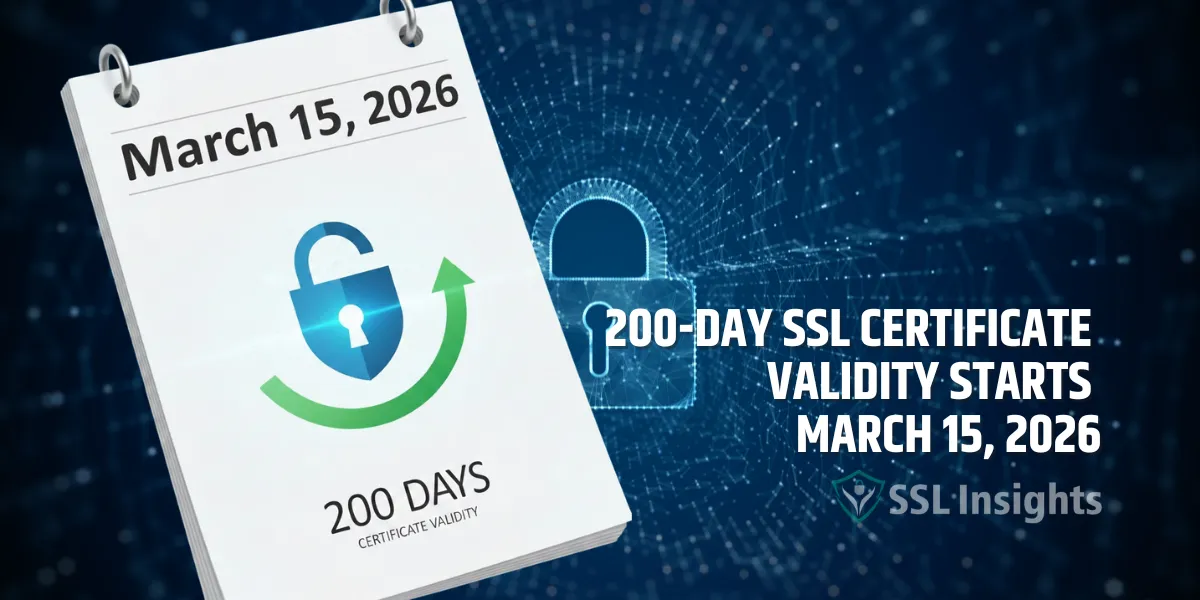
The dual-EKU TLS certificate removal ends the longstanding practice of issuing a single public certificate with both Server Authentication and Client Authentication extended key usages. From mid-2026, public CAs will only issue certificates containing the serverAuth...