Bare metal hosting is the strongest infrastructure choice for PCI DSS compliance because it provides single-tenant physical servers, eliminating the shared-resource risks that complicate cardholder data environment scoping in virtualized setups. For e-commerce businesses, payment processors, and fintech platforms required to meet PCI DSS v4.0 requirements - which became fully mandatory in March 2025 - dedicated hardware gives auditors a clean, documentable environment with no noisy-neighbor exposure. The right provider pairs compliant physical infrastructure with supporting controls: network segmentation, intrusion detection, WAF services, and audit-ready documentation.
What Is Bare Metal Hosting and Why Does PCI DSS Favor It?
Bare metal hosting is dedicated physical server infrastructure where a single tenant owns all compute resources - CPU, RAM, storage - with no hypervisor layer shared with other customers. Unlike cloud VMs, there is no virtualization overhead and no risk of another tenant's workload touching your hardware.
PCI DSS compliance requires organizations to define and isolate their Cardholder Data Environment (CDE) - every system that stores, processes, or transmits payment card data. Shared virtualized servers create overlapping scopes that are difficult to audit and harder to control. Bare metal removes that ambiguity.
Requirement 1 mandates network security controls, while Requirement 2 covers system configuration security. Both are simpler to satisfy when you control the full hardware stack. Bare metal also supports Layer 2 network isolation, dedicated firewall deployment, and hardware-level encryption that PCI auditors look for during assessments.
What Did PCI DSS 4.0 Change for Hosting Environments?
PCI DSS v4.0 replaced version 3.2.1 in March 2024, and all future-dated requirements became mandatory by March 31, 2025. For organizations selecting hosting infrastructure today, these changes directly affect what a compliant server environment must support.
Key changes that impact hosting infrastructure choices include:
- Multi-factor authentication (MFA) is now required for all access into the CDE - not just administrative access - meaning your provider's management layer must support MFA integration.
- Disk and partition-level encryption alone no longer satisfies data protection requirements. Field- or column-level encryption with key management is now expected for stored cardholder data.
- Web Application Firewalls (WAF) are mandatory for internet-facing payment pages under Requirement 6.4.2, so your provider should offer WAF services or support third-party integration.
- Authenticated vulnerability scans are required quarterly, replacing unauthenticated scans - providers with managed security services are better positioned to support this.
- Third-party service providers must share documented proof of their own PCI compliance annually, per Requirement 12.8.4.
According to the PCI SSC summary of changes from v3.2.1 to v4.0, the updated standard introduced nearly 200 unique updates to address emerging cloud, API, and payment page threats. Organizations using bare metal benefit because they control the environment these new controls run within.
How Do Top Bare Metal Providers Compare for PCI Compliance?
The table below compares leading providers across the features that matter most for PCI-compliant deployments.
| Provider | PCI-Ready | Managed Security | Isolation | Compliance Certs | Price/mo |
| Atlantic.Net | Yes - audit-ready | Firewall, IDS, MFA, WAF | Layer 2 + single-tenant | PCI DSS, HIPAA, SOC 2/3, GDPR | ~$279 |
| Liquid Web | Yes | Managed + proactive monitoring | Dedicated physical server | PCI DSS, HIPAA | ~$354 |
| PhoenixNAP | Yes | DDoS, firewall, VPN | SOC-audited Bare Metal Cloud | PCI DSS, SOC 1/2, ISO 27001 | Custom |
| IBM Cloud | Yes - Level 1 SP | HSM, logging, vuln scan | Dedicated + hybrid options | PCI DSS (L1), HIPAA, FedRAMP | Enterprise |
| OVHcloud | Yes (select DCs) | Security add-ons | Bare Metal Cloud | PCI DSS, ISO 27001, SOC 2 | Custom |
Atlantic.Net and Liquid Web lead for organizations needing managed compliance support alongside hardware. IBM Cloud suits enterprises with Level 1 PCI Service Provider requirements in their vendor chain.
Why Is Atlantic.Net the Top Choice for PCI-Compliant Bare Metal?
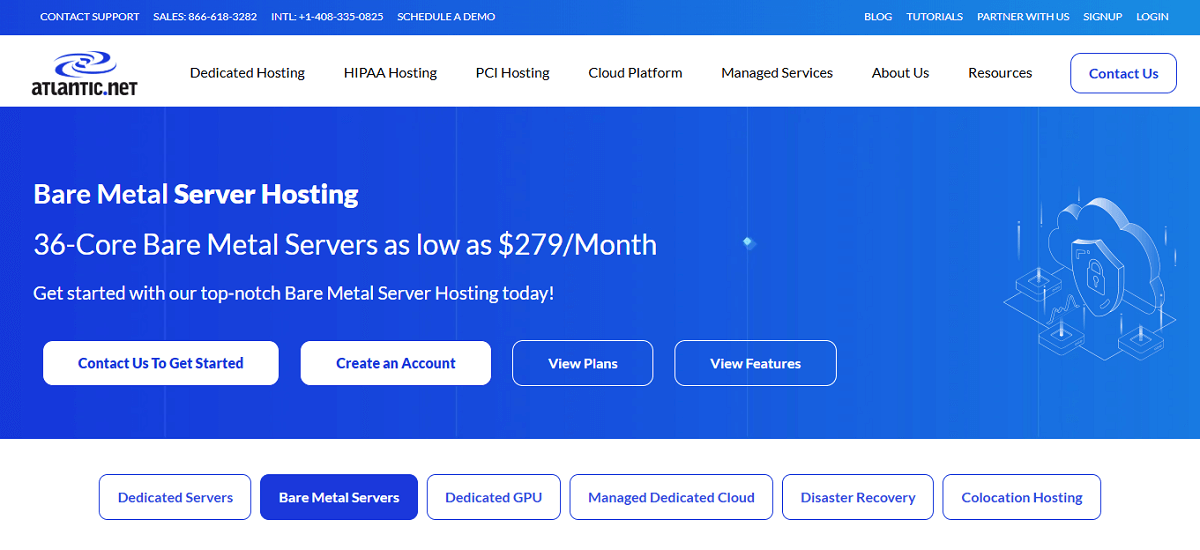
Atlantic.Net leads for PCI-focused bare metal because it combines audit-ready infrastructure with hands-on managed security - an unusual pairing at this price point. Most bare metal providers deliver hardware and leave compliance implementation entirely to the customer.
Atlantic.Net holds certifications for PCI DSS, HIPAA, SOC 2 Type II, SOC 3, and GDPR-ready operations. Their bare metal servers use Layer 2 network virtualization to isolate tenant traffic at the hardware level - a direct answer to PCI DSS Requirement 1 network segmentation controls.
Available hardware includes Intel Xeon and AMD EPYC processors with configurations up to 64 cores, 1 TB+ RAM, and NVMe storage. Bare metal plans start at around $279/month for a 36-core server, with optional managed add-ons including:
- Managed firewall service with custom rule sets
- Intrusion Detection Service (IDS) for real-time threat visibility
- Multi-Factor Authentication integration for CDE access control
- Trend Micro Deep Security Suite for endpoint protection
- DDoS mitigation via Network Edge Protection
- Veeam-powered backup and replication supporting data recovery obligations under PCI Requirement 9
Data centers span New York, Dallas, Ashburn, San Francisco, Orlando, and London, with additional international locations. The 100% network and infrastructure uptime SLA is backed contractually, which matters during audits where system availability logs are reviewed.
What PCI DSS Requirements Does Bare Metal Hosting Address Directly?
Bare metal hosting helps satisfy multiple requirements within the PCI DSS framework. Understanding which ones depend on hosting infrastructure helps you evaluate providers more precisely.
| PCI DSS Requirement | What It Demands | How Bare Metal Helps |
| Req. 1 - Network Controls | Firewall/controls isolating CDE | Single-tenant hardware with Layer 2 isolation removes shared-tenant exposure |
| Req. 2 - Secure Config | No vendor defaults; hardened configs | Full OS control; configure from scratch without shared constraints |
| Req. 3 - Data Protection | Encrypt stored card data; field-level required | Direct control over storage encryption at hardware and OS level |
| Req. 6 - Secure Systems | WAF for payment pages; patch management | WAF available as add-on; customer or provider manages patching |
| Req. 8 - Identity & Access | MFA for all CDE access; 12-char passwords | Managed MFA add-ons available; no shared-tenant access risk |
| Req. 10 - Logging | Log all system activity; 12-month retention | Dedicated log storage; no cross-tenant log contamination |
| Req. 11 - Testing | Quarterly authenticated scans; annual pen test | Managed providers handle scan schedules; dedicated hardware simplifies scope |
Application-level controls, user access policies, and security awareness training remain your responsibility regardless of infrastructure. A compliant bare metal provider handles the physical and network layers that underpin the entire compliance posture.
What Should You Look for in a PCI-Compliant Bare Metal Provider?
Choosing the right provider goes beyond checking a PCI-ready checkbox. These are the specific features that separate a genuinely useful compliance partner from one that sells hardware alone.
- Attestation of Compliance (AOC) on request: The provider should share their own PCI DSS AOC when asked. Under Requirement 12.8.4, you must obtain proof of service provider compliance annually. If a provider cannot produce an AOC, they cannot reduce your compliance scope.
- Documented shared responsibility model: PCI compliance always splits between hosting provider and customer. The provider should supply a written document specifying which requirements they own versus which fall to you. Without this, your QSA will flag the gap during assessment.
- Network segmentation at hardware level: VLAN segmentation is software-defined and can be misconfigured. For high-security CDE deployments, Layer 2 physical isolation at the switch or NIC level provides stronger audit evidence than software-only segmentation.
- Managed security services: WAF, IDS, MFA, and vulnerability scanning should be available as add-ons or inclusions. Sourcing all these controls separately increases operational complexity and makes audit documentation harder to centralize.
- Data center SOC 2 Type II certification: The data centers hosting your servers should hold SOC 2 Type II at minimum, confirming physical security and confidentiality controls have been independently verified - directly supporting PCI Requirement 9.
- Geographic options matching data residency needs: EU customer card data may be subject to GDPR data residency restrictions. Choose a provider with locations that match both your latency requirements and jurisdictional rules.
Is Bare Metal Hosting More Expensive Than Cloud for PCI Compliance?
Bare metal hosting costs more per month than a comparable cloud VM, but total PCI compliance costs are often lower - because you spend less building controls the hosting environment already provides.
For sustained workloads running around the clock, bare metal delivers meaningful savings versus equivalent cloud instances. Cost reduction comes from predictable pricing without data egress fees, and from consolidating workloads onto single high-spec hardware rather than managing multiple billable cloud instances.
Consider the compliance-specific cost factors:
| Cost Factor | Cloud VM (Shared) | Bare Metal (Dedicated) |
| CDE scope complexity | High - shared hypervisor complicates CDE definition | Low - single-tenant hardware creates clean scope |
| Network segmentation | Additional VPC/firewall configurations required | Often included or simpler to implement |
| QSA audit time | Longer - auditor evaluates shared infrastructure | Shorter - dedicated environment assesses faster |
| Data egress fees | Common with major cloud providers | Predictable or included in bandwidth allowances |
| Hardware control | None - provider manages hardware choices | Full - select CPU, RAM, storage configuration |
For organizations processing high transaction volumes continuously, dedicated bare metal for PCI workloads frequently makes more financial sense than attempting to isolate a compliant CDE within shared cloud infrastructure.
How Do You Set Up a PCI-Compliant Environment on Bare Metal?
Setting up a PCI DSS-compliant bare metal environment follows a defined sequence. These steps reflect the core technical setup required to pass a QSA assessment on dedicated hardware.
- Define and document your CDE scope: Identify every server, network segment, and system component that stores, processes, or transmits cardholder data. With bare metal, this is clean: your designated server(s) and their network connections form the scope boundary.
- Implement network segmentation: Configure dedicated firewalls and VLANs to isolate your CDE from other systems. Managed firewall services include custom rule sets that prevent out-of-scope systems from reaching payment infrastructure.
- Harden the operating system: Remove unnecessary services, disable default accounts, and apply a documented baseline configuration per Requirement 2. Bare metal ships without a pre-installed hypervisor, giving you full OS control from the first boot.
- Enable field-level encryption for stored card data: PCI DSS 4.0 requires stronger encryption for stored Primary Account Numbers. Implement database-level column encryption or tokenization - disk-level encryption alone no longer qualifies under the updated standard.
- Deploy WAF for payment pages: Requirement 6.4.2 mandates a WAF for internet-facing payment interfaces. Configure it to log and block OWASP Top 10 attacks, and document rule sets in your security policies for auditors.
- Configure MFA for all CDE access: Every user accessing the cardholder data environment needs MFA - not only administrators. Document user access reviews occurring at least every six months per the updated requirements.
- Set up logging and retention: Configure system logging for all in-scope components and retain logs for 12 months with three months immediately available. Bare metal gives direct OS-level log access without virtualization-layer interference.
- Schedule quarterly authenticated vulnerability scans: Work with an Approved Scanning Vendor (ASV) for quarterly external scans and run internal authenticated scans per the updated standard. Providers with managed security services often include scan scheduling.
- Obtain and file your provider's AOC: Request the hosting provider's current PCI DSS Attestation of Compliance. File it in vendor documentation and renew annually under Requirement 12.8.4.
What Are Common Mistakes When Choosing Bare Metal for PCI Compliance?
Most compliance failures during PCI assessments trace back to infrastructure choices that seemed reasonable at provisioning time. These errors appear repeatedly across assessments.
- Assuming "PCI-ready" means "PCI-compliant" - A PCI-ready provider has built infrastructure that can support your compliance effort. Application controls, access policies, and training requirements remain entirely yours.
- Skipping the shared responsibility document - Without a written agreement specifying which requirements your provider owns versus which you own, auditors assign all unclaimed requirements to you.
- Choosing a provider without an AOC - If your hosting provider cannot produce an Attestation of Compliance, they cannot qualify as a compliant service provider under Requirement 12.8.4 - a finding that can invalidate your own assessment.
- Relying on VLAN segmentation alone - VLANs are software-defined and can be misconfigured. Physical isolation at the switch or NIC level provides stronger audit evidence for high-security CDE environments.
- Ignoring data center physical security certifications - PCI Requirement 9 covers physical access controls. Ask specifically for SOC 2 Type II reports on physical security rather than accepting verbal assurances.
- Over-scoping by connecting non-payment systems to CDE servers - Every system with network access to your CDE enters PCI scope. Bare metal makes clean boundaries achievable, but only if you configure network rules deliberately from the start.
Choosing Hosting That Works With Your Compliance Strategy
PCI DSS 4.0 raised the bar for every organization handling payment card data. Bare metal hosting addresses the infrastructure layer directly - clean hardware isolation, full configuration control, and a documented environment that QSAs can assess without untangling shared-tenant complexity.
For most e-commerce, fintech, and payment processing teams, Atlantic.Net's bare metal servers represent a practical starting point: audit-ready infrastructure, managed security add-ons, multiple compliance certifications, and 30+ years of experience with regulated workloads. Your immediate next step is requesting their current AOC and shared responsibility document - those two items clarify exactly what your compliance team inherits versus what you build yourself.
Frequently Asked Questions
Does bare metal hosting guarantee PCI DSS compliance?
No. Bare metal provides the hardware foundation for compliance, but application code, access controls, encryption, and security policies remain your responsibility. A compliant hosting environment reduces scope and audit complexity - it does not replace your compliance program.
What is the difference between PCI-ready hosting and PCI-compliant hosting?
PCI-ready hosting means the provider's infrastructure is built to support PCI DSS requirements. PCI-compliant hosting means the provider holds a current Attestation of Compliance confirmed by an independent QSA. Always request the AOC rather than accepting a marketing claim.
Can I use a cloud VPS instead of bare metal for PCI compliance?
Yes, but it requires more work. Shared virtualized environments create overlapping scopes that complicate CDE definition and demand stronger segmentation documentation. Bare metal simplifies scope and reduces audit time because hardware isolation is inherent to the architecture.
How often does a PCI-compliant hosting environment need to be assessed?
PCI DSS requires annual assessments, quarterly external vulnerability scans by an Approved Scanning Vendor, quarterly internal authenticated scans, and semi-annual access privilege reviews. Your hosting provider's managed security services can support several of these obligations.
What certifications should a PCI-compliant bare metal provider hold?
At minimum, your provider should hold a current PCI DSS AOC and SOC 2 Type II certification for their data centers. For regulated industries, HIPAA BAA capability and ISO 27001 certification add further audit support. Atlantic.Net holds PCI DSS, HIPAA, SOC 2/3, and GDPR-ready certifications across their infrastructure.
What happens if my hosting provider is breached - am I still liable?
Yes. Under PCI DSS, you are responsible for all cardholder data your business processes - even when a breach originates with a service provider. The provider's AOC and shared responsibility document define accountability but do not transfer your legal exposure.

Priya Mervana
 Verified Web Security Experts
Verified Web Security Experts
Priya Mervana is working at SSLInsights.com as a web security expert with over 10 years of experience writing about encryption, SSL certificates, and online privacy. She aims to make complex security topics easily understandable for everyday internet users.