The unable_to_get_issuer_cert_locally node js error means Node.js cannot verify the certificate chain of the remote server you are connecting to - typically because your system is missing the root or intermediate CA certificate needed to complete that validation. This happens during HTTPS requests, npm installs, and any API call that uses SSL/TLS. The fix depends on the root cause: missing CA certificates, a self-signed cert, a corporate proxy intercepting traffic, or an outdated system trust store. This guide walks through every solution in order of most to least common.
What Is the UNABLE_TO_GET_ISSUER_CERT_LOCALLY Error?
The UNABLE_TO_GET_ISSUER_CERT_LOCALLY error is an OpenSSL error code that Node.js surfaces when it cannot locate the issuer certificate for a server's TLS certificate in its trusted CA store. The error breaks the chain of trust: Node.js receives the server's certificate, attempts to trace it back to a trusted root CA, and fails because one link in that chain is absent locally.
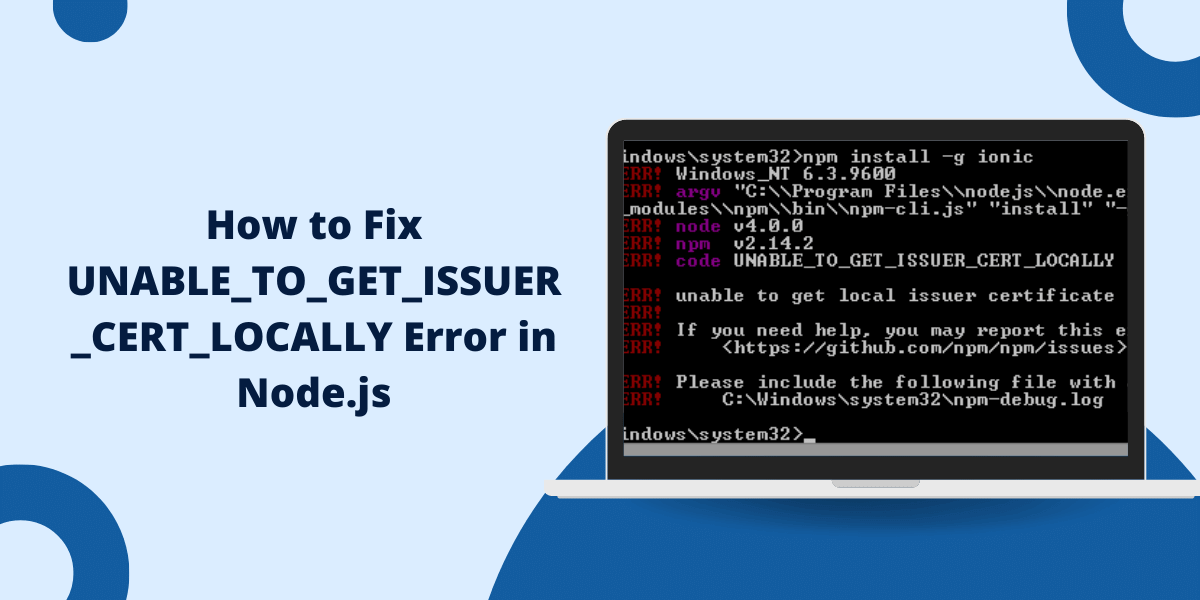
You will typically see it appear in one of these forms:
- npm ERR! code UNABLE_TO_GET_ISSUER_CERT_LOCALLY
- npm ERR! errno UNABLE_TO_GET_ISSUER_CERT_LOCALLY
- Error: unable to get local issuer certificate
- ssl error: unable_to_get_issuer_cert_locally
This is not a remote server problem in most cases. The certificate is usually valid - your local environment simply does not have the CA certificates required to verify it. Incomplete certificate chains are a documented industry problem: according to SSL Insight's June 2025 report on SSL/TLS configuration across 134,380 major websites, 28.7% failed to follow best practices, with incomplete certificate chains listed as one of the primary failure types.
What Causes the npm ERR! Code UNABLE_TO_GET_ISSUER_CERT_LOCALLY?
Four root causes account for the vast majority of occurrences:
- Missing root or intermediate certificates - Your system's CA bundle does not include the certificate authority that signed the server's cert.
- Self-signed certificate on the target server - A self-signed certificate node js error occurs because Node.js does not recognize self-signed certs as trusted by default.
- Corporate proxy or firewall SSL inspection - Many enterprise networks intercept HTTPS traffic and re-sign it with an internal CA. That internal CA is not in Node.js's trust store, which causes a corporate proxy ssl certificate node validation failure.
- Outdated CA certificate bundle - System CA bundles are not updated automatically on all platforms. An outdated bundle may be missing newer root certificates added by CAs in the past few years.
How to Fix the UNABLE_TO_GET_ISSUER_CERT_LOCALLY Error: 7 Solutions
Work through these solutions in order. Most cases are resolved by solutions 1 or 2.
1. Update npm and Node.js
Outdated versions of Node.js ship with older CA bundles. Updating to the current LTS release is often all it takes to resolve the node js ssl error fix for servers using recently issued certificates.
npm install -g npm
nvm install --lts
After updating, re-run the failing command before trying any other fix.
2. Install or Reinstall System CA Certificates
If your system's CA bundle is missing certificates, reinstall it. This is the most common fix for the update ca certificates linux node js error on server environments and CI pipelines.
On Debian/Ubuntu Linux:
sudo apt-get install --reinstall ca-certificates sudo update-ca-certificates
On macOS, you can update certificates using:
brew install ca-certificates
On Windows, open Certificate Manager (certmgr.msc) and import the required root certificate into the Trusted Root Certification Authorities store.
3. Use the NODE_EXTRA_CA_CERTS Environment Variable
The NODE_EXTRA_CA_CERTS environment variable is the cleanest solution when you have a specific CA certificate to add but do not want to modify your system's global trust store. According to the Node.js official TLS documentation, this variable instructs Node.js to extend its built-in CA list with the certificates in the specified PEM file, without replacing any existing trusted CAs.
export NODE_EXTRA_CA_CERTS=/path/to/your/ca.crt
Restart your Node.js process after setting the variable. This approach works well for Docker containers, CI/CD pipelines, and local development environments where you cannot modify system-level certificate stores.
4. Add a Self-Signed Certificate to Your Trusted Store
If the target server uses a self-signed certificate node js error-triggering cert, add it directly to your system's trusted CA store rather than disabling verification globally.
On Linux or macOS:
sudo cp server.crt /usr/local/share/ca-certificates/ sudo update-ca-certificates
On Windows, open Certificate Manager, navigate to Trusted Root Certification Authorities, and import the .crt file manually.
Download the certificate from the server using OpenSSL if you do not have the file:
openssl s_client -connect yourserver.com:443 -showcerts 2>/dev/null | openssl x509 -outform PEM > server.crt
5. Configure npm to Use a Custom CA Certificate
For npm cafile custom CA certificate setups - common in corporate environments with internal certificate authorities - point npm directly to your CA file:
npm config set cafile /path/to/your/ca.crt
Obtain the CA certificate file from your network administrator. This setting persists in your .npmrc file and applies to all future npm operations in that environment.
6. Disable SSL Verification in Development Only
The npm config set strict-ssl false approach and setting node js rejectUnauthorized false in your HTTPS request options are both viable for isolated development environments, but must never be used in production. Disabling SSL verification removes the protection that prevents man-in-the-middle attacks.
For npm:
npm config set strict-ssl false
For node js https request ssl error scenarios in development code:
javascript
const https = require('https');
const options = {
hostname: 'example.com',
port: 443,
path: '/',
method: 'GET',
rejectUnauthorized: false // Development only - never use in production
};
const req = https.request(options, (res) => {
res.on('data', (d) => process.stdout.write(d));
});
req.end();
Remember to revert this before deploying. The disable ssl verification node js development shortcut is a debugging tool, not a long-term fix.
7. Check Your Network and Proxy Configuration
If you are behind a corporate proxy, the corporate proxy ssl certificate node issue may require configuring npm's proxy settings alongside the CA certificate fix from Solution 5. Set both proxy addresses in npm:
npm config set proxy http://your-proxy-url:port npm config set https-proxy http://your-proxy-url:port
Also confirm that the proxy's root CA certificate is installed using Solution 3 or 5 - proxy configuration alone will not resolve the certificate trust error.
How to Prevent the Unable to Get Local Issuer Certificate Node.js Error
The node js ssl error production environment is almost always preventable with these standing practices:
- Keep your system's CA certificate bundle updated, especially on Linux servers and Docker base images.
- Use NODE_EXTRA_CA_CERTS in deployment pipelines rather than disabling verification.
- Never commit rejectUnauthorized: false to a shared codebase - use environment variables to control this flag instead.
- Test HTTPS connectivity in staging environments that mirror production CA trust stores before deploying.
Frequently Asked Questions
Why does Node.js reject SSL certificates that browsers accept?
Browsers use the operating system's certificate store and often have fallback retrieval mechanisms for missing intermediate certificates. Node.js uses OpenSSL with its own bundled CA list and performs stricter chain validation with no automatic intermediate fetching - so a chain that browsers tolerate will still fail in Node.js if a link is missing locally.
What is the difference between unable to get local issuer certificate and CERT_UNTRUSTED?
UNABLE_TO_GET_ISSUER_CERT_LOCALLY means Node.js cannot find the issuing CA in its trust store at all. CERT_UNTRUSTED means the CA is found but is not marked as trusted. The first typically requires adding a missing CA certificate; the second may require explicitly trusting an existing one.
Is it safe to set rejectUnauthorized to false in production?
No. Setting rejectUnauthorized: false disables certificate chain verification entirely, making your application vulnerable to man-in-the-middle attacks. It is acceptable only in isolated local development environments. Use NODE_EXTRA_CA_CERTS instead for any environment that connects to real data.
How do I check which CA certificates Node.js currently trusts?
Run node -e "console.log(require('tls').rootCertificates)" to print the full list of trusted root CAs bundled with your Node.js version. Compare this against the CA that issued the server's certificate to identify the missing entry.
Why does this error appear after moving to a Docker container?
Minimal Docker base images (such as node:alpine) ship with a stripped-down CA bundle. Install the full CA bundle with apk add --no-cache ca-certificates && update-ca-certificates in your Dockerfile, or use NODE_EXTRA_CA_CERTS to supply the specific certificate your application needs.
Can a corporate firewall cause the unable_to_get_issuer_cert_locally npm error?
Yes. SSL-inspecting firewalls and proxies replace the server's original certificate with one signed by an internal CA. Because that internal CA is not in Node.js's trust store, every outbound HTTPS request fails with this error. The fix is to export the firewall's root CA and add it via NODE_EXTRA_CA_CERTS or npm config set cafile.

Priya Mervana
 Verified Web Security Experts
Verified Web Security Experts
Priya Mervana is working at SSLInsights.com as a web security expert with over 10 years of experience writing about encryption, SSL certificates, and online privacy. She aims to make complex security topics easily understandable for everyday internet users.