Certificate Transparency (CT) logs are publicly accessible, append-only records that document every SSL/TLS certificate issued by participating Certificate Authorities. When a CA issues a certificate, it must submit that certificate to at least one CT log before browsers like Chrome will trust it. This mechanism makes it nearly impossible for a rogue certificate to exist in the wild without detection, because the entire issuance record is exposed to public scrutiny. Domain owners, security researchers, and automated monitoring tools can query these logs at any time to verify that no unauthorized certificate has been issued for their domain.
Certificate Transparency (CT) log: A cryptographically secured, publicly auditable ledger maintained by independent log operators that records TLS certificate issuances. Each log uses a Merkle tree data structure to ensure entries cannot be altered or deleted without detection. Any browser or monitoring tool can verify a certificate's inclusion proof against the log in milliseconds.
How Do CT Logs Actually Work?
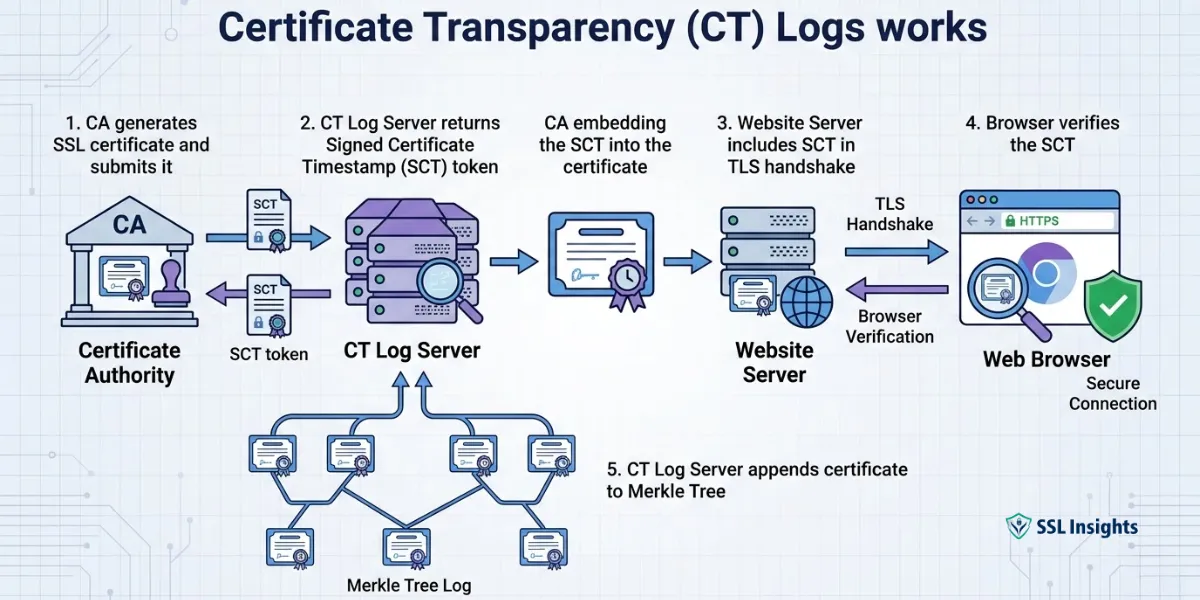
CT logs operate on a submit-sign-publish model that creates an auditable chain of evidence before any certificate reaches an end user.
Here is the sequence of events that occurs every time a CA issues a certificate:
- The CA generates the certificate and submits it to one or more CT log servers.
- Each log server returns a Signed Certificate Timestamp (SCT) - a cryptographic promise that the certificate will be incorporated into the log within a defined merge delay (typically 24 hours).
- The CA embeds the SCT in the certificate, or delivers it via TLS extension or OCSP stapling.
- The browser verifies the SCT during the TLS handshake. If no valid SCT is present, Chrome rejects the connection with an ERR_CERTIFICATE_TRANSPARENCY_REQUIRED error.
- The log server permanently adds the certificate to its Merkle tree, making it publicly searchable.
The Merkle tree structure is what gives CT logs their tamper-evident properties. Each new entry updates the tree's root hash, and any attempt to modify a historical record would produce a detectable inconsistency. Log monitors continuously cross-check these root hashes across multiple independent logs to catch any divergence.
According to Google's Certificate Transparency policy documentation, Chrome has required CT compliance for all publicly trusted certificates since April 2018, and certificates lacking valid SCTs are hard-blocked in the browser rather than presenting a user-override warning.
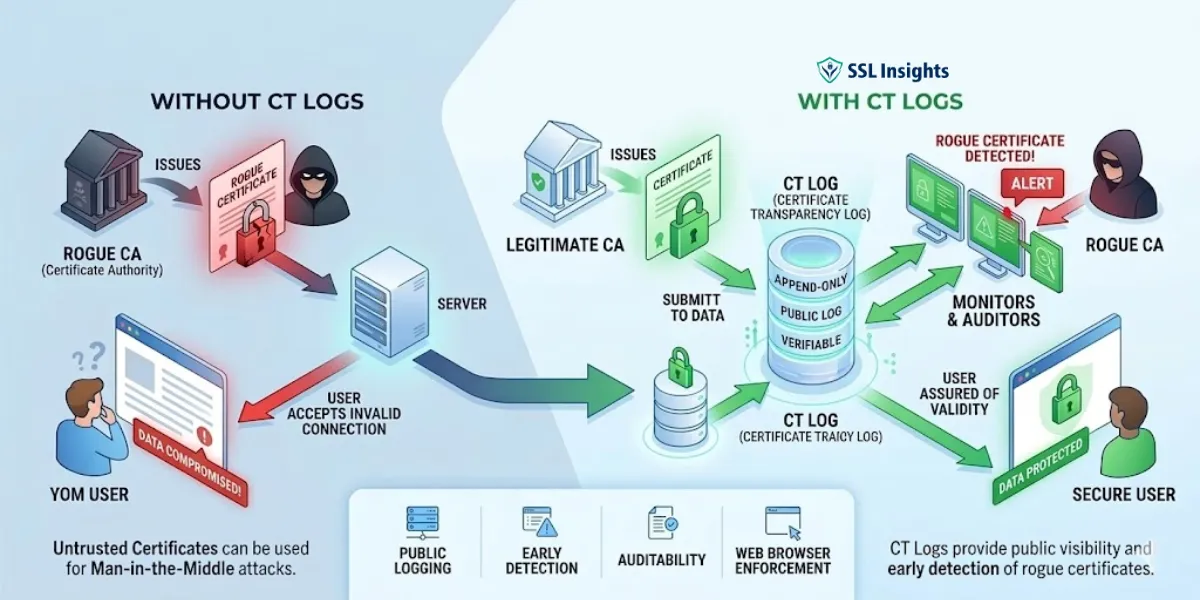
What Problem Did CT Logs Solve?
Before Certificate Transparency existed, the CA ecosystem had a critical blind spot: there was no way to know what certificates had been issued for a given domain. A compromised or misbehaving CA could issue a certificate for yourbank.com and nobody - including the domain owner - would be alerted.
This vulnerability became concrete in 2011 when the Dutch CA DigiNotar was compromised and issued fraudulent certificates for Google, Mozilla, and other high-profile domains. These certificates enabled man-in-the-middle attacks against Iranian users before the breach was discovered weeks later. The delay occurred precisely because there was no public record to monitor. CT logs were designed specifically to eliminate that detection window - any certificate now appears in a public log within hours of issuance.
A second high-profile incident in 2015 involved a Symantec sub-CA issuing unauthorized test certificates for Google domains without Google's knowledge. Google engineers discovered the problem through CT log monitoring, not through traditional revocation systems.
Who Operates CT Logs and Can They Be Trusted?
CT logs are operated by independent organizations, meaning no single entity controls the entire ecosystem. As of 2025, approved CT log operators include Google, Cloudflare, DigiCert, Sectigo, and Let's Encrypt, among others. Each operator runs one or more logs independently, and browsers typically require SCTs from at least two different logs to reduce reliance on any single party.
| Log Operator | Notable Logs | Status |
| Argon, Xenon | Trusted | |
| Cloudflare | Nimbus | Trusted |
| DigiCert | Yeti, Nessie | Trusted |
| Sectigo | Sabre, Mammoth | Trusted |
| Let's Encrypt | Oak | Trusted |
The trust framework for CT logs is maintained by browser vendors. Google publishes a list of CT logs trusted by Chrome, and each log must meet operational and auditing standards to remain on that list. A log that goes offline, stops accepting submissions, or fails an audit can be removed, and SCTs from that log will stop being counted toward CT compliance.
This multi-operator model means that even if one log operator were compromised, the other logs would still hold a consistent record. An attacker would need to corrupt every trusted log simultaneously - and do so without any of the continuous monitors detecting the discrepancy.
How Can You Monitor CT Logs for Your Domain?
Monitoring CT logs for unauthorized certificate issuances is one of the most practical security measures a domain owner can take. Several tools and services make this straightforward.
crt.sh - operated by Sectigo - is a free public search interface that queries multiple CT logs and returns every certificate ever issued for a given domain or subdomain pattern. Searching for %.yourdomain.com returns all wildcard and subdomain certificates, which is where unauthorized issuances most frequently appear.
Automated monitoring options include:
- Certspotter (by SSLMate): Sends email or webhook alerts whenever a new certificate appears in CT logs for your monitored domains.
- Facebook's Certificate Transparency Monitoring: Sends alerts via Facebook if your domain appears in a CT log unexpectedly.
- Google Search Console: Alerts site owners to certificate issues that may affect search indexing.
For organizations managing many domains, integrating CT log monitoring into a SIEM or security operations workflow via the Certificate Transparency API provides real-time data ingestion. According to the certificate transparency development documentation, log entries become searchable within minutes of the merge delay expiring, meaning your monitoring system can detect an unauthorized certificate before most users would ever encounter it.
The most common mistake organizations make here is assuming their CA handles monitoring on their behalf. CAs submit certificates to logs - they do not proactively alert you if someone else's CA issues a certificate for your domain. That monitoring responsibility falls entirely on the domain owner.
What Is the Difference Between CT Logs and Certificate Revocation?
CT logs and certificate revocation solve fundamentally different problems, and understanding the distinction matters for anyone managing TLS infrastructure.
Certificate Transparency answers the question: Was this certificate issued, and when? It creates a permanent public record that cannot be retroactively deleted. CT logs do not stop a bad certificate from being used - they make the issuance visible so action can be taken.
Certificate revocation answers the question: Should this certificate still be trusted right now? Mechanisms like CRL (Certificate Revocation List) and OCSP (Online Certificate Status Protocol) tell browsers whether a certificate has been invalidated after issuance. Revocation is the response to a problem; CT logging is what helps you detect the problem in the first place.
| Feature | CT Logs | Certificate Revocation |
| Purpose | Detect unauthorized issuances | Invalidate compromised certificates |
| Timing | Pre-issuance / at issuance | Post-discovery |
| Public record | Yes, permanent | Distributed, not permanent |
| Browser enforcement | Hard-block if missing | Soft-fail in most browsers |
| Who acts | Domain owner monitors | CA or domain owner requests revocation |
The two systems are complementary. CT logs surface the certificate; revocation removes trust in it. Understanding what a certificate authority does helps clarify why neither system alone is sufficient - CAs must participate in both to maintain trust.
Does CT Logging Apply to All Certificates?
CT log requirements apply to publicly trusted TLS certificates - those chained to root CAs included in major browser trust stores. Private or internal PKI certificates issued by an organization's own CA for internal use are not required to appear in public CT logs, and typically should not, since logging them would expose internal hostnames and infrastructure details to public search.
A few important scope boundaries:
- Let's Encrypt certificates: All are logged automatically. Let's Encrypt submits every certificate to multiple logs as part of its issuance pipeline.
- Wildcard certificates: Logged just like single-domain certificates. The wildcard notation (e.g., *.example.com) appears in the log, which is why CT monitoring for wildcards catches unauthorized subdomains.
- EV certificates: Were the first certificate type required to be CT-logged, predating the broader mandate.
- Expired certificates: Remain in the log permanently. The log is append-only; expiry does not remove an entry.
The permanent nature of CT logs is particularly valuable for post-incident forensics. If a compromise is discovered months after it occurred, investigators can query CT logs to determine exactly when a fraudulent certificate was issued, which CA signed it, and whether any SCTs were obtained from legitimate logs.
Building CT Log Monitoring Into Your Security Workflow
Certificate Transparency logs represent a genuine architectural shift in how the CA trust model operates - moving from a system where mis-issuance was invisible to one where every certificate leaves a permanent, auditable trail. The passive protection CT provides is real: the mere existence of the public log deters many forms of CA misbehavior.
The active protection, though, only materializes if someone is actually watching. Set up automated CT log monitoring for every domain your organization controls, treat unexpected certificate alerts as security incidents requiring immediate investigation, and use CAA DNS records to authorize specific CAs. As the ecosystem continues tightening enforcement - with shorter certificate lifetimes and stricter log policy requirements expected through 2025 and beyond - organizations that already have monitoring in place will be far better positioned to respond when an unauthorized issuance appears.
Frequently Asked Questions (FAQs)
What happens if a CA fails to submit a certificate to CT logs?
Browsers that enforce CT - Chrome being the primary example - will reject the certificate during the TLS handshake and show an error to the user. The site becomes inaccessible until the CA reissues a properly logged certificate. CAs that repeatedly fail CT submission requirements can face removal from browser trust stores.
Can CT logs be used to find subdomains of a target domain?
Yes, and this is a well-known dual-use aspect of CT logs. Security researchers use CT log data for reconnaissance and asset discovery. Attackers can do the same. Organizations should treat their CT log footprint as public information and ensure internal hostnames are never issued public certificates.
How long does it take for a certificate to appear in CT log search tools?
After a CA submits a certificate to a log, the SCT is returned immediately. The certificate becomes publicly searchable through tools like crt.sh typically within minutes to a few hours, depending on the log's merge delay and the search tool's indexing frequency.
Do CT logs prevent certificate mis-issuance, or just detect it?
CT logs detect mis-issuance - they do not prevent it. A CA can still issue a fraudulent certificate and submit it to CT logs. The value is that the issuance becomes publicly visible almost immediately, enabling domain owners or security researchers to spot it and initiate revocation before significant harm occurs.
What is a Signed Certificate Timestamp (SCT) and where is it stored?
An SCT is a cryptographic receipt from a CT log server confirming that a certificate was submitted for logging. It can be embedded directly in the certificate during issuance, delivered via a TLS extension during the handshake, or stapled in an OCSP response. Browsers check for a valid SCT as part of understanding the SSL/TLS handshake process to confirm CT compliance before completing the connection.
Are there privacy concerns with CT logs being publicly accessible?
Yes. Because CT logs are fully public, any certificate issued for a domain - including internal-looking names accidentally issued as publicly trusted certificates - becomes searchable globally. Organizations should audit their certificate issuance practices to avoid exposing internal infrastructure in public logs. This concern has driven interest in DNS-based CAA records, which let domain owners specify which CAs are authorized to issue certificates for their domain.

Priya Mervana
 Verified Web Security Experts
Verified Web Security Experts
Priya Mervana is working at SSLInsights.com as a web security expert with over 10 years of experience writing about encryption, SSL certificates, and online privacy. She aims to make complex security topics easily understandable for everyday internet users.