No malware was installed. No corporate email was compromised. The attacker never touched your firewall.
Smishing – SMS phishing – has become the highest-converting attack method in the cybercriminal toolkit, and most businesses still don’t have a single countermeasure in place. Not a training program. Not a verified sender policy. Not a smishing simulation. The defenses that companies spent years building around email remain almost entirely absent on the channel employees check 96 times a day on average, according to Asurion’s mobile behavior research.
This article breaks down why smishing has surged so sharply, how modern attacks are structured, what weaknesses in enterprise wireless infrastructure make them worse, and what a real defense plan looks like in practice.
The Numbers Behind the Smishing Surge
Businesses now rely on enterprise SMS platforms like Infobip to run automated customer communications, internal alerts, and two-factor authentication at scale. Platforms like this are built with enterprise-grade security, reliability, and global delivery capabilities that make them a trusted choice for critical communications. They also provide advanced features such as message authentication, delivery tracking, and compliance support, helping organizations maintain consistent and secure communication with both employees and customers.
That scale also introduces a broader attack surface. Employees and customers receive hundreds of legitimate branded texts every week, which conditions them to act on SMS from institutions they trust. Over time, that familiarity lowers skepticism and shortens decision-making, creating an environment where malicious messages can blend in more easily. Attackers exploit that conditioned behavior precisely because it works.
SMS Phishing Click Rates vs. Email
The click-through gap between smishing and email phishing is not marginal. According to Keepnet Labs’ 2026 Smishing Statistics report, SMS phishing achieves click-through rates of 19-36%, compared to 2-4% for email phishing. That’s roughly ten times more effective – on a channel most security teams actively ignore.
The financial damage is already in the hundreds of millions. The U.S. Federal Trade Commission’s 2024 Consumer Sentinel Network Report found that Americans lost $470 million to smishing scams in 2024, five times the losses recorded in 2020. The volume of attacks has declined slightly, which means attackers are getting more effective per message sent, not less.
Businesses specifically are squarely in the crosshairs. Keepnet Labs’ 2026 report found that 76% of organizations were targeted by smishing in a single year. And yet only 32% run smishing simulations, even though 79% offer formal email phishing training. That’s a training gap so large it’s essentially a standing invitation.
Why SMS Is a High-Risk Attack Channel
Part of why SMS converts so well comes down to the medium itself. Mobile screens hide full URLs. Text messages strip away the extended context that makes email phishing easier to spot. And SMS feels immediate and personal in a way that corporate email doesn’t. Asurion’s mobile behavior research found that people check their phones 96 times a day on average – a text that says “urgent: verify your account” arrives in a mental space where quick, instinctive responses are the norm. There’s no spam folder, no email client, no automatic link-scanning tool standing between the message and the tap.
To see how smishing fits into the broader phishing picture, the numbers are just as striking – phishing as a category remains the leading initial access vector in breaches globally, and SMS has become its fastest-growing channel.
How Smishing Attacks Work: The Modern Playbook
Modern smishing campaigns are not improvised. They’re industrialized.
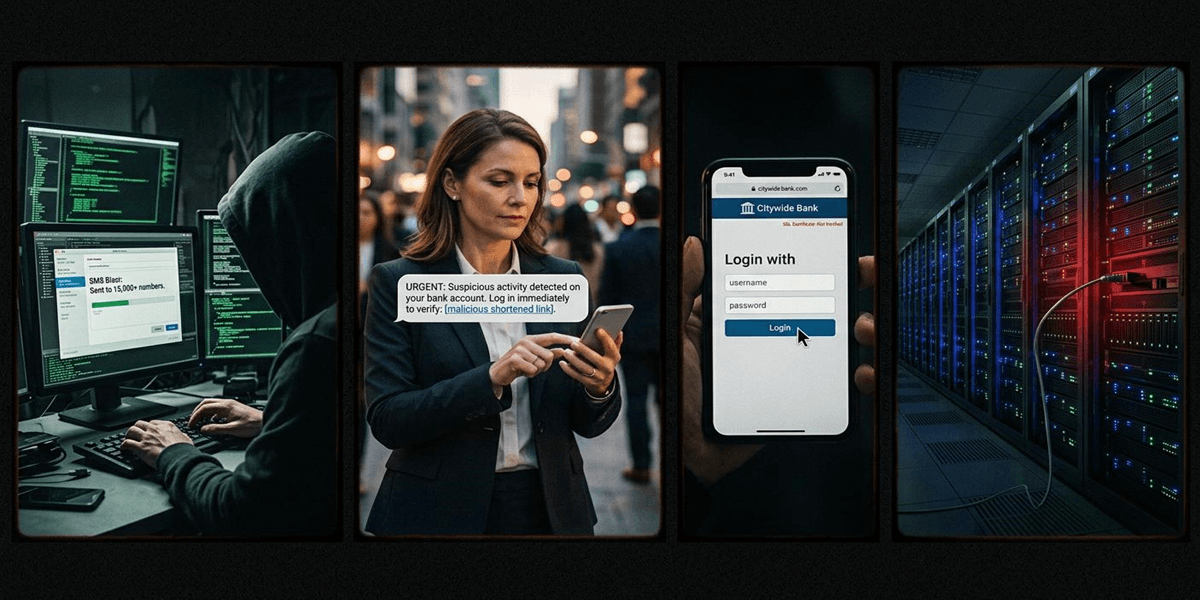
How Attackers Execute Smishing Campaigns
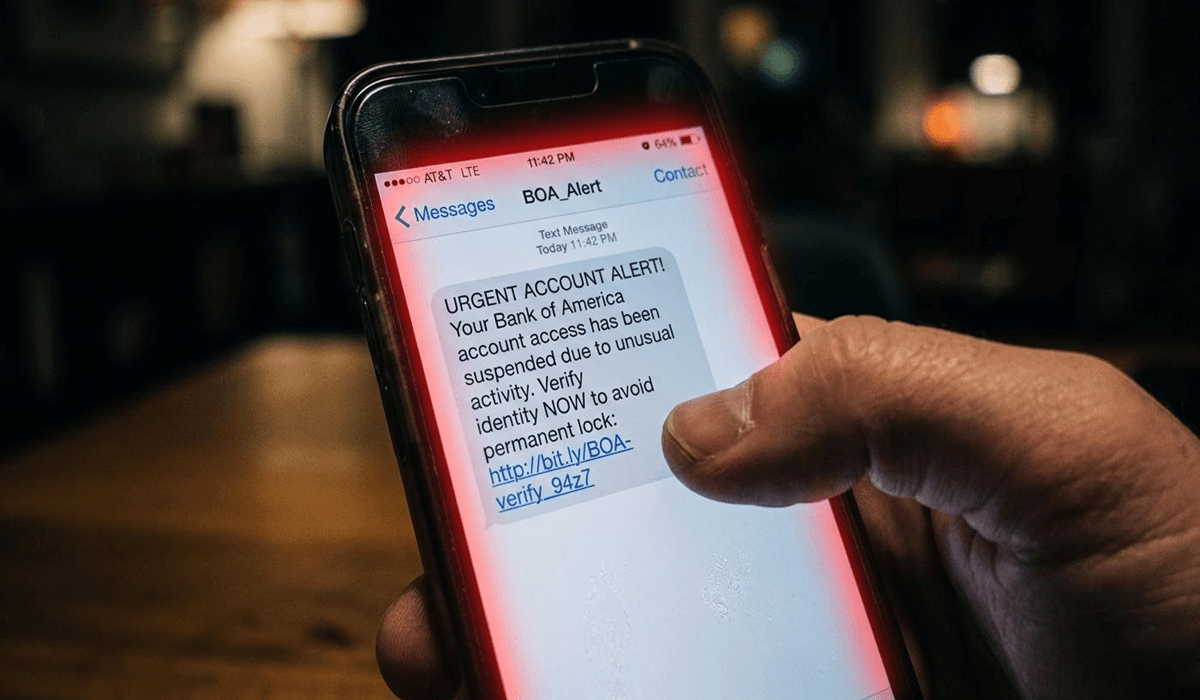
Attackers use bulk SMS platforms – many of them the same tools legitimate businesses use – to blast millions of messages with spoofed sender IDs. The messages impersonate banks, parcel delivery companies, government agencies, and increasingly, internal corporate departments like HR or IT helpdesk. The fake landing pages they link to are built for mobile screens, load in under two seconds, and are often hosted on freshly registered domains that haven’t yet been flagged by threat intelligence feeds.
Threat actor groups like the “Smishing Triad” – documented in Silent Push’s 2025 threat research – operate at extraordinary scale, running more than 200,000 fraudulent domains simultaneously and cycling through them faster than blocklists can keep up. These aren’t lone hackers; they’re organizations with infrastructure, customer service operations, and documented revenue models.
AI and Multi-Channel Attack Techniques
AI has accelerated the timeline significantly. Microsoft’s 2025 Digital Defense Report noted that large language models have cut the time to create a convincing phishing campaign from around 16 hours to roughly five minutes. That speed advantage compounds: attackers can now run highly personalized, localized campaigns targeting specific employee demographics at a fraction of the previous cost.
Smishing has also become a component of multi-channel attacks. Attackers send a phishing email first, then follow up with an SMS to “confirm” a security alert, lending the whole sequence an air of legitimacy. Or they use a smishing message to deliver a phone number to call – a technique called vishing (voice phishing) – where a human operator closes the social engineering loop.
Specific scenarios targeting businesses include:
- CEO or CFO impersonation requesting wire transfers or gift card purchases
- HR benefit enrollment texts with links to fake portals harvesting employee credentials
- IT helpdesk credential reset requests via SMS, bypassing email-based verification entirely
- Delivery notifications with embedded malware links sent to employees who regularly order supplies
CISA’s guidance on avoiding social engineering and phishing attacks lists the clearest employee-facing warning signs: unexpected urgency, requests to bypass normal procedures, sender IDs that don’t match known contacts, and links that don’t match the alleged sender’s domain. Training employees to pause on any one of these signals can interrupt an attack before a credential is entered.
Why Enterprise Wireless Networks Amplify the Risk
When a smishing attack succeeds on an employee’s mobile device, the damage rarely stays contained to that device. The moment that phone reconnects to the corporate wireless network, a compromised device becomes a potential entry point into the internal environment.
Growing Wireless Vulnerabilities
The wireless attack surface itself is growing faster than almost any other area of cybersecurity. According to the Bastille Networks 2025-2026 Threat Report, which draws on NIST National Vulnerability Database data, researchers published 937 new wireless-related CVEs in 2025 alone – averaging 2.5 new vulnerabilities per day. That’s a 230x increase since 2010, and wireless CVEs are growing more than 20 times faster than CVEs across all other technology categories combined.
The Verizon 2025 Mobile Security Index puts the organizational exposure into stark terms: 85% of organizations reported attacks on mobile devices in 2025, up sharply from the previous year. More critically, 53% reported a mobile or IoT-related security incident that resulted in actual data loss or unplanned downtime.
BYOD and Unmanaged Device Risks
BYOD environments make this substantially worse. Personal phones receiving smishing texts are then brought into the office and connected to corporate Wi-Fi. If the user clicked a link and entered credentials, or if a malicious profile was silently installed, that personal device now bridges the attack directly to the internal network. The IT team often has no visibility into what’s on the device, and no policy to block it.
Unmanaged devices compound the problem. Verizon’s 2025 Mobile Security Index also found that 69% of IT administrators report at least half of the devices on their network are unmanaged – meaning no endpoint detection, no patching schedule, no mobile device management enrollment.
Man-in-the-middle attacks over unsecured or poorly configured Wi-Fi add a secondary threat layer. Once an attacker has positioned themselves between an employee’s device and the network – a realistic scenario at any public or improperly secured corporate wireless access point – they can capture session tokens, intercept SMS verification codes, and monitor communications in real time.
When you look at enterprise breach data across industries, the human element continues to play a role in roughly 60% of all confirmed security breaches. Pretexting, the social engineering technique that smishing relies on, has surged as an incident type and now accounts for more than half of all social engineering cases. Mobile devices have become a primary delivery mechanism for these attacks, not a secondary one.
The SMS Authentication Problem: When Security Becomes a Liability
Here’s the uncomfortable part: many of the businesses most exposed to smishing are the ones that thought they were being proactive by implementing SMS-based two-factor authentication.
Why SMS-Based MFA Is Not Phishing-Resistant
SMS 2FA is not sufficient for high-value accounts. That’s not a hedged position – it’s the explicit finding of CISA’s joint phishing guidance document, co-authored with the NSA, FBI, and MS-ISAC. The guidance explicitly states that SMS-based MFA is not phishing-resistant and should not be used for accounts with privileged access.
The reasons are structural. SIM swapping attacks allow criminals to convince a mobile carrier to transfer control of a phone number to an attacker-controlled SIM. Every SMS sent to that number – including OTP codes – now goes to the attacker. The victim loses their second factor entirely without knowing it.
How Attackers Bypass SMS Authentication
Smishing itself can be used to bypass SMS MFA without a SIM swap. An attacker sends a text impersonating the company’s IT team: “Security alert: we detected unusual login activity on your account. Please reply with the verification code just sent to you.” The victim, already expecting a code from a real login attempt, forwards it. Authentication complete.
According to the Proofpoint 2024 State of the Phish report, only 29% of employees surveyed could correctly identify what smishing is. Reports of smishing attacks increased more than 20% year-over-year. Those two numbers together describe a threat that’s accelerating into a workforce that’s largely unprepared to recognize it.
Regarding SMS-based authentication risks, the practical recommendation from security researchers is straightforward: implement FIDO2-compliant hardware keys or authenticator apps for any account with access to financial systems, internal infrastructure, or sensitive data. Phase out SMS OTPs for those accounts entirely.
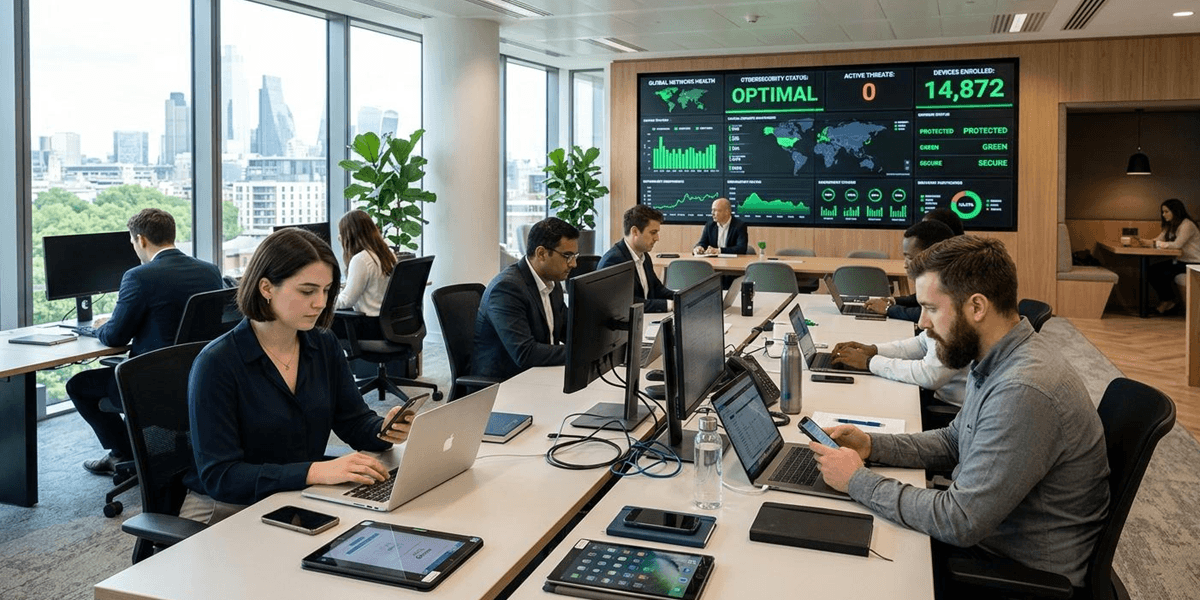
The infrastructure layer matters too. Organizations that have invested in dedicated wireless business solutions have better visibility into which devices are actively connected to their network. That visibility is what makes it possible to detect anomalous behavior – unusual data transfers, unexpected network requests – triggered by a successful smishing attack before it escalates into a full breach.
Building a Smishing Defense Plan for Your Business
The Current State of Business Defenses
Most businesses have no coherent smishing defense. They have email phishing training, maybe a spam filter, and an assumption that employees will figure out the rest. That assumption doesn’t hold up when the attack arrives via a channel the training program never touched.
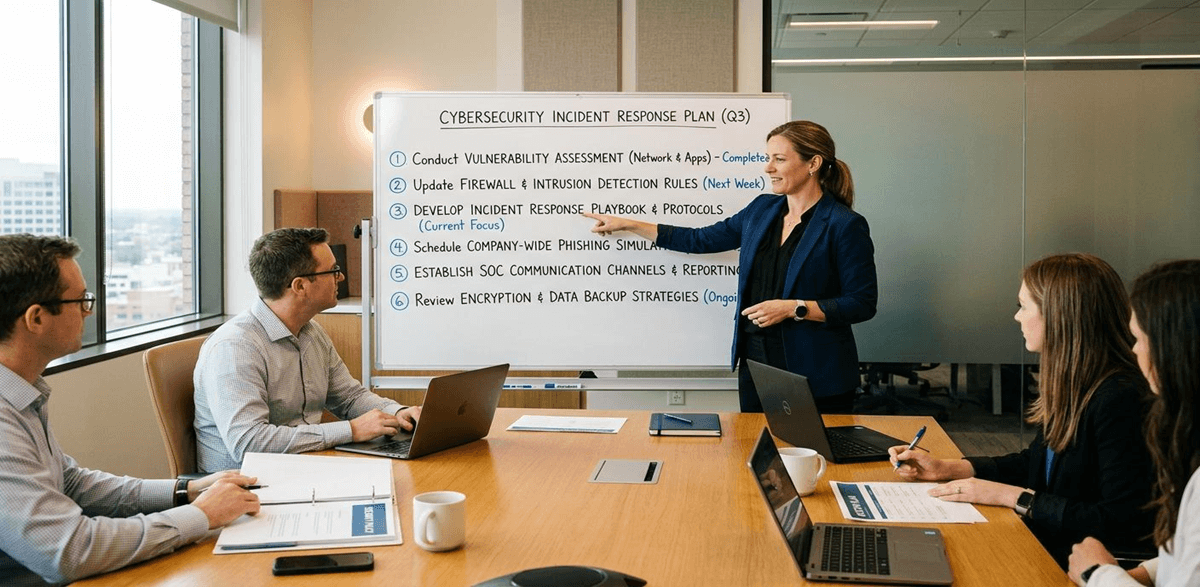
A workable defense plan doesn’t require a complete security overhaul. It requires six specific actions.
Six Actions to Defend Against Smishing
- Run smishing simulations. Only 32% of organizations run them, despite most offering email phishing programs. Smishing simulations don’t have to be elaborate – a quarterly test using a spoofed sender number and a realistic scenario is enough to close most of the recognition gap. Keepnet Labs’ same report found an 87% improvement in smishing recognition rates after targeted training within 90 days.
- Replace SMS OTPs for privileged accounts. CISA’s joint guidance is unambiguous: SMS authentication is not phishing-resistant. For accounts that access financial systems, admin panels, or sensitive customer data, switch to FIDO2 hardware security keys or TOTP authenticator apps. The migration cost is real but modest compared to the cost of a single compromised privileged account.
- Establish a verified sender policy. Employees should know exactly which phone numbers and sender IDs the company uses for official communications – payroll alerts, IT notifications, HR updates. Anything outside that verified list requires a second verification step before action is taken. This policy should be in writing and tested in onboarding.
- Apply DNS filtering on corporate wireless networks. Network-level controls can block connections to known malicious domains before a credential is entered, even if an employee clicks a link. CISA’s phishing guidance specifically recommends DNS filtering as a first-line defense that doesn’t depend on user behavior.
- Enroll all corporate-connected devices in MDM. Mobile Device Management tools give IT teams visibility into what’s on the network, enforce security policies remotely, and allow a compromised device to be wiped before it becomes a lateral movement vector. The 69% of IT admins reporting that half their network devices are unmanaged – per Verizon’s 2025 MSI – are running a network they can’t actually see.
- Build a smishing-specific incident response protocol. Employees need to know exactly what to do when they receive a suspicious text or realize they have clicked a malicious link. Who should they report it to? How quickly should they act? What happens after the report is made? Organizations with clearly defined reporting procedures consistently contain incidents faster than those relying on ad hoc communication. A simple and well-known reporting channel, such as a dedicated Slack channel, a short-code SMS line, or an email alias, removes the ambiguity that often causes employees to hesitate or stay quiet after a potential compromise.
What the Threat Actually Requires
Smishing is not a variation of email phishing with a different delivery method. It’s a structurally different attack that operates on different trust signals, different infrastructure, and different user psychology. The click rates, the financial losses, the wireless CVE explosion, and the MFA bypass techniques are all pointing in the same direction: mobile is now the primary attack surface for social engineering, and most businesses haven’t updated their defenses to reflect that.
The companies most exposed right now are those treating mobile security as an afterthought. They’re running annual email phishing simulations, patting themselves on the back for the SSL certificate on their login page, and leaving SMS completely unguarded.
The path forward isn’t complicated, but it does require making smishing a deliberate part of security planning rather than hoping employees work it out on their own. Audit your current SMS security posture. Check whether your wireless infrastructure gives you visibility into connected devices and anomalous behavior. Schedule your first smishing simulation this quarter, before an attacker runs one for you.

Priya Mervana
 Verified Web Security Experts
Verified Web Security Experts
Priya Mervana is working at SSLInsights.com as a web security expert with over 10 years of experience writing about encryption, SSL certificates, and online privacy. She aims to make complex security topics easily understandable for everyday internet users.