Converting SSL certificate formats is a standard task in web server configuration. CRT and CER files typically contain X.509 certificates, PEM uses Base64 encoding with header/footer text, DER uses binary encoding, and PFX (also called PKCS#12) bundles certificates with private keys in a password-protected container.
Most web servers and applications require specific certificate formats. Apache and Nginx prefer PEM, while Windows servers use PFX. Understanding these conversions prevents deployment errors and ensures secure HTTPS connections.
What Is the Difference Between Certificate Formats?
Certificate formats differ in encoding method and file structure. PEM (Privacy Enhanced Mail) stores certificates in Base64 ASCII encoding between "-----BEGIN CERTIFICATE-----" and "-----END CERTIFICATE-----" markers. DER (Distinguished Encoding Rules) contains the same certificate data in binary format without text markers.
CRT and CER files are certificate containers that can use either PEM or DER encoding. PFX files combine certificates, intermediate chains, and private keys into a single encrypted archive protected by a password.
Common Format Characteristics:
| Format | Encoding | Contains Private Key | Common Extensions | Primary Use |
|---|---|---|---|---|
| PEM | Base64 ASCII | Optional (separate file) | .pem, .crt, .cer, .key | Linux/Unix servers |
| DER | Binary | No | .der, .cer | Java applications |
| PFX/PKCS#12 | Binary | Yes (bundled) | .pfx, .p12 | Windows servers, email clients |
| CRT | PEM or DER | No | .crt | Generic certificate file |
| CER | PEM or DER | No | .cer | Microsoft convention |
According to SSL.com's 2025 certificate deployment analysis, PEM format accounts for approximately 68% of web server certificate installations due to its compatibility with Apache and Nginx.
How Do You Convert CRT to PEM Format?
CRT files already contain certificate data in either PEM or DER encoding. First, determine which encoding your CRT file uses by opening it in a text editor.
If you see "-----BEGIN CERTIFICATE-----" text, the file is already in PEM format. Simply rename it from .crt to .pem or use it directly. If the file shows binary gibberish or unreadable characters, it uses DER encoding and requires conversion.
For DER-encoded CRT files:
openssl x509 -inform DER -in certificate.crt -out certificate.pem
This command reads the DER-formatted certificate and outputs PEM encoding. The -inform flag specifies input format, while the default output is PEM.
For already PEM-encoded CRT files:
cp certificate.crt certificate.pem
Or just use the .crt file directly - most applications accept both extensions for PEM-encoded certificates.
How Do You Convert DER to PEM Format?
DER to PEM conversion changes binary encoding to Base64 text encoding. OpenSSL handles this conversion through its x509 utility.
Run this command:
openssl x509 -inform DER -in certificate.der -out certificate.pem
The resulting PEM file contains the same certificate data wrapped in Base64 encoding with BEGIN/END markers. You can verify successful conversion by opening the output file - it should display readable ASCII text starting with "-----BEGIN CERTIFICATE-----".
For private keys in DER format:
openssl rsa -inform DER -in privatekey.der -out privatekey.pem
The rsa utility converts key files specifically, while x509 handles certificate files.
How Do You Convert CER to PFX Format?
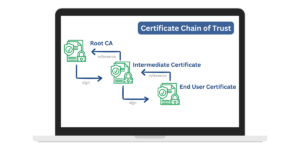
Converting CER to PFX requires both the certificate file and its corresponding private key file. PFX format bundles these components into a single password-protected archive.
The conversion command combines three elements: certificate, private key, and optional intermediate certificates.
Basic conversion (certificate + private key):
openssl pkcs12 -export -out certificate.pfx -inkey privatekey.key -in certificate.cer
You'll be prompted to create a password for the PFX file. This password protects the private key during storage and transfer.
Including intermediate certificates:
openssl pkcs12 -export -out certificate.pfx -inkey privatekey.key -in certificate.cer -certfile intermediate.cer
The -certfile parameter adds certificate authority (CA) intermediate certificates to complete the chain of trust. Most production environments require this complete chain.
Converting PEM-formatted components:
If your CER file is PEM-encoded and your key is separate:
openssl pkcs12 -export -out certificate.pfx -inkey privatekey.pem -in certificate.cer -certfile ca-bundle.crt
Windows IIS and Exchange servers require PFX format for certificate installation. The bundled format simplifies deployment by keeping all certificate components in one file.
What Tools Can Perform Certificate Format Conversions?
OpenSSL remains the standard command-line tool for certificate conversions across platforms. It ships with most Linux distributions and macOS, and Windows users can install it through package managers or standalone installers.
OpenSSL advantages:
- Free and open-source
- Available on Windows, Linux, and macOS
- Handles all common certificate formats
- Scriptable for batch conversions
- Preserves certificate integrity
GUI alternatives for non-technical users:
- Windows Certificate Manager: Built-in utility for importing/exporting certificates
- KeyStore Explorer: Java-based GUI for managing certificates and keystores
- XCA: Cross-platform certificate management with conversion features
- SSL.com's online converter: Web-based tool for simple conversions
Online converters work for non-sensitive development certificates but expose private keys to third parties. Never upload production private keys to online conversion services.
Why Do Different Systems Require Different Certificate Formats?
Server software and operating systems evolved with different security standards and encoding preferences. Apache and Nginx originated in Unix environments where text-based configuration files were standard, making PEM's ASCII format a natural fit.
Microsoft's IIS server uses Windows Certificate Store, which expects binary PFX format with bundled private keys. Java applications use keystores that prefer DER encoding for efficiency.
Platform format preferences:
- Apache/Nginx: PEM (.pem, .crt, .key files separately)
- IIS/Exchange: PFX (.pfx or .p12 with password)
- Tomcat/Java: JKS or PKCS12 keystore formats
- HAProxy: Combined PEM file (certificate + key in one file)
- F5 Load Balancers: PEM or PFX depending on configuration
Email encryption (S/MIME) and code signing use PFX because these applications need portable certificates with private keys. The password protection prevents unauthorized key extraction.
How Do You Verify Certificate Conversion Results?
Verification confirms the converted certificate contains correct data and maintains validity. OpenSSL provides commands to inspect certificate details.
Check PEM certificate contents:
openssl x509 -in certificate.pem -text -noout
This displays certificate details including issuer, subject, validity dates, and public key. Compare these values to your original certificate.
Verify PFX file contents:
openssl pkcs12 -in certificate.pfx -info -noout
You'll need to enter the PFX password. The output shows included certificates and keys.
Test private key match:
openssl x509 -noout -modulus -in certificate.pem | openssl md5
openssl rsa -noout -modulus -in privatekey.pem | openssl md5
Both commands should produce identical MD5 hashes. Matching hashes confirm the certificate and private key form a valid pair.
Common validation checks:
- Certificate subject matches your domain
- Validity dates cover your intended usage period
- Issuer matches your certificate authority
- Private key modulus matches certificate modulus
- File extension matches actual encoding
What Are Common Certificate Conversion Errors?
Incorrect format specification causes most conversion failures. OpenSSL requires explicit input format declaration when handling DER files.
"unable to load certificate" error:
This typically means wrong -inform flag. DER files need -inform DER specified:
openssl x509 -inform DER -in cert.der -out cert.pem
"No certificate matches private key" error:
The certificate and private key don't form a pair. Verify you're using the correct key file that was generated with your certificate signing request (CSR). Check modulus values match using the verification commands above.
PFX password errors:
PFX files require password protection. Always use strong passwords and store them securely. You can create a PFX without password using -nodes flag, but this is insecure for production use.
Missing intermediate certificates:
Browsers show security warnings when the certificate chain is incomplete. Always include intermediate certificates when creating PFX files using the -certfile parameter.
Permission denied errors:
OpenSSL needs read access to input files and write access to the output directory. Check file permissions and run with appropriate privileges.
Converting certificate formats is straightforward once you identify source and target encodings. Keep private keys secure during conversion, verify results before deployment, and maintain backups of original certificate files. Most SSL/TLS deployment issues stem from format mismatches that these conversions resolve.
Frequently Asked Questions (FAQs)
What is the difference between PEM and DER formats?
PEM (Privacy Enhanced Mail) is a text-based encoding format for X.509 certificates and cryptographic keys, whereas DER (Distinguished Encoding Rules) is a binary encoding format. PEM files are human-readable and typically larger, while DER files are more compact but not human-readable.
Can I convert a DER-encoded certificate to PKCS#12 format?
Yes, you can convert a DER-encoded certificate, along with the private key and certificate chain, to the PKCS#12 format using the openssl command-line tool. This allows you to bundle the certificate, private key, and additional data into a single file.
What is the purpose of the PKCS#7 format?
The PKCS#7 (Public Key Cryptography Standards #7) format is a container format used to store and transmit digital certificates, certificate revocation lists (CRLs), and other related data. It is commonly used to exchange certificates and CRLs between different systems or applications.
Can I convert a PKCS#12 file back to individual PEM or DER formats?
Yes, you can extract individual components (certificates, private keys, etc.) from a PKCS#12 file and convert them to PEM or DER formats using the openssl command-line tool.
What is the benefit of using the PKCS#12 format?
The PKCS#12 format provides a secure way to bundle multiple certificates, private keys, and additional information into a single file, often protected by a password. This makes it convenient for storing and distributing sensitive cryptographic data while ensuring its integrity and confidentiality.

Priya Mervana
 Verified Web Security Experts
Verified Web Security Experts
Priya Mervana is working at SSLInsights.com as a web security expert with over 10 years of experience writing about encryption, SSL certificates, and online privacy. She aims to make complex security topics easily understandable for everyday internet users.