. Each participating organization must explicitly configure its systems to trust the federated roots. The upside is that each organization retains full control over its own certificate policies while still enabling secure cross-domain authentication.
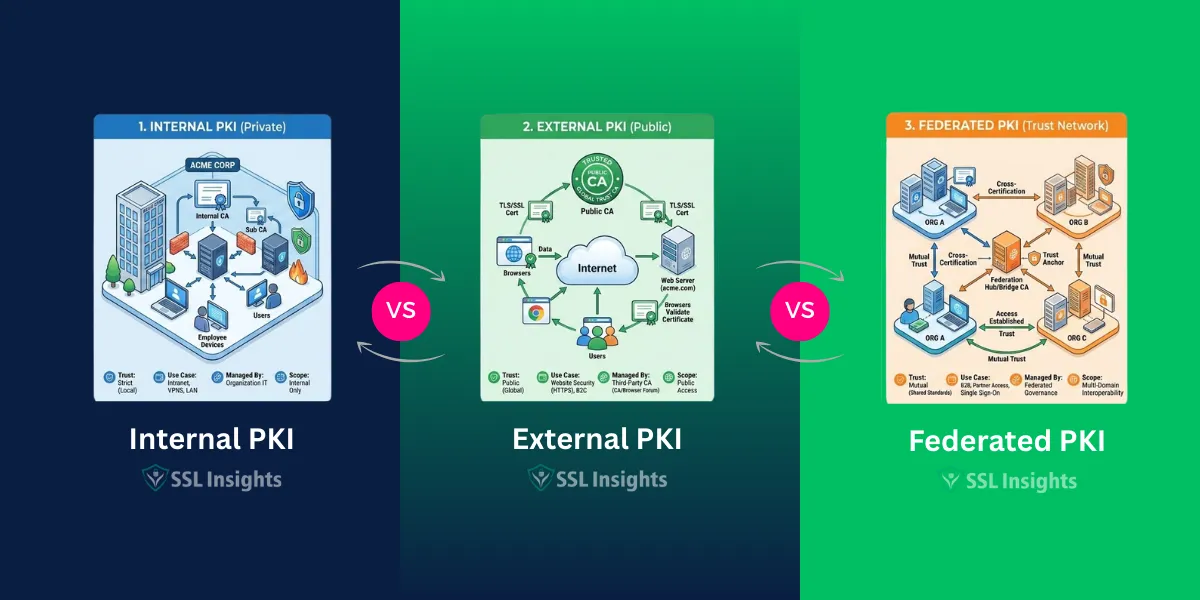
How Do the Three Architectures Compare: Internal vs External vs Federated PKI
| Attribute | Internal PKI | External PKI | Federated PKI |
| Default browser trust | No | Yes | No |
| Control over certificate policy | Full | Limited | Shared |
| Cost at scale | Low (fixed infrastructure) | High (per-certificate) | Medium |
| Cross-organization trust | No | Yes (via shared public root) | Yes (explicit federation) |
| Operational complexity | High | Low | Medium-High |
| Best fit | Enterprise internal systems | Public-facing web services | Multi-org or multi-cloud |
| Governance | Organization | CA/Browser Forum | Consortium or bilateral agreement |
Can You Use More Than One PKI Model?
Most large organizations use all three models simultaneously. That is not redundancy – it reflects the different trust requirements of different certificate use cases.
A typical enterprise setup looks like this: an internal PKI handles device authentication, internal service-to-service TLS, and Zero Trust access policies. An external PKI issues certificates for customer-facing websites and public APIs. A federated arrangement connects internal PKI environments across business units, acquired companies, or cloud providers.
The key is mapping each use case to the model that satisfies the trust requirement at the lowest operational cost. Using external PKI for internal services wastes money and introduces dependency on CA/Browser Forum policies that don’t apply to closed systems. Using internal PKI for public-facing web servers means every user needs custom root configuration – which is impractical.
Understanding how public and private keys underpin each of these models helps clarify why the CA hierarchy matters regardless of which architecture you choose.
What Are the Common Mistakes Organizations Make When Choosing a PKI Model?
The most common error is selecting a PKI architecture based on immediate needs rather than a five-to-ten year projection. An organization that starts with a handful of internal servers may find itself needing to issue certificates to thousands of containers, mobile devices, and IoT endpoints within two years. An internal CA built for the initial use case often lacks the automation, API integration, and scalability to handle that growth.
A second mistake is underestimating the operational requirements of internal PKI. Running a private CA requires maintaining the offline root, managing CRL and OCSP services, monitoring certificate expiration at scale, and having an incident response plan for CA key compromise. Organizations that build internal PKI without dedicated PKI staffing or a managed PKI platform often experience outages caused by expired certificates or misconfigured trust chains.
A third mistake is using external PKI for internal use cases. Certificates from public CAs are subject to 90-day or shorter validity periods under CA/Browser Forum guidance, and revocations can happen automatically based on policy triggers that have nothing to do with your environment. Internal systems need the stability and control that only an internal or federated model can provide.
Match Your PKI Architecture to Your Trust Scope
The right PKI model is not the most sophisticated one – it is the one that satisfies your actual trust requirements with the fewest operational trade-offs. Internal PKI wins when control and scale matter more than default browser trust. External PKI wins when reaching any internet client without configuration is the priority. Federated PKI wins when multiple independent environments need to trust each other without surrendering policy autonomy.
Start by mapping your certificate use cases to a trust scope: internal-only, internet-facing, or cross-organization. That single question will point you to the correct architecture. From there, evaluate whether you want to own the infrastructure, use a managed platform, or work with a commercial CA to provide the root while you operate the intermediate. Audit your current certificate inventory before you build anything – most organizations discover more active certificates than they expected, and that inventory shapes every architectural decision that follows.
Frequently Asked Questions (FAQs)
What is the main difference between internal and external PKI?
Internal PKI uses a private CA that your organization controls entirely. Certificates it issues are only trusted by systems you configure to trust them. External PKI uses a publicly trusted CA whose root is already embedded in browsers and operating systems, so no additional configuration is needed for public-facing trust. Internal PKI offers more control; external PKI offers broader default acceptance.
When should an organization use federated PKI instead of internal PKI?
Federated PKI is appropriate when trust must extend beyond a single organization while each party still needs independent control over its own certificate policies. If you are connecting systems across cloud providers, partner organizations, or merged business units, federation allows mutual authentication without forcing one organization to subordinate its CA to another’s root.
Is federated PKI the same as a public CA?
No. A public CA issues certificates trusted by default in all major browsers and operating systems. A federated PKI establishes mutual trust only between explicitly configured participants. Systems outside the federation do not automatically trust federated roots. Federated PKI is closer to an internal PKI in terms of default trust scope – it just extends that scope across multiple organizations.
Can a small business run its own internal PKI?
Yes, but the operational burden was historically a barrier for smaller teams. Cloud-managed PKI platforms have reduced that barrier significantly – some charge per device rather than requiring full infrastructure ownership. For an organization with fewer than 50 devices, external PKI is often simpler. For larger environments or those with strict compliance requirements, internal PKI managed via a hosted platform is a practical option.
What happens if the root CA in an internal PKI is compromised?
A root CA compromise is a serious incident. All certificates issued by CAs in that hierarchy are no longer trustworthy. The standard response involves revoking the compromised root, re-building the CA hierarchy from a new root, and re-issuing all affected certificates. This is precisely why the root CA should always be kept offline and protected by a hardware security module (HSM). The offline root model limits the blast radius of an intermediate CA compromise and prevents the root from being attacked over the network.
How does federated PKI work in a multi-cloud environment?
Each cloud environment runs its own CA. The federation is configured by adding each CA’s root certificate to the trusted roots bundle of the other CA. Services in Cloud A use certificates from Cloud A’s CA, and services in Cloud B trust both their own CA and Cloud A’s CA. Mutual TLS connections between clouds authenticate using those certificates without requiring a shared CA or a VPN tunnel.

Priya Mervana
 Verified Web Security Experts
Verified Web Security Experts
Priya Mervana is working at SSLInsights.com as a web security expert with over 10 years of experience writing about encryption, SSL certificates, and online privacy. She aims to make complex security topics easily understandable for everyday internet users.