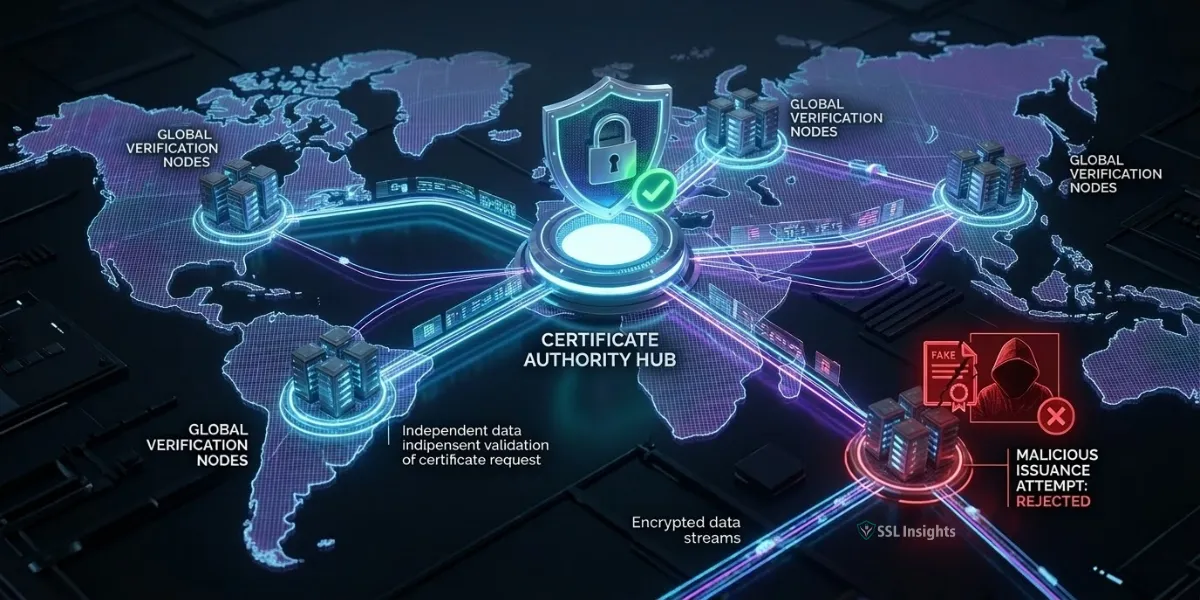
Multi-Perspective Issuance Corroboration (MPIC) is a certificate issuance security standard that requires Certificate Authorities to verify domain ownership from multiple, geographically separate network locations before issuing an SSL/TLS certificate. Instead of a single validation check that an attacker can manipulate by hijacking local network traffic, MPIC demands agreement from several independent vantage points simultaneously.
As of September 15, 2025, MPIC is mandatory for all publicly trusted TLS certificates under CA/Browser Forum Ballot SC-067 - meaning every CA that issues certificates trusted by browsers must comply or lose that trust status.
What Problem Does MPIC Solve?
MPIC exists because traditional single-perspective domain validation is vulnerable to BGP hijacking attacks. Border Gateway Protocol (BGP) is the routing system that directs traffic across the internet. When an attacker manipulates BGP routes in a localized region, they can intercept or redirect the validation traffic a Certificate Authority sends to confirm domain ownership. If that CA relies on just one validation check from one location, the attacker wins - they obtain a certificate for a domain they don't control.
This is not a theoretical concern. Research from Princeton University's Center for Information Technology Policy demonstrated real-world BGP-based attacks that successfully fooled CA domain validation in the wild. Because BGP hijacks tend to be localized - affecting only a portion of the internet at a given time - an attacker only needs to manipulate traffic in one region to deceive a CA using a single validation perspective. MPIC closes that window by requiring simultaneous agreement from multiple regions, forcing an attacker to compromise geographically distributed network points at once.
To understand the concept intuitively: a single referee in a stadium can be fooled by a bad angle. But when four officials positioned across the field all agree on the same call, the chance of a coordinated error drops dramatically. The same logic applies here.
How Does MPIC Work Technically?
When a CA receives a certificate request under MPIC, it performs two types of checks from multiple independent network locations:
- Domain Control Validation (DCV): The CA verifies that the certificate requester controls the domain. This includes HTTP file-based challenges, DNS-based challenges using the ACME protocol, and DNS TXT record verification.
- CAA Record Checks: The CA confirms it is authorized to issue certificates for the domain by reading the Certificate Authority Authorization (CAA) record in DNS.
Both checks run not just from the CA's primary server but also from remote network perspectives - servers placed in distinct geographic regions, each registered under a different Regional Internet Registry (RIR). The five RIRs are ARIN (North America), RIPE NCC (Europe), APNIC (Asia-Pacific), LACNIC (Latin America), and AFRINIC (Africa).
Per CA/Browser Forum Baseline Requirements Section 3.2.2.9, each DCV and CAA check must use at least two independent perspectives separated by a minimum of 500 kilometers and registered under different RIRs. During full enforcement, CAs typically use one primary perspective plus five remote perspectives - and at least four of those six must agree for issuance to proceed. If results differ across locations, the certificate request fails or is flagged for investigation.
| Enforcement Phase | Start Date | Behavior |
| Reporting-only mode | February 18, 2025 | MPIC runs but doesn't block issuance |
| Soft enforcement | March 15, 2025 | CAs must implement; blocking at CA discretion |
| Full enforcement | September 15, 2025 | Certificate denied if perspectives disagree |
Since September 2025, any certificate issued without corroborated multi-perspective validation is non-compliant and can be rejected by major browser trust stores.
What Is the Quorum Model and Why Does It Matter?
MPIC doesn't require unanimous agreement across all perspectives - it uses a quorum model. This is a practical allowance for benign network inconsistencies without weakening the security guarantee.
The quorum model works as follows:
- A CA selects a total number of perspectives - typically six (one primary, five remote).
- A minimum threshold of those perspectives must return consistent, corroborating results.
- If the number of non-corroborating responses exceeds the permitted threshold, the certificate is blocked.
For six total perspectives, at least five must agree. So a single non-corroborating result - perhaps due to temporarily slow DNS propagation in one region - won't automatically block a valid request. But if an attacker has poisoned routes in one or two locations, the remaining perspectives catch the inconsistency.
This quorum design matters for system administrators because MPIC is not zero-tolerance for minor validation variance - but it is zero-tolerance for coordinated manipulation. If your certificate issuance is failing under MPIC, the problem is almost certainly a genuine infrastructure issue, not a minor timing quirk. Start with the infrastructure review, not a CA support ticket.
Why Did the CA/Browser Forum Make MPIC Mandatory?
The CA/Browser Forum formally codified MPIC in Ballot SC-067 (version 3), which passed in August 2024 with support from Google, Apple, Mozilla, and major CAs. According to Princeton University's CITP research on MPIC's development (July 2024), BGP-based validation attacks have been demonstrated successfully in the real world at scale - including against CAs processing millions of certificates per day. The research began in 2015 when BGP hijacking was first theorized as a PKI threat, with Let's Encrypt pioneering multi-perspective validation in production by 2020.
Google's Chrome Root Program played a particularly active role in the timeline. Google Trust Services had already deployed its own internal multi-perspective validation before the ballot passed. The Chrome Root Program's requirements drove the industry timeline by establishing that CAs not implementing MPIC would face review for root store inclusion - a consequence no CA could afford.
The mandate also extends beyond TLS. Ballot SMC010 extended MPIC requirements to S/MIME certificate validation, so email signing certificates now face the same multi-perspective standards. If your organization uses S/MIME for digitally signed email, the same infrastructure review applies.
How Does MPIC Affect Website Owners and Sysadmins?
For most organizations, MPIC operates entirely behind the scenes. But certain infrastructure configurations can break the corroboration process and cause certificate issuance to fail - sometimes with unclear error messages.
Review these configurations before any upcoming certificate renewal:
- Geoblocking and regional firewall rules: If your server blocks inbound connections from specific countries or IP ranges, remote validation perspectives from those regions will fail. Allowlist the IP ranges your CA uses for MPIC checks.
- DNS providers with geographic restrictions: Some DNS providers reject queries from outside a defined region. Because MPIC requires DNS lookups from multiple RIR regions, a DNS provider that blocks international queries prevents successful corroboration.
- GeoDNS configurations: If your DNS returns different IP addresses depending on the requester's location, remote perspectives may receive different DNS answers than the primary perspective - which looks identical to a BGP attack from MPIC's standpoint.
- CDN caching of validation tokens: HTTP-based DCV challenges place a file at a specific URL path. If your CDN caches or blocks that path, remote perspectives may not be able to fetch the token.
- Premature deletion of DCV records: With single-perspective validation, you could remove a DNS TXT record as soon as your primary CA server confirmed it. Under MPIC, all remote perspectives also need to read that record. Removing it too early causes failures at remote nodes.
If you manage domain control validation records for multiple domains, audit each against this list before the next renewal window.
How Does MPIC Compare to RPKI?
MPIC and Resource Public Key Infrastructure (RPKI) are complementary security mechanisms - but they protect different layers of the same threat landscape.
| Feature | MPIC | RPKI |
| Attack type addressed | Localized BGP hijacks (equally-specific prefix attacks) | Globally invalid BGP route advertisements |
| Where protection applies | Certificate issuance validation | Internet routing infrastructure |
| Who configures it | Certificate Authorities | ISPs and network operators |
| Protects against global attacks? | No | Yes |
| Protects against localized attacks? | Yes | Limited |
RPKI signs BGP route announcements at the source, preventing globally invalid routes from propagating. But equally-specific prefix attacks - where an attacker announces a route just as specific as the legitimate one - can slip past RPKI because both routes appear valid. MPIC catches these localized manipulations because different network perspectives, by definition, route through different paths.
The combination of both mechanisms provides layered defense. RPKI hardens routing infrastructure; MPIC hardens certificate issuance. Network teams managing DNS security and certificate infrastructure should treat both as baseline requirements rather than advanced options for high-security environments only.
What Should You Do If Certificate Issuance Fails After MPIC Enforcement?
If a certificate renewal fails after September 2025, work through these steps in order:
- Request an error report from your CA that identifies which perspectives failed and what those failures returned. Most enterprise CAs provide this detail in their portal or via API.
- Test DNS resolution for your domain from multiple geographic regions using a tool like DNSChecker.org to identify whether your authoritative name server returns consistent answers globally.
- Verify that your DCV challenge file (for HTTP-based validation) or DNS TXT record is accessible from international IP addresses. Temporarily disable geoblocking rules during the validation window if needed.
- Check your CDN configuration to confirm that validation URL paths bypass caching and return live responses.
- Contact your DNS provider to confirm it serves queries from all five RIR regions without geographic filtering.
Once you correct the underlying infrastructure issue, re-submit the certificate request. You don't need to generate a new CSR unless the CA requires it for the specific failure type.
MPIC Is Now the Baseline - Not the Exception
MPIC represents the certificate ecosystem's formal response to a proven, real-world attack class. For organizations running standard web infrastructure with globally accessible DNS and servers, the September 2025 enforcement deadline passed without incident. But for anyone managing infrastructure with strict geographic access controls, internal name servers, or aggressive CDN caching, the MPIC requirements create new failure modes worth understanding before a certificate expires.
Review your DNS accessibility, firewall rules, and CDN configuration against the checklist in this article - and test validation behavior from multiple regions before your next renewal cycle. Finding an MPIC incompatibility during a planned review is far less disruptive than discovering it during an emergency renewal.
Frequently Asked Questions (FAQs)
Does MPIC require any action from website owners?
Most website owners will notice no changes. The CA handles all multi-perspective validation automatically. Action is only needed if your infrastructure blocks international connections, restricts DNS queries by geography, or uses configurations that return inconsistent responses across regions. Review the infrastructure list in this article and test DNS resolution behavior before your next certificate renewal.
Does MPIC slow down certificate issuance?
MPIC can introduce minor delays because the CA must coordinate checks across multiple global servers before issuing a certificate. In practice, the added latency is typically a matter of seconds, not minutes. Automated certificate management workflows using ACME may see slightly longer issuance times, but the delay is not significant enough to disrupt normal operations or automated renewal pipelines.
Does MPIC apply to private or internal certificates?
No. MPIC is a requirement for publicly trusted TLS and S/MIME certificates - those issued by CAs whose root certificates are included in browser and OS trust stores. Private CA certificates used internally for intranets, internal APIs, or internal tooling are not subject to CA/Browser Forum Baseline Requirements and therefore do not require MPIC.
What is the Open MPIC Project?
The Open MPIC Project is an open-source implementation of the MPIC protocol developed by Princeton University researchers. It provides CAs with a reference API and cloud-based infrastructure (including an AWS Lambda implementation) to run remote validation perspectives without building proprietary systems from scratch. The CA/Browser Forum formally referenced the Open MPIC Project in SC-067 ballot discussions as one viable implementation path for CAs of any size.
Can MPIC be bypassed if a certificate was issued before the enforcement deadline?
Certificates issued before February 18, 2025 under previous validation rules remain valid until they expire or are revoked - MPIC does not retroactively invalidate them. But any renewal or new issuance after the enforcement deadline must comply. Short-lifetime certificates like 90-day certificates from Let's Encrypt mean most sites have already cycled through at least one MPIC-compliant issuance since full enforcement began.
Does MPIC apply to wildcard and multi-SAN certificates?
Yes. Wildcard certificates covering *.example.com still require domain validation, and that validation must go through multi-perspective checks. Each domain name in a multi-SAN certificate is also independently validated through MPIC, so a certificate covering five different domains triggers five separate multi-perspective validation runs. Plan for this if you use certificate management automation - each SAN adds validation overhead.

Priya Mervana
 Verified Web Security Experts
Verified Web Security Experts
Priya Mervana is working at SSLInsights.com as a web security expert with over 10 years of experience writing about encryption, SSL certificates, and online privacy. She aims to make complex security topics easily understandable for everyday internet users.