Phishing Statistics 2026: Key Data, Trends, and Emerging Threats
Over 3.8 million phishing attacks were recorded globally in 2025 - and the average breach triggered by a phishing email now costs organizations $4.88 million. For security teams, CISOs, IT administrators, and business leaders, these numbers are no longer background noise: phishing is the most reported cybercrime in the United States and the primary delivery mechanism for ransomware, credential theft, and business email compromise. This article compiles 50+ verified phishing statistics from authoritative sources including APWG, IBM, the FBI IC3, Verizon DBIR, KnowBe4, and Proofpoint, organized into a clear taxonomy to help organizations understand scale, cost, targets, and defenses in 2026.
Key Phishing Statistics for 2026
The following figures represent the most important data points across the full phishing landscape:
- 3.8 million phishing attacks were recorded globally in 2025, according to APWG's full-year 2025 Phishing Activity Trends Report (January 2026).
- $4.88 million is the average cost of a phishing-related data breach in 2024, per IBM's Cost of a Data Breach Report 2024 (2024).
- 82.6% of phishing emails analyzed between September 2024 and February 2025 contained AI-generated content, per KnowBe4's 2025 Phishing Threat Trends Report (March 2025).
- $2.8 billion in BEC losses were reported in the U.S. in 2024, according to the FBI Internet Crime Complaint Center IC3 Annual Report (2025).
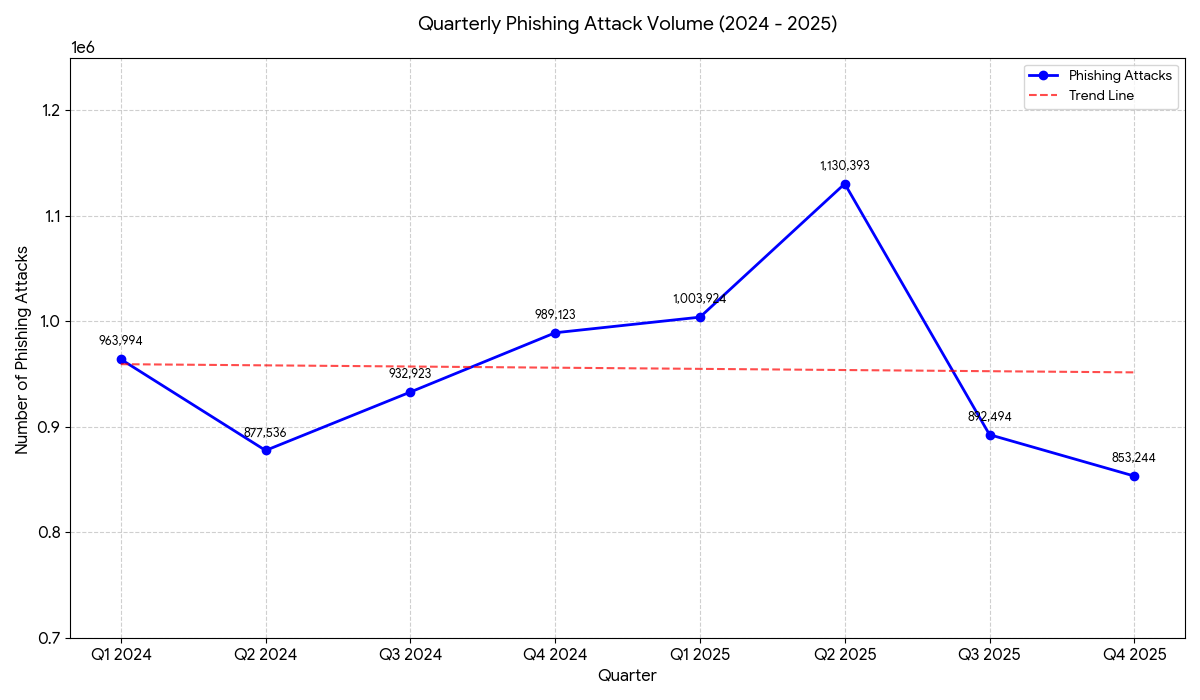
- 1,130,393 phishing attacks were recorded in Q2 2025 alone - the highest quarterly total since Q2 2023 - per APWG Q2 2025 Phishing Activity Trends Report (September 2025).
- 90% of top-clicked phishing attempts in Q4 2025 simulation tests involved domain spoofing, per KnowBe4's Q4 2025 Phishing Simulation Roundup (January 2026).
- 16% of all data breaches analyzed in 2024–2025 used phishing as the initial access vector, according to Verizon's 2025 Data Breach Investigations Report (2025).
Global Phishing Volume Statistics
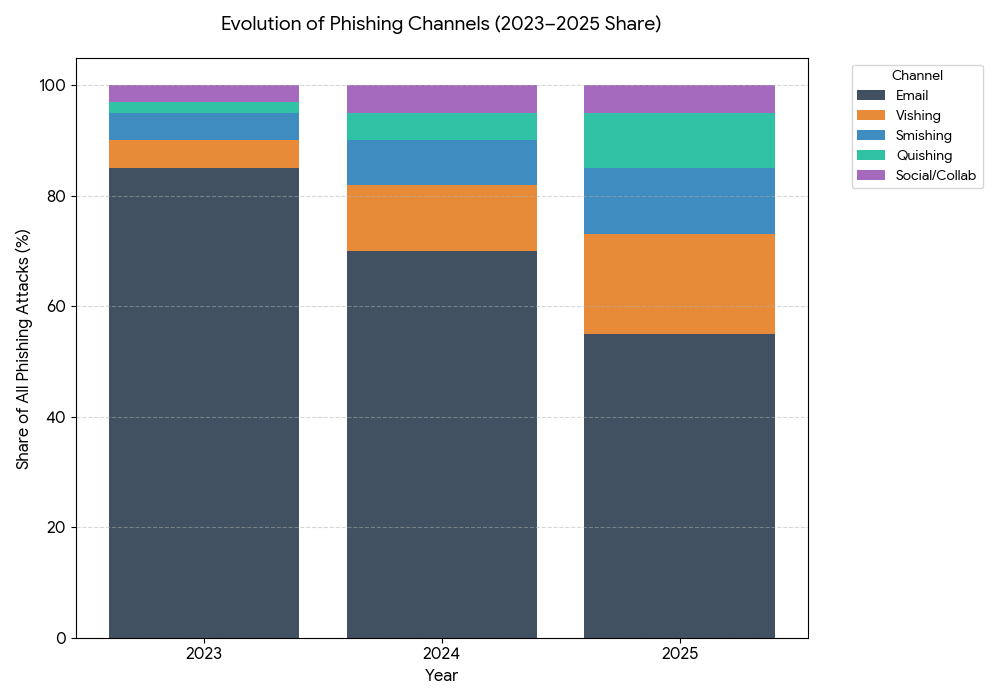
Phishing activity in 2025 stayed at historically elevated levels - the second-highest annual count on record. After peaking at 4.7 million attacks in 2022 and declining slightly in 2024, attack volume climbed again in 2025, driven by AI-assisted campaign generation and the proliferation of Phishing-as-a-Service (PhaaS) kits.
- APWG recorded 3.8 million phishing attacks in 2025, slightly up from 3.76 million in 2024, according to the APWG Q4 2025 Phishing Activity Trends Report (January 2026).
- In Q2 2025, APWG observed 1,130,393 phishing attacks, up 13% from Q1 2025's 1,003,924 - the largest quarterly total since Q2 2023, per the APWG Q2 2025 Phishing Activity Trends Report (September 2025).
- Q3 2025 saw 892,494 attacks - a quarterly decrease, but SMS-based fraud increased by nearly 35% in the same period, per the APWG Q3 2025 Phishing Activity Trends Report (December 2025).
- Q4 2025 recorded 853,244 phishing attacks, a 4% decrease from Q3, though wire transfer BEC attacks rose 136% quarter-over-quarter, per the APWG Q4 2025 Phishing Activity Trends Report (January 2026).
- Phishing attacks increased 13% year over year in 2024 and remained the most common initial attack vector, according to Bright Defense's 2026 Phishing Statistics roundup citing FBI IC3 data (February 2026).
- Phishing was the most-reported cybercrime in 2024, with 193,407 complaints representing 22.5% of all internet crimes and $70 million in direct losses, per the FBI IC3 2024 Internet Crime Report (2025).
- During 2025, threat volume on social media platforms increased across all major platforms, with growth ranging from 51% to 843% quarter-to-quarter, per ZeroFox data cited in APWG Q4 2025 Phishing Activity Trends Report (January 2026).
- An estimated 3.4 billion phishing emails are sent daily worldwide, making it the most pervasive form of cybercrime, per AAG IT Support phishing statistics citing Statista data (updated October 2025).
- The human element was a factor in approximately 60% of all confirmed breaches in 2024, according to Verizon's 2025 Data Breach Investigations Report (2025).
Phishing Costs and Financial Impact Statistics
The financial consequences of phishing extend well beyond the initial breach - they include forensic investigation, business disruption, notification costs, regulatory fines, and reputational damage. The numbers in 2025 reflect a threat with direct P&L implications.
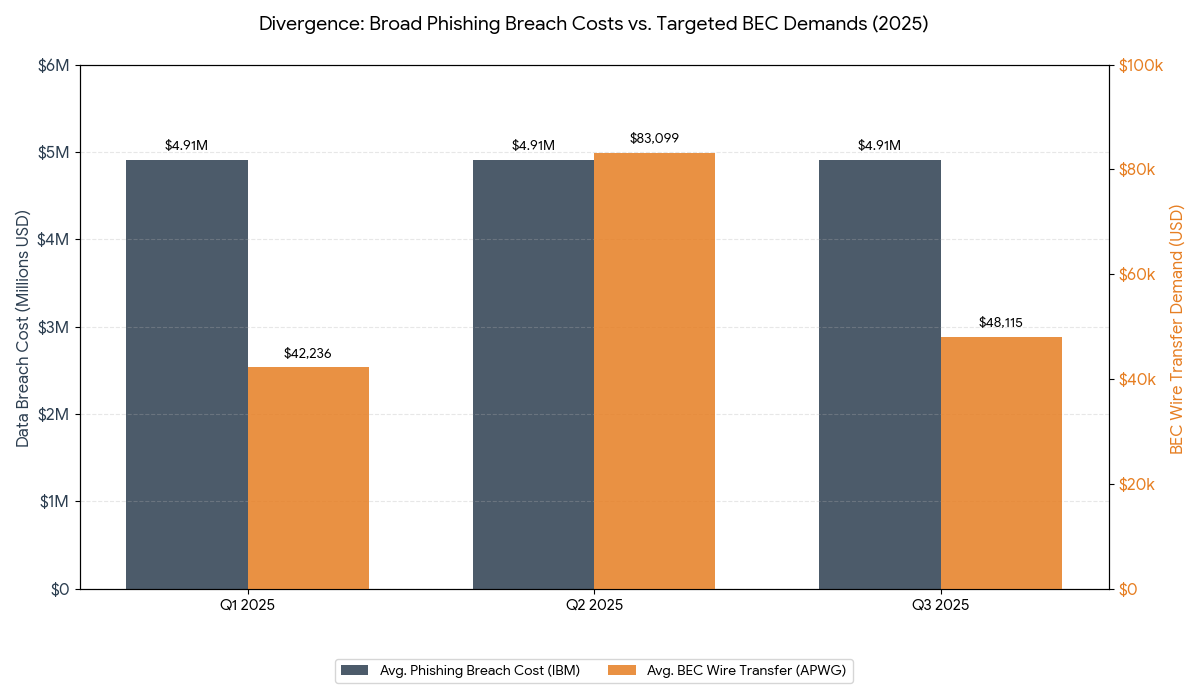
- The average cost of a phishing-related data breach reached $4.88 million in 2024, according to IBM's Cost of a Data Breach Report 2024. This figure dropped to $4.44 million globally in 2025 as AI-assisted detection shortened containment times, per IBM's Cost of a Data Breach Report 2025 (2025).
- Breaches that began with a phishing attack averaged $4.91 million per incident according to analysis of IBM's 2025 Cost of a Data Breach Report summarized by Deepstrike Social Engineering Statistics 2025 (September 2025).
- Business Email Compromise (BEC) caused $2.8 billion in U.S. losses in 2024, per the FBI IC3 2024 Annual Crime Report cited in APWG Q3 2025 (December 2025).
- Global financial losses from phishing hit $17.4 billion in 2024, a 45% year-over-year increase, per NordVPN research cited in Kelser Corporation's 2025 phishing analysis (2025).
- The average wire transfer requested in BEC attacks rose to $83,099 in Q2 2025 - a 97% increase from Q1 2025's average of $42,236 - then fell to $48,115 in Q3 2025, according to APWG Q2 2025 and APWG Q3 2025 Phishing Activity Trends Reports.
- Wire transfer BEC attacks in Q4 2025 increased 136% compared to Q3 2025, driven largely by threat group "Scripted Sparrow," which sends an estimated 6 million targeted emails monthly, per the APWG Q4 2025 Phishing Activity Trends Report (January 2026).
- In 2024, the FBI IC3 received over 21,442 BEC complaints, with total reported losses of $2.77 billion, per data cited in Verizon's 2025 DBIR analysis by Keepnet (May 2025).
- Organizations extensively using AI and automation in breach prevention saved an average of $2.2 million per breach compared to those without such tools, according to IBM's 2025 Cost of a Data Breach Report.
What Industries Are Most Targeted by Phishing?
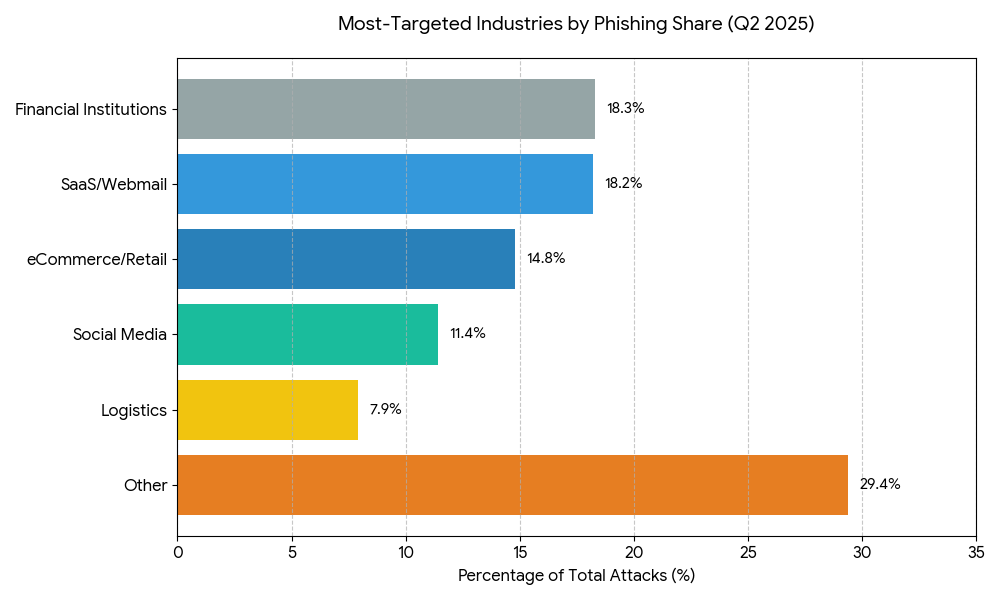
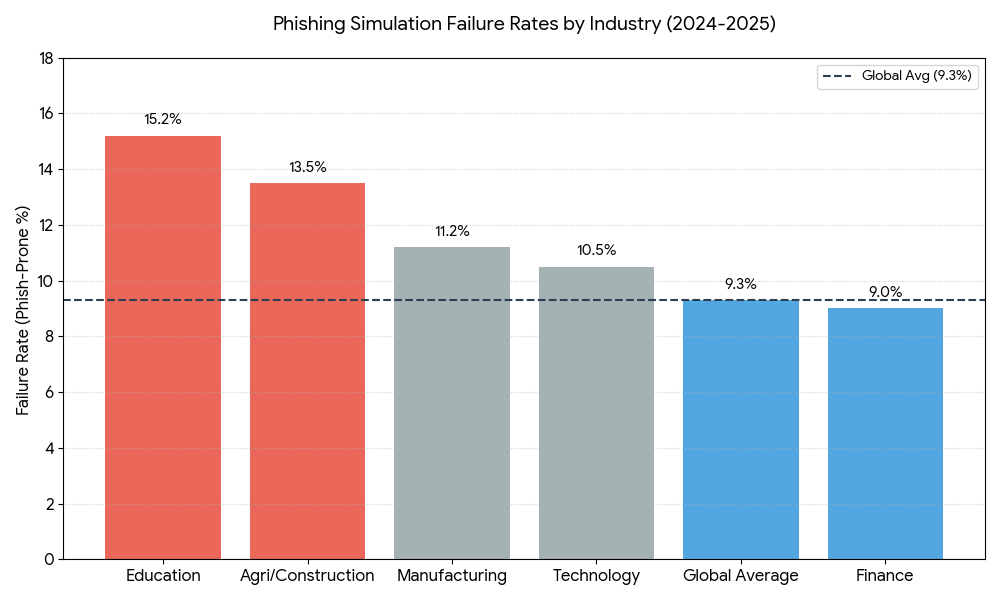
No sector is immune, but phishing campaigns concentrate in industries with high transaction volumes, valuable credentials, and large user bases. The sector rankings shifted throughout 2025 as attackers adapted tactics.
- In Q2 2025, the most-targeted sectors were Financial Institutions (18.3%), SaaS/Webmail (18.2%), and eCommerce/Retail (14.8%), per the APWG Q2 2025 Phishing Activity Trends Report (September 2025).
- In Q3 2025, SaaS/Webmail and Social Media became the most frequently targeted sectors, per the APWG Q3 2025 Phishing Activity Trends Report (December 2025).
- Financial services and online payments together accounted for 30.9% of all phishing attacks in Q1 2025, per the APWG Q1 2025 Phishing Activity Trends Report (May 2025).
- Manufacturing was the sector most often attacked with malicious QR codes in Q3 2025, with 74,054 detections, per the APWG Q3 2025 Phishing Activity Trends Report (December 2025).
- Social engineering accounts for 16% of Educational Services breaches, and 77% of those social engineering breaches were caused by phishing, per Verizon's 2025 DBIR (2025).
- Phishing was the fifth most common action in manufacturing data breaches, accounting for nearly one-fifth (19%) of incidents, per Verizon's 2025 DBIR cited by Secureframe (August 2025).
- Finance, Retail, and Federal sectors were the three most consistently targeted by social media-based phishing threats throughout 2025, per ZeroFox data in APWG Q4 2025 (January 2026).
- The financial services sector showed the highest phishing simulation reporting rate at 32.35%, while education had the lowest at 7.71%, per Proofpoint's 2025 phishing test data (April 2025).
Brand Impersonation Statistics
Attackers consistently exploit the trust users have in well-known brands. The most impersonated brands change quarter to quarter, but technology companies and delivery services dominate.
- Microsoft was the most impersonated brand in 2024, appearing in over 51.7% of all phishing scams worldwide, per data reported by Hunto AI's 2026 Phishing Attack Statistics (January 2026).
- In Q3 2025, Walmart became the most-impersonated brand, supplanting delivery company DHL, which had topped Q2 rankings, per the APWG Q3 2025 Phishing Activity Trends Report (December 2025).
- Mimecast counted 1,642 brands targeted by criminals using QR codes in Q2 2025, with DHL attacked most often (3,543 unique QR codes), followed by Microsoft, per the APWG Q2 2025 Phishing Activity Trends Report (September 2025).
|
Brand |
Phishing Share (Avg) |
QR Phishing Target Rank |
Primary Industry |
|
Microsoft |
22% - 51.7% |
High (#2) |
Technology / SaaS |
|
|
9% - 13% |
Moderate |
Technology / SaaS |
|
Amazon |
3% - 9% |
Moderate |
eCommerce / Retail |
|
Apple |
6% - 12% |
Low |
Technology / Hardware |
|
Facebook (Meta) |
3% - 14.5% |
Moderate |
Social Media |
|
DHL |
1% - 2% |
Very High (#1) |
Logistics / Shipping |
|
Walmart |
(Leading Q3 '25) |
Moderate |
eCommerce / Retail |
|
PayPal |
2% - 3% |
Moderate |
Financial Services |
- The top 10 most-reported real-world phishing attacks in Q4 2025 simulation tests frequently impersonated Microsoft, ShareFile, Google, Zoom, Adobe, Coinbase, and DHL, per KnowBe4's Q4 2025 Phishing Simulation Roundup (January 2026).
- 74% of BEC attacks in Q3 2025 were launched using free webmail domains; Gmail was used in 66% of those accounts, per the APWG Q3 2025 Phishing Activity Trends Report (December 2025).
- Deceptive links were the most common phishing method, making up 36% of phishing threats identified in Cloudflare's analysis of 13 billion emails, per Keepnet's 2026 Phishing Statistics (January 2026).
AI-Powered Phishing Statistics
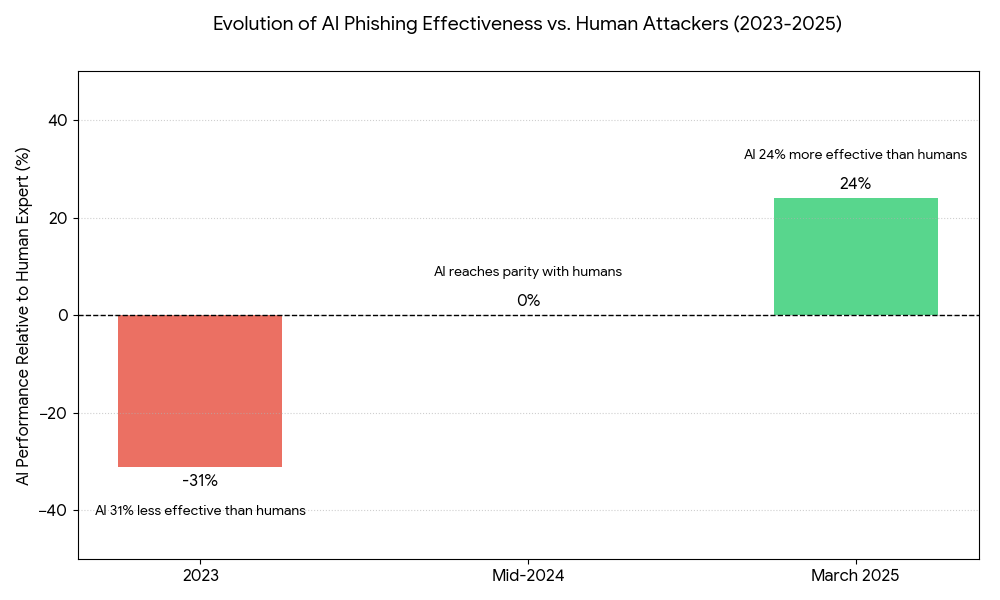
The weaponization of generative AI has fundamentally changed phishing's threat profile. AI enables attackers to produce high-volume, high-quality, personalized campaigns at a fraction of the previous cost and effort.
- 82.6% of phishing emails analyzed between September 2024 and February 2025 contained AI-generated content, per KnowBe4's 2025 Phishing Threat Trends Report (March 2025). This signals that AI is no longer an edge tactic - it is the baseline for modern phishing campaigns.
- AI-driven fraud attacks spiked by more than 1,200% in December 2025, according to a report by Pindrop Security cited by KnowBe4 (February 2026).
- Phishing emails containing ransomware jumped by 22.6% between September 2024 and February 2025, per KnowBe4's 2025 Phishing Threat Trends Report (March 2025).
- Over 75% of phishing campaigns now use morphing or polymorphic techniques to bypass traditional email filters, per KnowBe4's 2025 Phishing Threat Trends Report as summarized by OCD Tech (March 2025).
- An AI spear phishing agent was 24% more effective at tricking users than elite human red team operators by March 2025, reversing a 2023 result where AI was 31% less effective than humans, per Hoxhunt research cited in Deepstrike's 2025 Phishing Statistics (April 2025).
- AI-generated phishing emails achieve a click-through rate of 54%, matching performance of emails crafted by human experts and outperforming control groups by 350%, per a 2024 study cited by NordVPN's 2026 Phishing Statistics (January 2026).
- 86% of organizations have encountered at least one AI-related phishing or social engineering incident, per Bright Defense's Phishing Statistics 2026 (February 2026).
- A single threat intelligence database misses 15–30% of threats, highlighting why AI-assisted multi-source detection is now necessary, per analysis from CaptainDNS phishing trends analysis (February 2026).
QR Code Phishing (Quishing) Statistics
QR code phishing bypasses traditional email security filters because the malicious link is encoded in an image, not text. This technique surged throughout 2025.
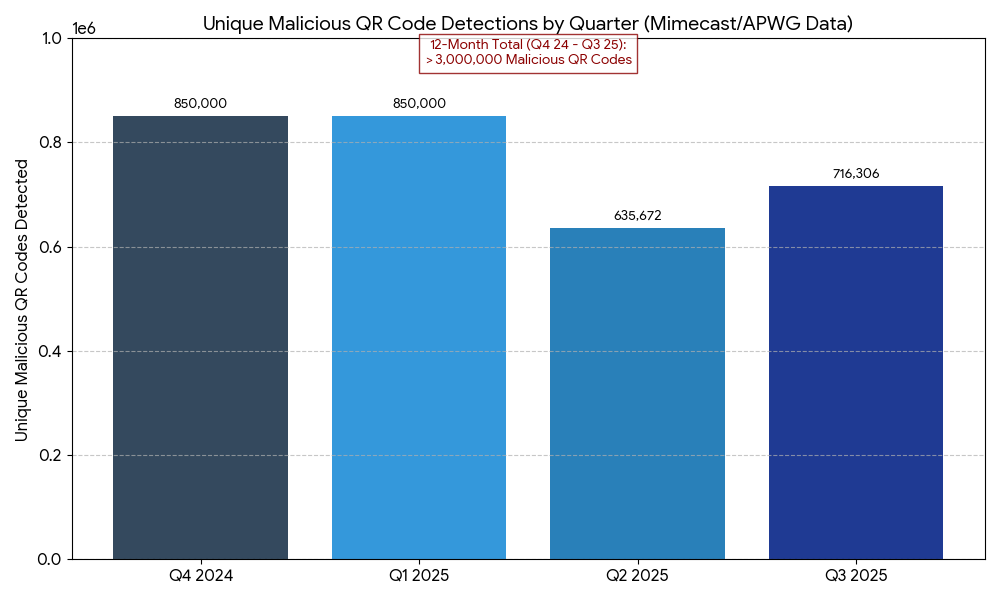
- During Q3 2025, Mimecast detected 716,306 unique malicious QR codes used for phishing - up 13% from 635,672 in Q2, per the APWG Q3 2025 Phishing Activity Trends Report (December 2025).
- Over the 12-month period from Q2 2024 through Q3 2025, Mimecast detected more than 3 million unique malicious QR codes, per the APWG Q3 2025 Phishing Activity Trends Report (December 2025).
- QR code attacks increased 400% between 2023 and 2025, according to Abnormal Security research cited by CaptainDNS (February 2026). The most affected sectors are energy, healthcare, and manufacturing.
- Cofense reported a 331% year-over-year increase in QR code phishing campaigns, per data cited in Deepstrike's 2025 Phishing Statistics (April 2025).
- In Q4 2025, quishing volume dropped quarter-on-quarter, but phishers shifted to new infrastructures and targets to evade detection, per the APWG Q4 2025 Phishing Activity Trends Report (January 2026).
Business Email Compromise (BEC) Statistics
BEC sits at the intersection of phishing and fraud. Unlike broad phishing campaigns, BEC is precision-targeted - impersonating executives, vendors, or partners to authorize fraudulent transfers.
- BEC accounted for the #1 cybercrime by financial loss in the FBI's 2024 reporting, with losses reaching $2.77–$2.8 billion in the U.S. alone, per the FBI IC3 Annual Crime Report 2024 and the APWG Q3 2025 Trends Report (2025).
- BEC accounted for 27% of all incident response engagements, second only to ransomware, per analysis of IBM and Verizon data cited in Deepstrike's 2025 Phishing Statistics (April 2025).
- The total number of wire transfer BEC attacks in Q1 2025 increased 33% compared to Q4 2024, while the average amount requested dropped 67% from the prior quarter's average of $128,980 to $42,236, per the APWG Q1 2025 Phishing Activity Trends Report (May 2025).
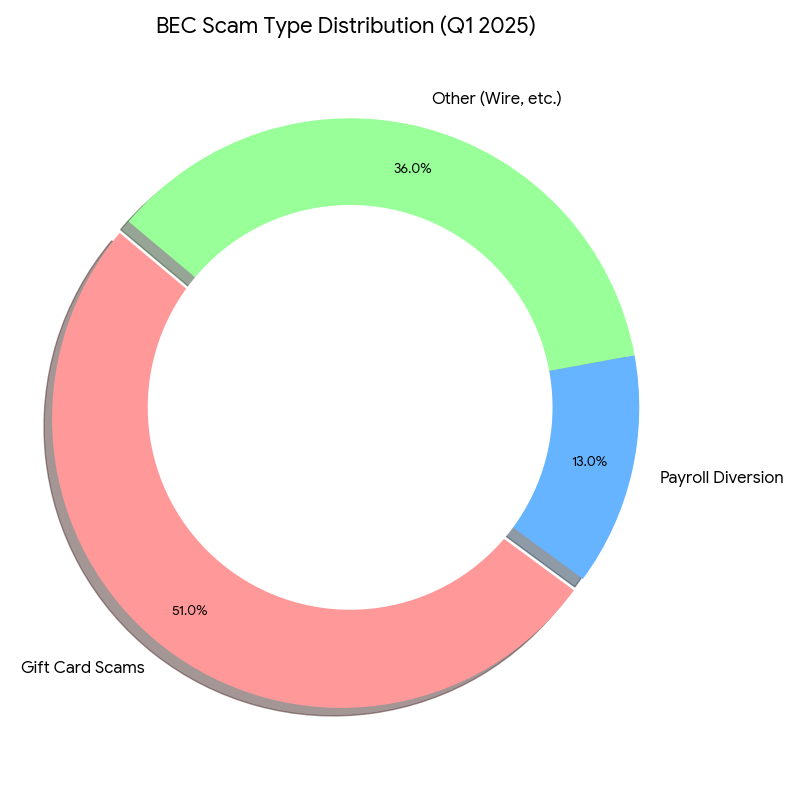
- Gift card scams were the most popular BEC scam type in Q1 2025, making up 51% of the total, with payroll diversion scams representing 13%, per the APWG Q1 2025 Phishing Activity Trends Report (May 2025).
- Pretexting incidents have nearly doubled, now accounting for over 50% of all social engineering incidents, per Verizon's 2025 DBIR analysis (May 2025). Pretexting is the social engineering layer that powers BEC.
- The FBI's 2025 IC3 report logged a 37% rise in AI-assisted BEC, including hundreds of deepfake-based scams involving cloned executive voices, per Deepstrike's AI Cyber Attack Statistics 2025 (October 2025).
- 74% of BEC attacks in Q3 2025 were launched from free webmail accounts, with Gmail used in 66% of those accounts, per the APWG Q3 2025 Phishing Activity Trends Report (December 2025).
Phishing Attack Types: Smishing, Vishing, and Spear Phishing Statistics
Phishing has expanded well beyond the email inbox. Attackers now operate across SMS, voice calls, and social platforms, exploiting the lower defenses of non-email channels.
- SMS-based fraud (smishing) increased by nearly 35% in Q3 2025 compared to Q2, per the APWG Q3 2025 Phishing Activity Trends Report (December 2025).
- 75% of organizations reported at least one smishing attempt in the past year, per a 2025 Proofpoint survey cited by Sycom Academy (2025).
- Vishing (voice phishing) was identified as the most common phishing type in Q1 2025, accounting for over 60% of phishing-related incident response engagements, per Cisco Talos data cited by Deepstrike's 2025 Phishing Statistics (April 2025).
- Vishing attacks on professionals rose by 28% in 2024, per NordVPN's 2026 Phishing Statistics citing Proofpoint research (January 2026).
- 65% of successful phishing attacks in 2024 are attributed to spear phishing, targeting specific individuals with personalized content, per data cited by NordVPN's 2026 Phishing Statistics (January 2026).
- Internal topics appeared in 100% of the top 10 most-clicked phishing subject lines in Q4 2025 simulation tests, and HR-related topics were referenced in 46%, per KnowBe4's Q4 2025 Phishing Simulation Roundup (January 2026).
- 90% of top-clicked phishing attempts in Q4 2025 involved domain spoofing, according to KnowBe4's Q4 2025 Phishing Simulation Roundup (January 2026).
- Around 40% of phishing campaigns now extend to platforms beyond email, including Slack, Microsoft Teams, and social media, per Deepstrike's 2025 Phishing Statistics (April 2025).
Phishing Awareness and Human Risk Statistics
Training and awareness programs produce measurable results - but the data reveals a persistent gap between knowing about phishing and resisting it in real situations.
- 68% of employees admit to engaging in behaviors they know put their organization at risk, such as reusing passwords or ignoring security guidance, per Proofpoint's 2024 State of the Phish Report cited by Tropico Security (December 2025).
- The average reporting rate for users flagging simulated phishing messages across all organizations is 18.65%, with financial services highest at 32.35% and education lowest at 7.71%, per Proofpoint's 2025 phishing simulation data (April 2025).
- Annual phishing awareness training alone decreases click rates by only 1.7%, per a 2025 IEEE Security and Privacy study (Ho et al., 2025) - suggesting that one-time annual training has negligible impact without ongoing reinforcement.
- Consistent phishing awareness programs lowered organizations' Phish-Prone Percentage (PPP) by as much as 86% over one year, per KnowBe4's 2025 Phishing Report cited by Sycom Academy (2025). The key variable is frequency, not format.
- The median time for a user to fall for a phishing email is less than 60 seconds, per Deepstrike's Social Engineering Statistics 2025 (September 2025) - faster than most security monitoring systems can flag an inbound threat.
- New hires are 44% more likely to fall victim to phishing and social engineering attacks during their first 90 days, per Keepnet research cited in their 2026 Phishing Statistics (January 2026).
- In Verizon's simulated phishing exercises, approximately 20% of individuals recognized and reported phishing, while 11% of those who clicked still reported the incident afterward – signaling a growing but incomplete reporting culture. Employees should also flag the email as phishing in their inbox to train AI defenses. For an easy way to block emails, consider using a tool like Block Sender.
Phishing Defense and Security Technology Statistics
Technical controls including email authentication, AI-powered detection, and multi-factor authentication are producing results - but adoption gaps remain significant.
- 41% of banking institutions currently lack DMARC protection, creating a structural vulnerability to email spoofing, per PowerDMARC's 2026 phishing and DMARC statistics (February 2026).
- Zero-trust architecture reduced breach costs by $1.76 million per incident ($4.15M vs. $5.10M), per UpGuard research cited in Bright Defense's data breach statistics (January 2026).
- Phishing-resistant MFA adoption stands at only 5–15% across most organizations, despite regulatory guidance mandating FIDO2-compliant solutions, per Tropico Security's 2026 phishing analysis (December 2025).
- 96% of phishing attacks in 2024 exploited trusted domains including SharePoint and Zoom Docs, according to Darktrace research cited by NordVPN (January 2026). This makes domain-allowlisting ineffective as a primary defense.
|
Defense Layer |
Current Adoption Rate |
Cost Impact (Per Incident) |
Gap to Full Deployment |
|
DMARC Enforcement |
59% (Banking) |
Significant reduction in spoofing risk |
41% of banks still lack protection. |
|
Phishing-Resistant MFA |
14% (Global) |
Prevents AiTM & session hijacking |
86% still rely on legacy MFA (SMS/Push). |
|
Zero-Trust Architecture |
Varies by maturity |
$1.76M savings per breach |
38% higher costs for non-adopters. |
- Organizations that adopt AI and automation in security save an average of $2.2 million per breach compared to those without such tools, per IBM's Cost of a Data Breach Report 2025 (2025).
- The average breach detection and containment window dropped to 241 days in 2025, the lowest in nearly a decade, driven by AI-powered detection tools, per IBM's Cost of a Data Breach Report 2025 cited by Bright Defense (January 2026).